Last week’s big adventure was trying out Passkeys from both Ventura and Monterey 12.6 with Safari 16. Finding suitable sites was an interesting exercise in itself, and I give full credit to Best Buy for leading the pack.
Biometrics
What came as a surprise was trying to use my shiny new Passkey, created in Ventura on an M1 MacBook Pro, from my (Intel) iMac Pro. Although Apple’s limited documentation refers vaguely to alternative methods being provided for Intel Macs, as many lack support for Touch ID, I wasn’t expecting to see this alert.
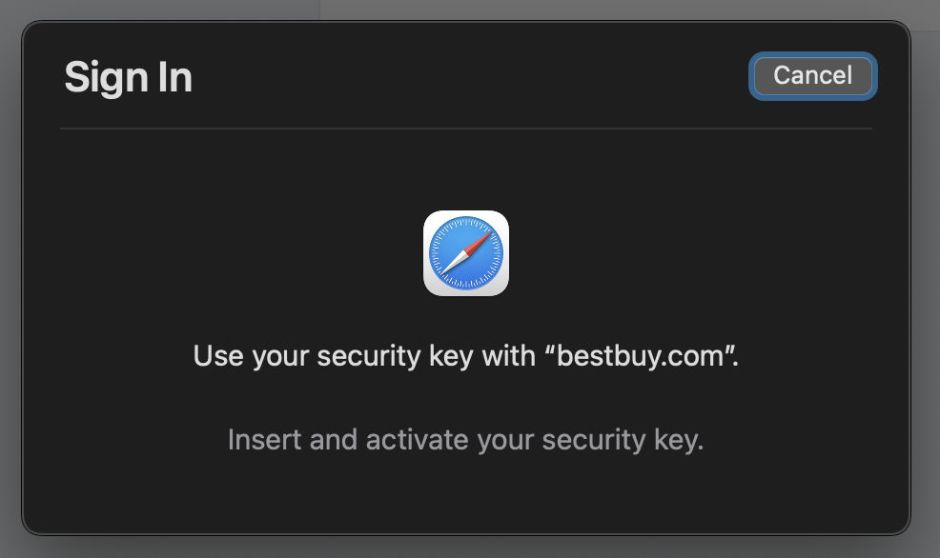
I was so taken aback that, when I wrote the first draft of my article explaining Passkeys, I stated that some form of biometric authentication was going to be required. While there are options available on Intel Macs, such as signing in using your Apple Watch, I can’t believe that those will be necessary. Apple must have better alternatives, surely?
What should have happened is hinted at in the window shown by Safari on an Apple silicon Mac, with support for Touch ID.
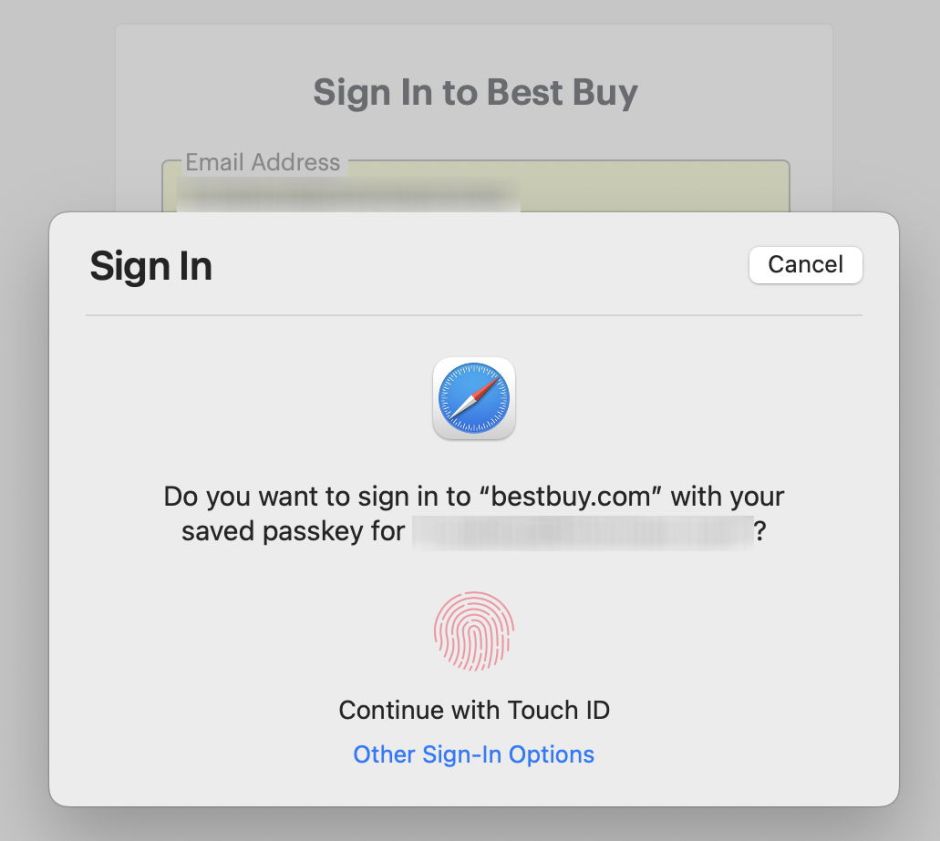
On my iMac Pro, I should have been able to go to Other Sign-In Options, and pick an alternative.
As I keep saying, these are early days for Passkeys. Although the API required to support them is available in Monterey, and I’m fully expecting someone to tell me that they can use them in Safari 15, Apple has announced them as a feature new to Ventura. That might send the message that what we’ve got now in Monterey isn’t as finished as we might wish.
A requirement for full-blown biometric authentication would be severely limiting. While there are third-party systems available, Intel Macs with a T2 chip and its secure enclave don’t all support Touch ID. Apple silicon notebooks all include it in their built-in keyboard, and all Apple silicon Macs are compatible with Apple’s Magic Keyboards with Touch ID. If you have an Intel Mac notebook with a T1 or T2 chip, then its integrated Touch Bar does support Touch ID, but no other Intel Macs, even those with T2 chips, currently have support for it.
Unfortunately those of us who bought M1 Mac minis before Apple released keyboards with Touch ID would have to buy a new and more expensive keyboard to enable Touch ID support. Those first came bundled with the M1 iMac in May 2021, but weren’t available separately until August 2021, a full nine months after the mini started to ship. In any case, according to Apple they’re only compatible with Apple silicon Macs, and can’t be used for Touch ID on any Intel model.
They are also significantly more expensive: the cost difference for an ordinary-size Magic Keyboard is around $/€/£ 50, and for a Magic Keyboard with Numeric Keypad it’s $/€/£ 70. Quite why the additional key is so much more expensive on the larger keyboard defies simple explanation. For Ventura to make Passkeys generally successful, Apple needs to make non-biometric means of using them, accessible to those Macs without Touch ID.
Passwords and Passkeys
The other important matter arising with Passkeys is whether you should use them alongside passwords, or instead of them, a question raised on Twitter and by those commenting here.
Passkeys are nothing if they can’t address the security shortcomings of passwords. If we’re still prone to phishing and the consequences of site breaches, then Passkeys just add another layer of complexity and potential failure. If you leave an account set so that you can access it with either a Passkey or password, then it’s only as secure as the weaker of those two systems, passwords.
Suppose you allowed access to your Amazon account by either method. Then one day you received an email from Amazon informing you that there was a problem with Passkey access, and asking you to click a link and enter your username and password to ensure your Passkey access was enabled again. What better way to steal those credentials before handing you on to your normal Passkey sign-in? Of course, none of us would ever be caught by such an obvious phishing attack, but many would.
As long as you can access that account using a password instead of a Passkey, its security is only as strong as the weaker of the two methods. It’s a good move to leave both available until you have established the reliability of Passkey access on each of your Macs and devices with that particular service. Once you’re happy that it works reliably, go back to your account and disable password authentication completely, so relying on the Passkey alone.
It might seem that you’re doing yourself a favour keeping password access as well. In reality the only person you’re doing a favour to is the one you don’t want to steal your credentials and thereby access your account. They most certainly don’t want you to switch to Passkeys.
