For as long as I can remember, certainly going back to the late 1970s, passwords have been a cornerstone of computer security. In those days, when I logged on to a remote mainframe using a ‘teletype’ terminal, I entered my username and password, just the same as I do now to log on or authenticate to any of my Macs. Steal someone’s username and password, and you can be that person, with all their permissions and privileges.
Over that period, other mechanisms have been devised to replace passwords for authentication. Like Touch ID and Face ID, most are dependent on hardware, and only available on certain systems. Plug-in hardware keys are an alternative widely used in some enterprise environments, but seldom by ordinary users.
Hardware keys generally use pairs of keys generated using cryptographically secure methods, so they’re effectively impossible to crack. The way they work is complex, but in essence what they do is provide the server or service with the public key from the pair, and keep its private key partner secret. The server then challenges for proof of validity, and once that’s been completed accepts that authentication. Public keys alone can’t be used to discover or guess the private key, and the private key is never divulged.
Passkeys essentially work the same as a hardware key, but everything is handled in your Mac’s (or device’s) secure enclave instead.
The advantages to this are great: you don’t need to remember or fetch any passwords, only your username, which should be auto-filled; if a remote server is compromised and your information stolen, it only contains your username and the public key, which can’t give anyone else access to your account; if an attacker tries to phish for your password, they can’t obtain your Passkey, and you know neither of its keys anyway. Passkeys therefore address all the main weaknesses in password-based authentication.
Requirements
Passkeys are now available for use in Monterey and Ventura, as well as iOS 16. To use them, you need:
- Macs to be running macOS 12 or later,
- iOS devices to be running iOS 15 or later,
- iPadOS devices to be running iPadOS 15 or later,
- Safari 16 or another browser/app with Passkey support; although support exists in Safari 15, it doesn’t appear as reliable,
- biometric authentication support, such as Touch ID or Face ID, is a great advantage and may be required for some services/sites,
- Keychain in iCloud for Passkey sharing,
- services with Passkey support.
I haven’t tried macOS 11, as that doesn’t have the API required for Passkey support. I don’t know whether iOS/iPadOS 15, which do have API support, offer Passkeys in Safari or other apps.
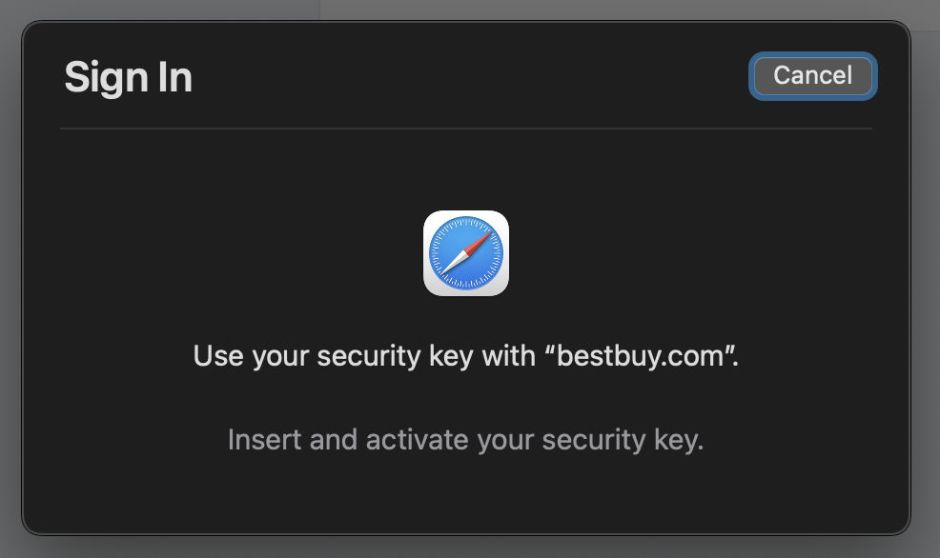
Biometric authentication seems the most reliable, although Apple refers to alternatives being available for Intel Macs which don’t support it. For the moment, if you try to access some Passkey-protected accounts on a Mac without biometric support, Safari might presume that you are using a hardware key, and prompt for that, which gets you nowhere.
Setting up Passkey access
Provided a website or service supports Passkeys and your Mac is compatible, setting them up is straightforward.
Perhaps the most prominent early adopter is Best Buy, which I’ll use for this demonstration. First set up a regular account, if you don’t already have one, with your username and a robust password. Then go to the Account Home page within it, select Account Settings, and Face or Fingerprint Sign-In. When you configure that, Safari’s Passkey setup window will appear.

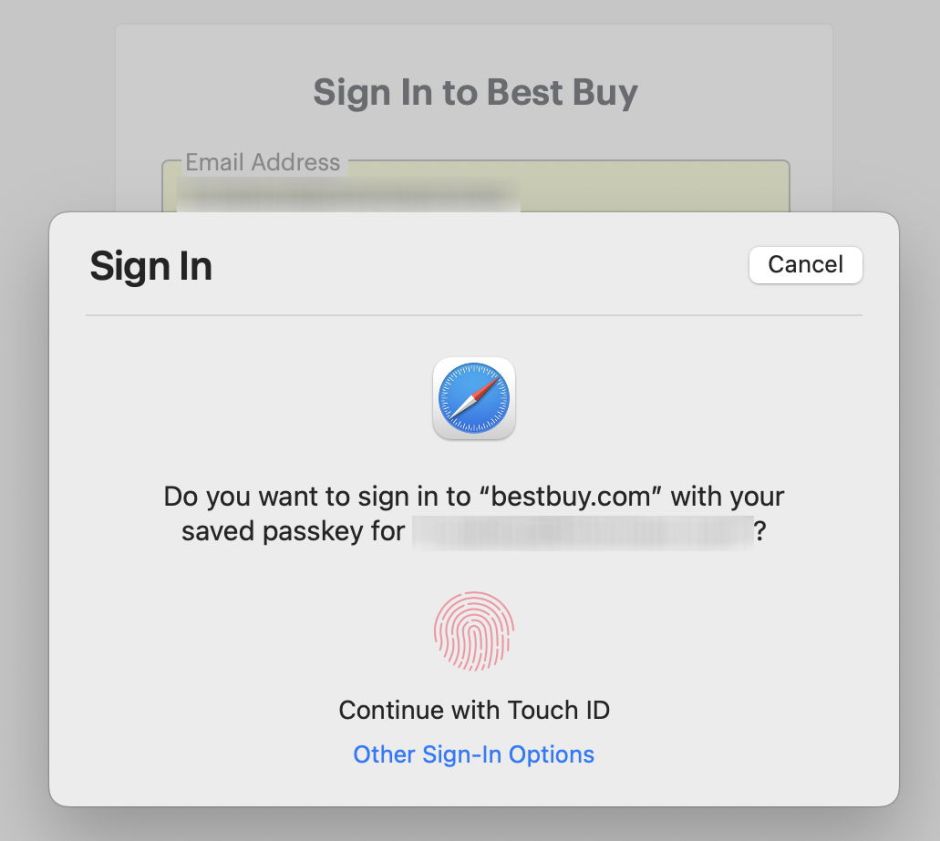
Simply use Touch ID for macOS to create your Passkey and set it up with Best Buy. Then log out and try your new login method. Currently, this is slightly kludgy, in that you first enter your email address as your username, then click on the Sign In with WebAuthn button to log in with your Passkey.
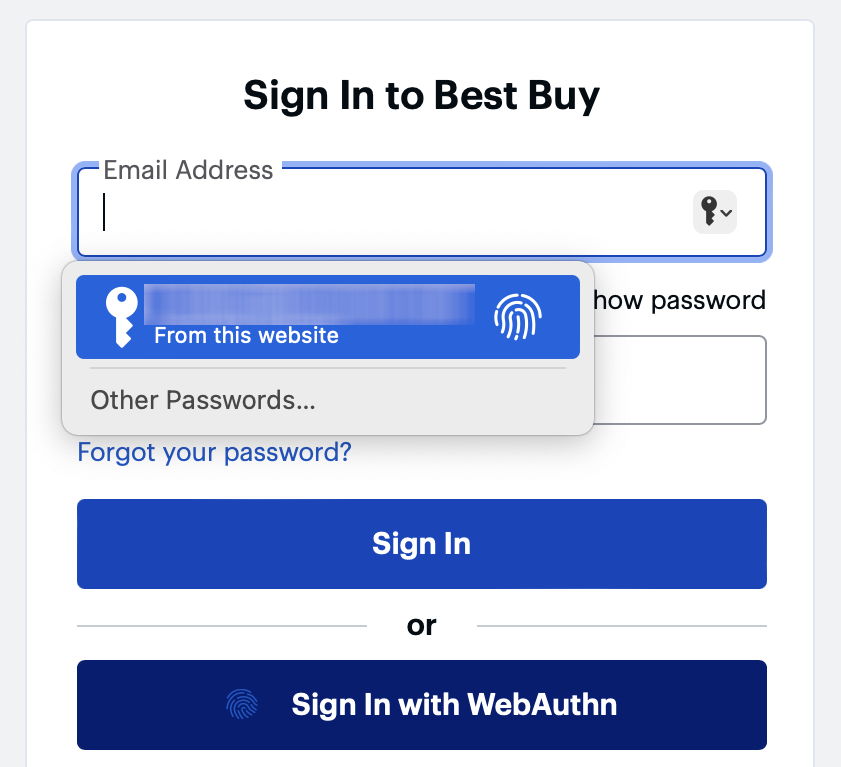
Safari will then invite you to use Touch ID to authenticate with your Passkey.
That’s all there is to it.
These are early days. Until the public release of iOS 16 and Safari 16 on 12 September 2022, Passkeys and hardware keys have been minority pursuits. Now that hundreds of millions of people around the world can readily use Passkeys on their iPhones and Macs, expect this to change rapidly.
Passkeys for 2FA
Although services may not yet offer Passkeys as their primary means of authentication, many more support their use in 2FA. I tested this out with GoDaddy, adding a Passkey as an alternative to a texted PIN to complete 2FA. This is a safe option, as it allows me to provide the second authentication factor by either entering the texted PIN or using the Passkey.
In the Account security page, I selected Security Key as the secondary method for 2-Step Verification. Safari then displayed the window to set a Passkey, which requires Touch ID authentication, following which GoDaddy confirmed that had been successfully set. In this case, I was asked to assign a name to the Passkey.
Checking your Passkey
There isn’t much to check in a Passkey. Both Safari’s Passwords in Preferences and the Passwords pane report that a Passkey has been set for individual accounts, and offer to send them to another Mac or device by AirDrop if you want. Keychain Access doesn’t yet distinguish Passkeys from other keychain contents.
Support for other devices
Apple has shown a method using a QR code which it claims can export a Passkey to a device that can’t share a keychain in iCloud. So far, I haven’t been able to find that feature in macOS or its bundled apps.
