It’s one of the commonest questions I’m asked: can an ordinary Mac user now rely on the security protection provided by macOS Ventura, or do they need third-party extras? The correct answer is that it depends on your security risk assessment, but you also need to know how effective macOS protection is, and where its weaknesses are. In this article I set out to assess how good Ventura 13.1 is when confronted with real malware.
Methods
To investigate this, I prepared three Ventura 13.1 virtual machines, each with different security configurations:
- Apple silicon Full Security mode, with all standard security protection enabled;
- Permissive Security set in Recovery mode, with System Integrity Protection (SIP) disabled;
- Permissive Security with SIP disabled, and the security assessment policy subsystem disabled using
spctl --global-disable.
Settings were confirmed by checking each with SilentKnight, and all tests were virtualised using sandboxed ViableS locked down in isolation from the host Mac Studio M1 Max. Because the malware samples include x86 executables, Rosetta 2 was installed on each VM before testing started.
Samples tested included DazzleSpy, SysJoker, CloudMensis (known by Apple as SnowDrift) and XCSSET (identified by Apple as DubRobber A). As some of the samples lacked an effective installer, and macOS 13.1 has patched most if not all the vulnerabilities they relied on to install successfully, only the XCSSET and DazzleSpy samples appeared able to run and at least partially install themselves. To further aid the malware, tests were also run in each VM with the quarantine flag stripped from Zip archives.
Results
Full Security
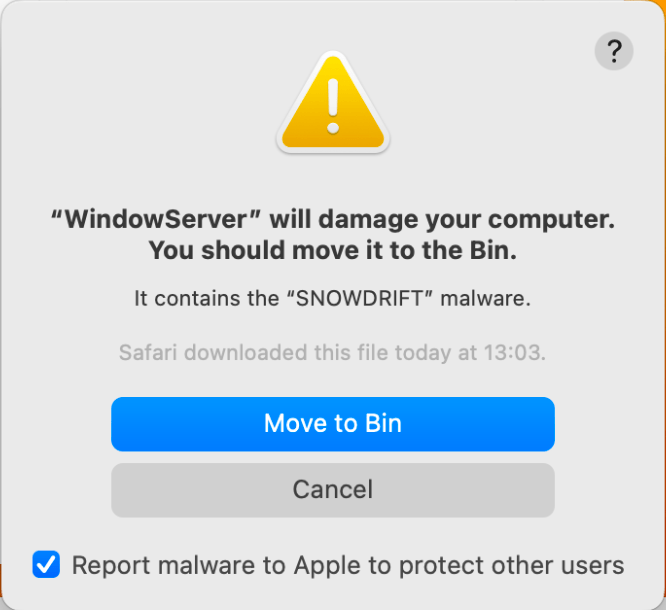
Running with full security enabled, macOS successfully recognised and blocked the samples of CloudMensis and XCSSET, whether or not a quarantine flag was set.

Trying to run the malicious WindowServer component in CloudMensis left the user in no doubt that it was malicious, and gave no option to bypass the block.
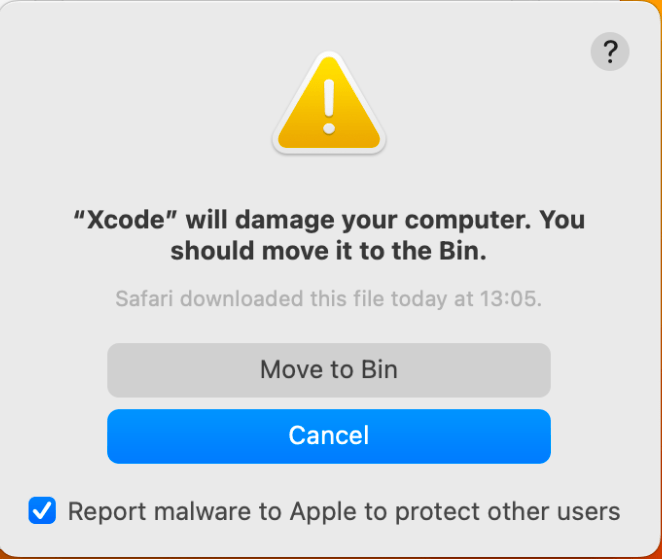
Although in this configuration, the malicious Xcode app in XCSSET wasn’t specifically identified, it was recognised as malicious and blocked effectively.
SysJoker’s bogus MPEG-2 Transport Stream was blocked from being run in QuickTime Player, although the determined user could bypass that, and it wasn’t identified as being malicious.
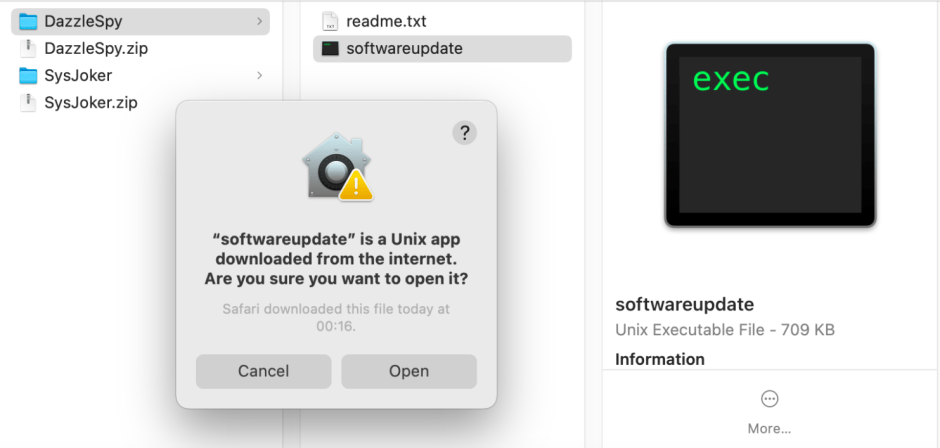
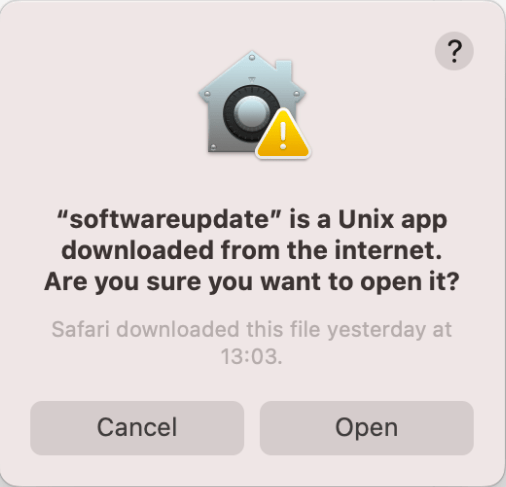
The only warning given on DazzleSpy’s malicious softwareupdate was uncommitted, and left the user with the option to open it. If they chose to proceed, it successfully installed itself in its hidden folder at ~/.local, installed its property list in ~/Library/LaunchAgents for persistence, and macOS automatically added it to System Settings > General > Login Items, although it was left to the user to enable it.

With decompressed samples of malware in ~/Documents, XProtect Remediator scans didn’t result in any reports of suspicious software. However, moving the malicious Xcode app from XCSSET into the /Applications folder was detected and remediated by its deletion.
SIP disabled
This introduced several subtle but significant differences from Full Security, making it less difficult to run malicious code, but also changing XProtect Remediator scans.
The bogus Xcode app in XCSSET was still successfully blocked, but here it was identified as containing MACOS.2070d41 malware, also known by Apple as DubRobber A. It could also be run after stripping its quarantine flag, using the bypass technique of the Finder’s Open command, which was blocked when in Full Security. When its quarantine flag had been stripped, SysJoker’s malicious MPEG-2 Transport Stream was opened and run in QuickTime Player without any warning being shown.
More disturbingly, when macOS installed DazzleSpy’s malicious softwareupdate as a Login Item, it was enabled by default. For a relatively new protection against a well-known method of achieving persistence, that’s a worrying side-effect of disabling SIP.
As if to compensate, XProtect Remediator’s scans appeared more extensive in their coverage. The malicious WindowServer code in CloudMensis was detected and reported when still in ~/Downloads and ~/Documents folders, and DubRobber was both detected and remediated successfully from ~/Documents.
SIP and XProtect disabled
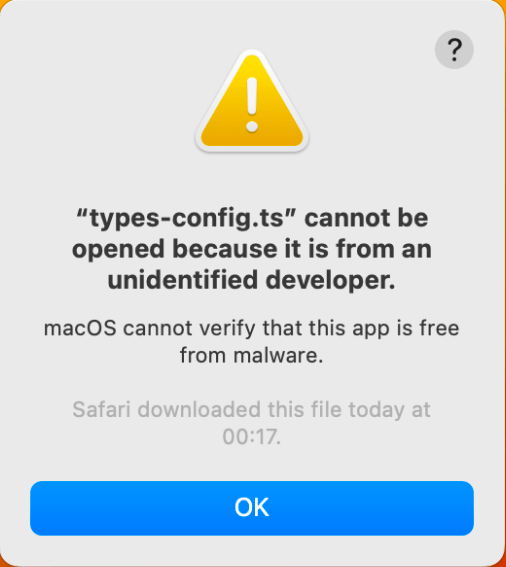
Disabling the security assessment policy subsystem removed most warnings when trying to run malicious software. In most cases, the user was presented with a neutral choice to be made, as to whether the malware should be opened.
The only exception to that was when trying to run the malicious Xcode app in XCSSET, which still resulted in blocking with the warning that it contained MACOS.2070d41 malware, although that could be bypassed by stripping the quarantine flag and using the Finder’s Open command.
XProtect Remediator scans behaved the same as those performed with SIP turned off, detecting WindowServer, and detecting and remediating DubRobber.
Does macOS security protection work?
The effectiveness of the security protection built into current macOS depends on security settings, the malware itself, and the user. With Full Security in force, the only one of the four samples of malware that macOS didn’t block effectively was DazzleSpy. Although that ran and installed without warning, which could have given it persistence, it was left disabled by default.
DazzleSpy is relatively recent malware, and might not present any threat to Mac users who keep their macOS up to date. There has been a lack of detections in the wild, and researchers believe that it may depend on two vulnerabilities that were both fixed in macOS 11.2. Although SysJoker could be opened in QuickTime Player, none of the VMs showed any evidence of its malicious activity, so it too may no longer present any threat to current macOS.
It’s also significant that, with full security protection active in macOS 13.1, stripping quarantine flags didn’t affect detection or blocking of the malware samples. In the past, when Gatekeeper checks were more dependent on the presence of a quarantine flag, methods of avoiding the flag being attached, or of removing it, could bypass most protection. Reducing reliance on quarantine flags makes it significantly harder to install and run malicious software.
Each step away from full security protection reduced the chances of these malware samples being detected and blocked by macOS. The effects of disabling SIP were particularly complex and pervasive. For XCSSET, for instance, it gave the user the opportunity to run its malicious app using a well-known method for bypassing security protection. I suspect that many who disable SIP are unaware of these sinister effects: it’s easy to assume that the robust protection provided by the SSV makes SIP less important to Macs running Big Sur and later.
XProtect Remediator plays an important role in detecting and removing some types of known malware. It relies on heuristics for efficiency, for example minimising the folders it scans, and scan frequency. For much of last summer it ran multiple checks for DubRobber each day, but those have now reduced in frequency, presumably because of a reduction in Apple’s assessment of its threat.
For all malware, the most dangerous period is that between its release and spread, and the release of effective countermeasures, including the patching of exploited vulnerabilities and updates to XProtect and XProtect Remediator. Apple is expected to address the first of those with Rapid Security Responses (RSRs), and for much of the latter half of last year released updates to XProtect Remediator every two weeks. It remains to be seen how they will cope with a major increase in threat from novel malware.
I haven’t considered reporting and monitoring in this article; I’ll look at those separately tomorrow.
Conclusions
- When the current release of macOS is run with Full Security protection enabled, it provides a good level of protection against known malware, which should be sufficient for most users, in accordance with their risk assessments.
- Many factors reduce the effectiveness of macOS security, including running an older version of macOS, disabling SIP, disabling XProtect, and high-risk user behaviour such as using known bypasses, inattention, and clicking through warnings.
- Effective security in Ventura is much less dependent on quarantine. In the past, removing a quarantine flag could enable known malware to run freely. That’s no longer the case in Ventura.
- Ventura, XProtect Remediator and RSR security updates have yet to be tested by a major increase in threat.
Malware samples used were made available to researchers by the Objective-See Foundation. I’d like to thank the Foundation and Patrick Wardle in particular for their generous help.