Over the last week or so, in test virtual machines, I’ve been deliberately running malicious software that macOS has detected and removed (‘remediated’). Following yesterday’s assessment of the effectiveness of protection provided by macOS, this article looks at how well the user is informed about malware detections.
Detection
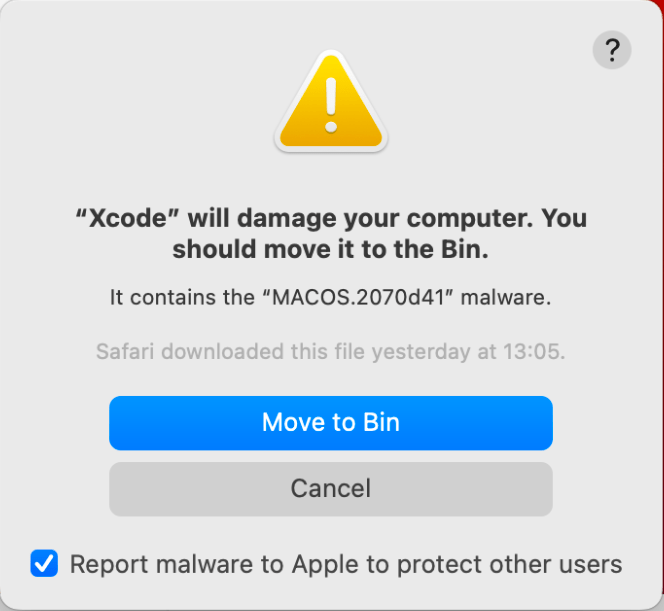
When malware is detected as the user is trying to open or run it, alerts are clear, apart from the terminology used.
It’s some years since Apple referred to malware using regular names. Since then, sources such as the XProtect Yara data file refer to all malware using semi-randomised hex. For example, the alert below cites the name of MACOS.2070d41, which is unique to Apple. This turns out to mean a variant of what’s generally known as XCSSET, which Apple has also previously referred to as DubRobber A.
Other alerts use newer names, in common with codenames used for the scanning modules in XProtect Remediator, such as SnowDrift, although why it has been capitalised in the alert below is a mystery.

SnowDrift refers to what everyone else knows as CloudMensis.
None of Apple’s obscure naming systems informs the user, just leaves them puzzled, and unless they have the presence of mind to take a screenshot, they won’t recall the name shown in the alert.
Apple is in the unique position of being able to agree common terminology with security researchers. It’s high time that Apple fixed this and stopped confusing users.
XProtect Remediator
Detections and remediations by XProtect Remediator aren’t reported to the user in notifications, alerts, or any other overt means of informing them. Instead, they’re written in entries made in the Unified log, and made accessible to apps with access to the Endpoint Security framework. The latter only applies in macOS Ventura, though, which now supports es_event_xp_malware_detected_t and es_event_xp_malware_remediated_t events recording detection and remediation. For ordinary users relying on the utilities bundled in Ventura, this effectively conceals all malware detection and remediation, other than those reported in alerts as shown above.
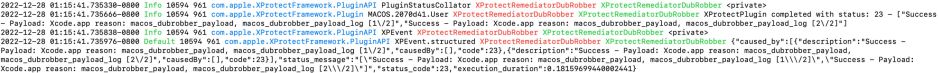
Advanced users with experience of accessing the Unified log can retrieve log entries written by XProtect Remediator’s scanning modules, like those above reporting a successful remediation of DubRobber payload during testing.
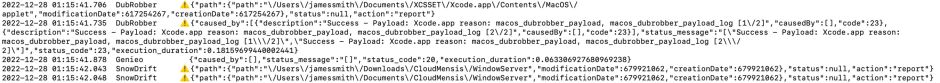
They can also be accessed more readily using my free utility XProCheck. In the excerpt above, DubRobber payload is first detected then remediated, following which two potential detections of CloudMensis (SnowDrift) are reported, but no remediation of those was attempted. To put that more directly, XProtect Remediator discovered two rogue files which it suspects could be malware, but the user wasn’t notified of their presence, and is left none the wiser.
At present, with the exception of the command tool eslogger, macOS contains no app that can monitor Endpoint Security events for the user. Although several third-party security products do use Endpoint Security, few if any detail which events they monitor. As those reporting detections and remediations are only available in macOS Ventura, I have yet to discover any vendor whose products will report es_event_xp_malware_detected_t and es_event_xp_malware_remediated_t events.
Using eslogger isn’t simple either. That tool has to be left running to gather records of events into a text file, which the user has to monitor and maintain. Using the details I published here previously, I gathered those two event types during my tests using malware samples. Each event generates a substantial quantity of JSON data which appears to be undocumented.
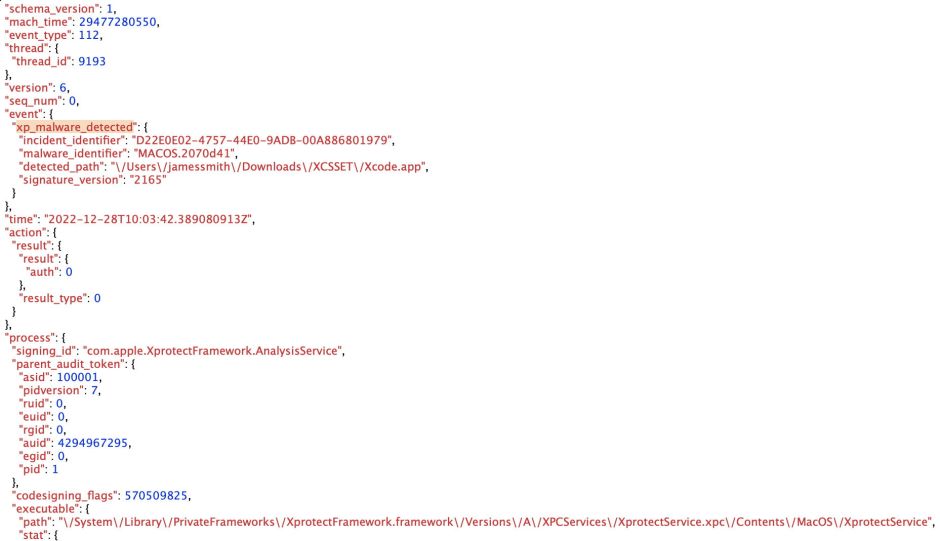
Above is the first half of the data for a single successful detection, in this case not by an XProtect Remediator scan, but by the regular XProtect service.
Summary
Currently:
- Apple uses two different and obscure naming systems for malware, neither of which matches that used by everyone else. These make it harder for users to understand detection alerts.
- In macOS Catalina to Monterey, XProtect Remediator detection and remediation reports are only written in the Unified log, and are therefore inaccessible to the great majority of users.
- In Ventura, detection and remediation reports are also available to Endpoint Security clients. The only client bundled with macOS is a command tool which must be left running at all times if it’s to get events and record them to a log. That isn’t a practical solution for users.
- Although some third-party security products are capable of recording detection and remediation events, it’s not clear which if any do, or whether they alert the user. Most of those products also require significant subscriptions.
- As a result, the great majority of users are oblivious of the detection and remediation of malware on their Macs, which occurs in complete secrecy. The answer to my question in the title of this article is therefore that you don’t know.
