What can you do if you try to open an app and macOS refuses on the grounds of a problem with its signature? It’s a question many of us faced recently when the signature on HP printer software was suddenly revoked. A few users tried removing the offending signature, but some found that didn’t help, and were still unable to get the software to function. Does removing a signature work at all?
Before you even consider trying to remove code signatures, you must be certain of the reason for their failure. The most important reason for certificate revocation remains compromise of the certificate’s key, and that may well mean that there’s malware signed with that certificate, waiting to get you. Other reasons for signature failure could well be the result of an attack too; by removing the signature and running that software, you’d then be inviting that malware to do what it wants, which could include encrypting your files and holding you to ransom.
If you’re completely convinced that the signature failure is benign, and you’re prepared to take the risk, yes, you can strip the signature from executable code.
You can try this out in advance. Make a copy of a signed and intact app and make a small change to the Info.plist file inside it. Verify that this renders the app’s signature invalid, as macOS now blocks you from opening that app.
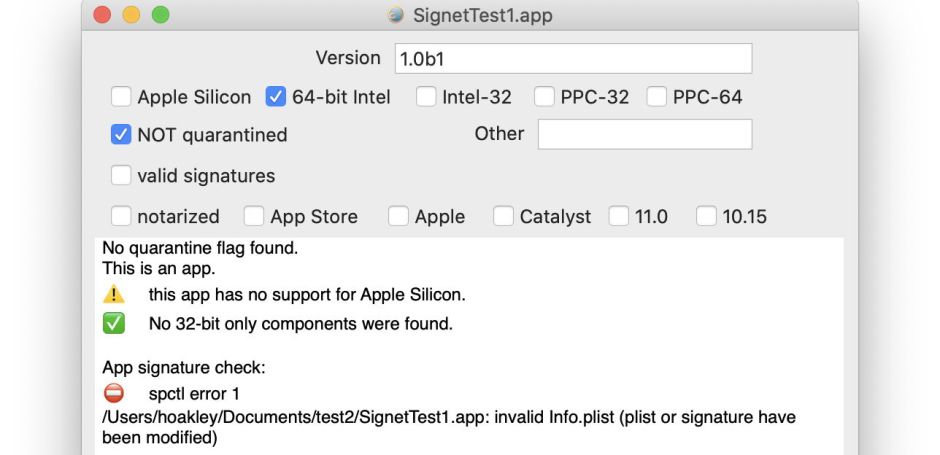
Check the app using ArchiChect and it reports a signing error which no one can get past, unless they know the hidden command in the command tool codesign, which isn’t listed in either its man page or usage info. Simply type
codesign --remove-signature appPath
where appPath is the path to the full name of the app, including its .app extension. codesign will then strip that app’s signature, and you’re done.

That damaged app no longer has a signature, but it still might not run, and could continue to generate signature problems. That shouldn’t happen in this test case, because the reason for it failing signature check is that its Info.plist file has been tampered with. But if the certificate had been revoked, then everything signed with that certificate will now be broken. That includes other executable code within that app’s bundle, such as helper apps and frameworks.
codesign only strips the signature from the app’s executable code in the MacOS folder. Many apps also have executable code tucked away in other places, including the Frameworks folder inside the app bundle. If stripping the code from the app’s main executable doesn’t enable it to run, you’ll need to work through the rest of that and any other supporting code, perhaps in a Library folder, which might be signed, stripping all broken signatures likewise.
That’s why some found that removing the signature from just one app in the many bundles of executable code in HP printer software didn’t work.
One final point for those using Apple Silicon Macs: code which runs native on those has to be signed. So if you strip signatures from ARM binaries, you’ll also have to re-sign them, if necessary using an ad hoc certificate. You then have the pleasure of using codesign all over again.
