Many users are continuing to report problems trying to connect to some websites, which reportedly have broken certificates. This comes a month after the fiasco with the Let’s Encrypt root certificate, and affects some other root certificate authorities, including IdenTrust. This article explains how you can deal with these and similar problems in both current and older versions of macOS.

Although the exact form and wording of the error varies across different browsers and versions, this is what you’re likely to see in recent versions of Safari. The message means that the browser tried to connect using HTTPS, and has detected a certificate problem.
Do you really want to visit that site?
The big question you then have to answer is whether you really want to continue trying to connect to that site. If you’re not confident that you can trust it, particularly if it’s not that important, the best option is to leave well alone.
If you have good reasons to press this further, the next step is to discover what went wrong by clicking on Show Details.
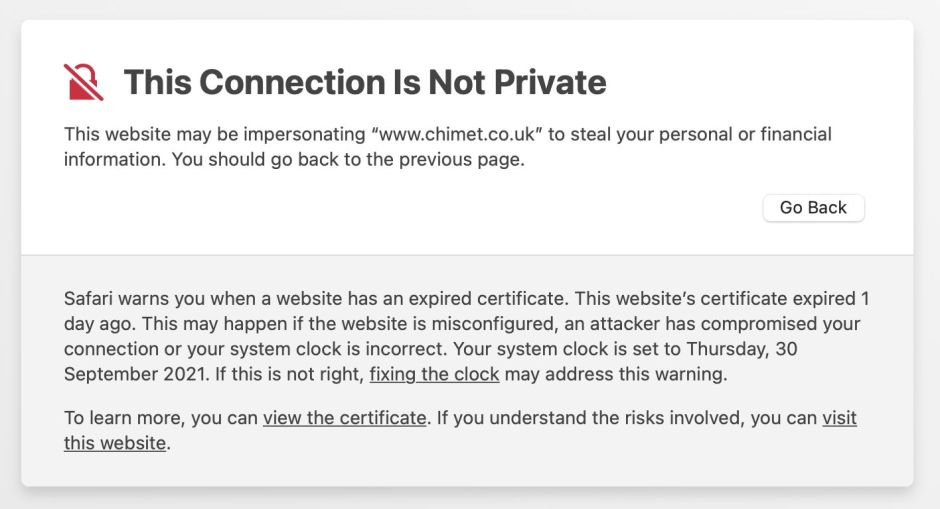
Further information provided by Safari is helpful, explaining the certificate expiry, giving that date and inviting you to check your Mac’s clock. If you’re happy that doesn’t explain the problem, click to view the certificate.

In this case, the site’s certificate remains valid until the end of this year, but the intermediate certificate R3 has expired.
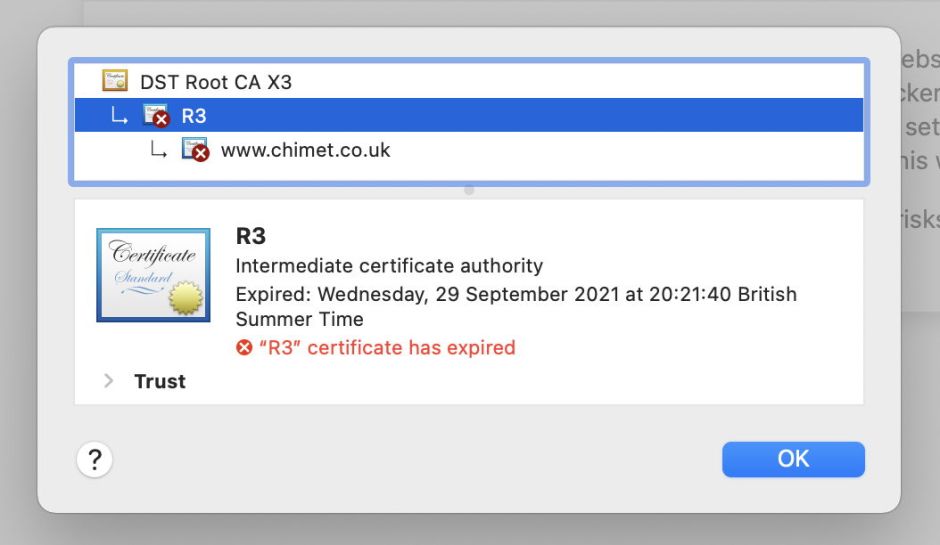
Although this is a Let’s Encrypt certificate chain, the first of the certificates to expire wasn’t its DST Root CA X3, which remained valid at the time that this happened to me. The first to expire was the intermediate R3, which expired on 29 September, a day earlier.
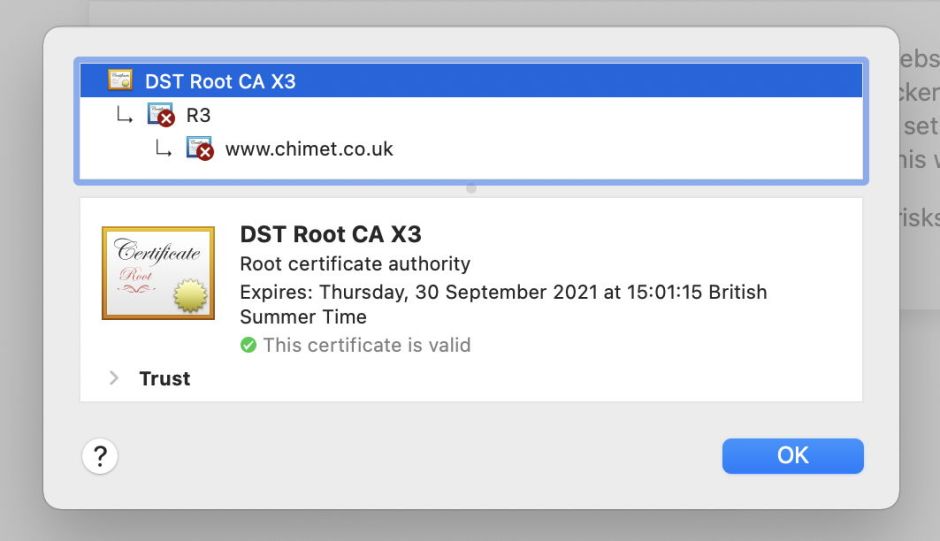
Step back to the Root Certificate, and you’ll see that was due to expire on 30 September, the very next day.
Manual override
If you’re in a rush and just want to connect to that site, and you’re completely confident that it isn’t in the slightest bit malicious, you can manually approve that site’s certificate, which bypasses the expiry of its other certificates. Safari will then add a special certificate to your keychain for that particular site.
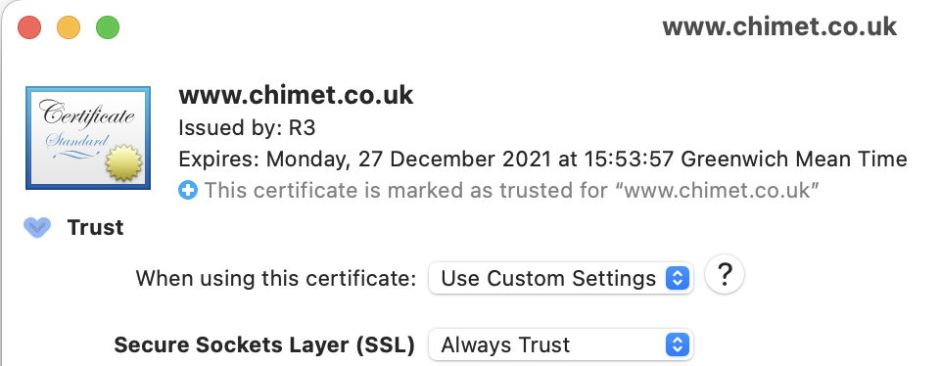
You should only ever do this as a temporary measure. If that site has been or will be hijacked, you’ve just given it a free pass to exploit your Mac. As soon as you can, open the Keychain Access app (in Applications/Utilities), locate that certificate in your Login keychain, and delete it. Even if you use Keychain in iCloud, security certificates like this aren’t shared, but kept in your main Login keychain.
Identify the problem
The next task is to discover what’s going on with those root and intermediate certificates, and the best way to do that is to visit their provider’s website. For Let’s Encrypt, a search should eventually lead you to this article which deals with the certificate expiry. For IdenTrust, you should arrive here. In both cases, links are provided to download the new root certificate, which you should do. They also explain how some older browsers and operating systems may not include those updated root certificates, making manual installation necessary if they’re to be trusted.
Installing a new root certificate
Some browsers, like Firefox, manage their own security certificates, but most, including Safari and Chrome, rely on those installed in your keychains, and for root certificates that normally means those listed in Keychain Access under System Roots, which are installed as part of macOS. For Firefox, follow the instructions given for your installed version to deal with this. For browsers like Safari which use your keychains, you’ll next check whether the updated root certificate is already installed in your Mac’s System Roots.
This is simplest when the root certificate you’ve downloaded is in a format such as PEM which Quick Look can preview and show its details. You can then check whether that’s already installed in your Mac’s System Roots using Keychain Access. Otherwise, you can open the certificate, either in the Finder or import it into Keychain Access and check there. If that root certificate isn’t already listed, you can then add it to your Login keychain and – most important of all – ensure that it’s set to Always Trust. Only ever do that with a certificate you can be confident is worthy of your trust, or once again you’ll be opening your Mac to something very nasty.

Once you’ve done that, try connecting to that website again. If it doesn’t work immediately, you may have to restart, or even start up in Safe mode then restart in regular mode, to ensure that your browser trusts that new root certificate.

Still not fixed?
If this doesn’t bring resolution, the most likely problem is that the site hasn’t configured its certificates correctly, so that they automatically use the new root certificate. In that case, while you can get by and use a temporary bypass, you should contact the site’s administrator and inform them of the site’s problems, so they can fix them at their end.
Protect yourself in future
Having fixed or worked around this problem, you should think seriously about the browser and version of macOS that you’re using.
It’s a common fallacy that if you only ever browse sites you can trust, it’s safe to continue using old browsers and old versions of macOS. You can’t: your browser and security certificates are your front-line defence against all the weapons used by the bad guys. If you’re still fighting with a bow and arrow, what good are they against their rocket attacks? Now is the time to do something about this, and get the best protection by running the latest version of a good browser on a supported version of macOS. If you don’t, it’s only a matter of time before you become a victim.

