Frustrated by the mess of different tools which let you check whether an item’s signing certificates are still valid, I have modified my free utility Taccy to help you check your store of Apple installers and updaters – and anything else which you’re interested in.
You can now drag and drop any Installer package or app onto Taccy, or Open them from its menu, and it will perform a full validation on the item’s signature, as well as all the other checks which it performs. I here show two examples drawn from my library of macOS installers and updaters.
For Mojave, I had earlier downloaded a full installer app named Install macOS Mojave.app using the Software Update pane before Apple updated its certificates.
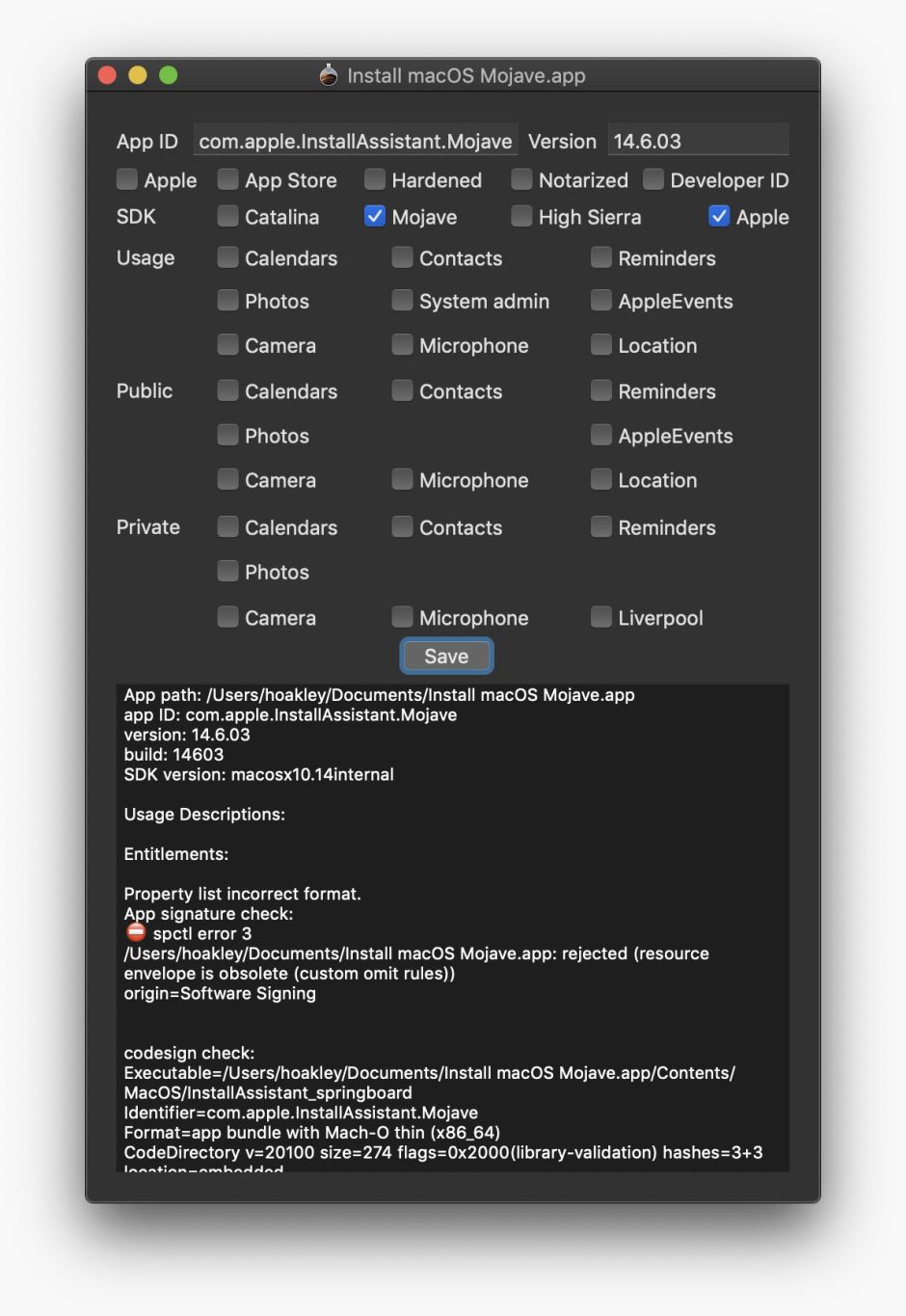
As you can see, in the text in the lower view, the App signature check reports the validation was rejected because “the resource envelope is obsolete”. That is indeed the error returned when you validate its signature by any other means, but it turns out that this is quite normal for Apple’s macOS installer apps, and no indication of whether they are usable, or the certificates have expired.
To check that, you have to examine one of the Installer packages contained within the app itself. In the Finder, select the installer app and use the contextual menu to Show Package Contents. Work down through the Contents folder inside the app to SharedSupport. Within that, you’ll see three disk images, of which one is named InstallESD.pkg. Double-click that to mount it, and within it you’ll see a folder named Packages, containing Installer packages. Check one or more of those using Taccy and this is what you’ll see in an expired installer app:
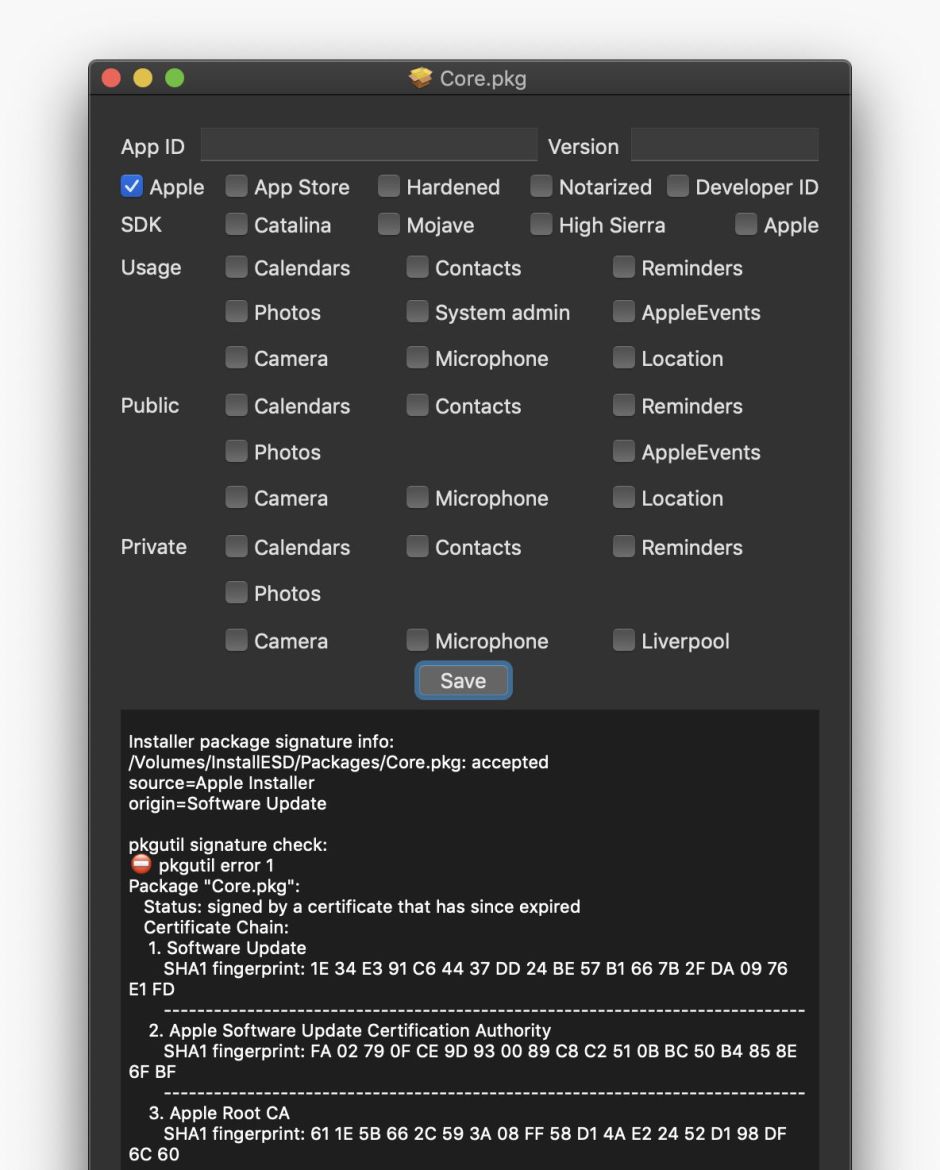
which is the same fatal error seen when you drop an old macOS update Installer package onto Taccy.
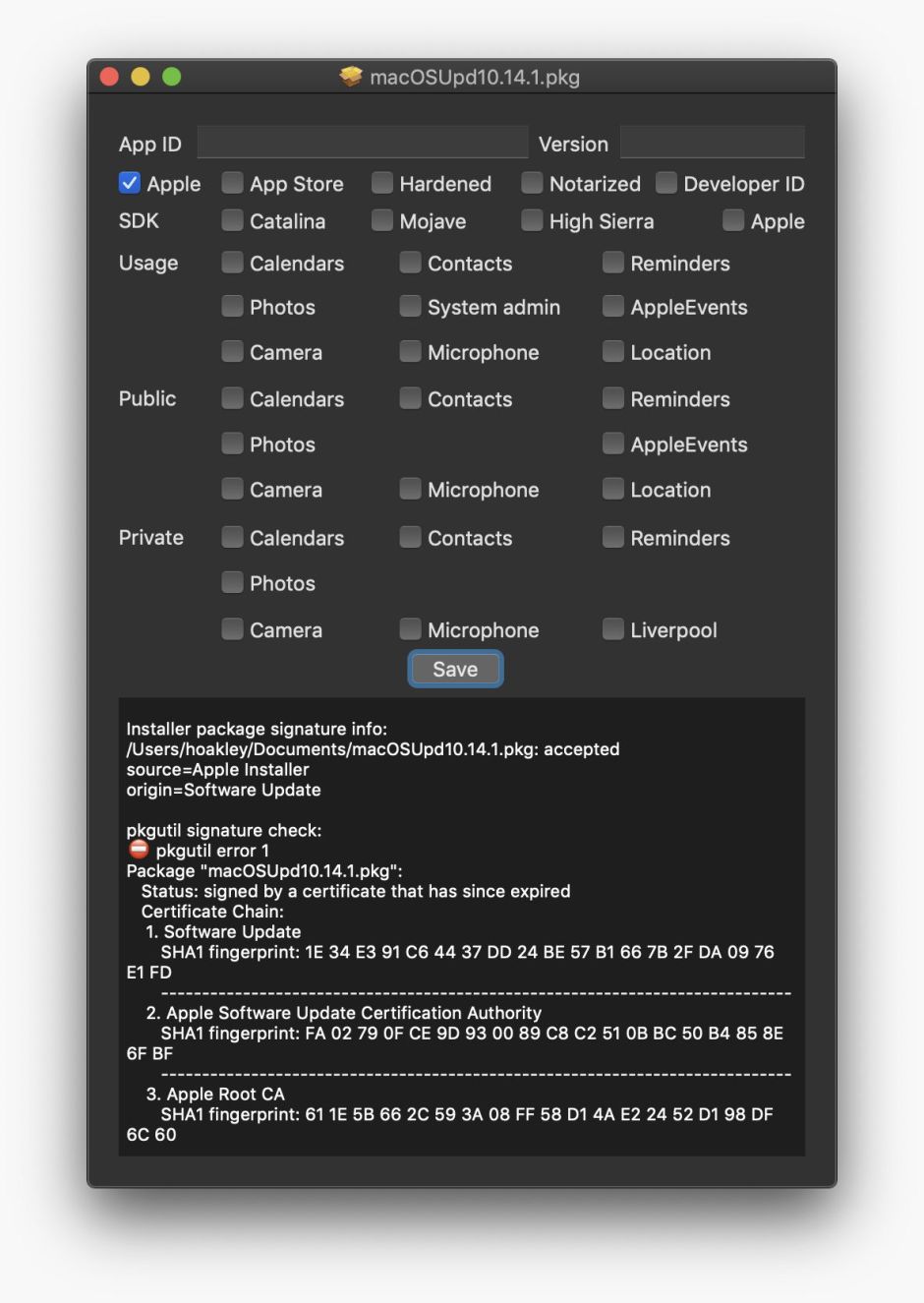
This reports at the top that it has been signed by Apple, but the text in the lower view reveals that its Status is that it is “signed by a certificate that has since expired.” It also reveals the Certificate Chain, in which both the Software Update and Apple Software Update CA certificates have now expired.
Taccy doesn’t (yet) check two types of update: command tools, which are not used standalone by Apple or any major vendor as far as I know, and disk images themselves, which invariably contain either an Installer package or app which can be checked now using Taccy.
Taccy version 1.6 (which is even better) is now available from here: taccy16
from Downloads above, from its Product Page, and through its auto-update feature.
I am very grateful to comments from John and Nort which finally guided me to this answer. Perhaps we should have expected Apple’s own installers not to pass Apple’s own signature checks even when they work!
