If you’re wondering whether the new macOS anti-malware scanner XProtect ‘Remediator’ works, here’s a teaser for a fuller account I’m preparing for next week. With the help of a locked-down virtual machine or three, running in my macOS virtualiser app ViableS, I downloaded and ran a sample of XCSSET malware, identified by Apple as MACOS.2070d41 or DubRobber A. XProtect Remediator detected it, and ‘remediated’ it by immediate deletion.
Getting known malware to run in Ventura 13.1 isn’t an easy task. Even when you do your best to bypass its protection, macOS bounces back and blocks you.

In the end, to give the malware a fighting chance of success, I reduced security, disabled SIP, and disabled the security assessment policy subsystem, as reported in detail by SilentKnight.

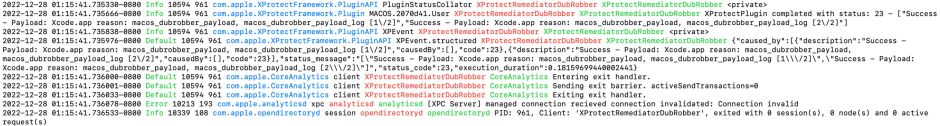
I then ran the malicious fake Xcode app, following which I ran XProtect Remediator in both user and root mode, manually from Terminal. XProCheck reported its detection of the malware, and its immediate remediation by removal of the malicious payload.
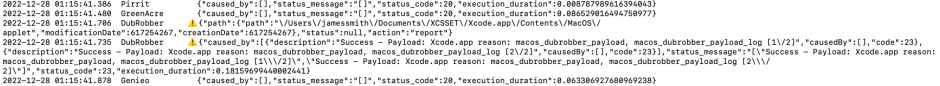
A fuller log extract obtained using Ulbow shows some additional entries.
We’ve already seen some previous examples of possible detections, when XProtect Remediator discovered stray WindowServer files that could indicate the presence of CloudMensis or ‘SnowDrift’, as it’s referred to in XProtect Remediator.
Next week I’ll look more thoroughly at these tests and their results, as well as comparing reporting in the log and through Endpoint Security.
You can obtain ViableS and its siblings Viable (regular macOS, not locked-down) and Liviable (Linux) from their Product Page.
The malware sample used is one of many made available to researchers by the Objective-See Foundation. I’d like to thank the Foundation and Patrick Wardle in particular for their generous help.
