One extraordinary bug in High Sierra 10.13 which has come to light is that, if you are not careful, using an APFS encrypted volume provides no protection at all. When someone tries to mount that volume and is prompted for its password, they can read it in what should have been the password hint.
This bug was first reported by Matheus Mariano over a week ago, and has since been confirmed by anyone who has tried to reproduce it, including me. If you have a system running High Sierra on an APFS disk, and a minute to spare, work through this with me now.
Note that this bug has been fixed by the High Sierra Supplemental Update of 5 October 2017, in Disk Utility version version 17.0 build 1626.
Demonstration
Open Disk Utility, and select your startup APFS container/volume at the left. Then click on the Volume tool just above it to add a new volume to it. APFS is much more flexible over volumes, and can add many more without taking any real disk space, so adding another here doesn’t affect your current startup volume at all.
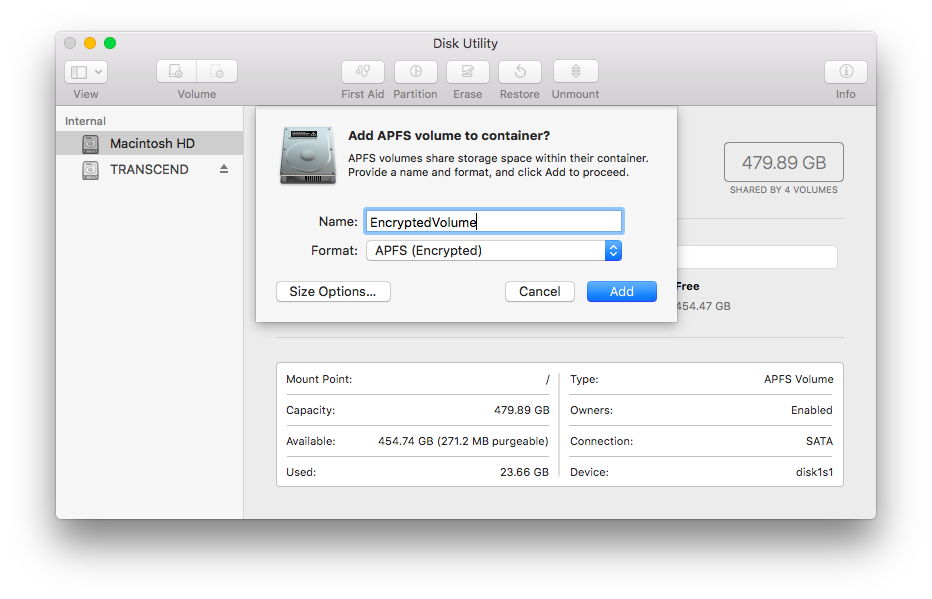
Disk Utility drops a sheet down, into which you should give a volume name such as EncryptedVolume, then select APFS (Encrypted) as its Format.
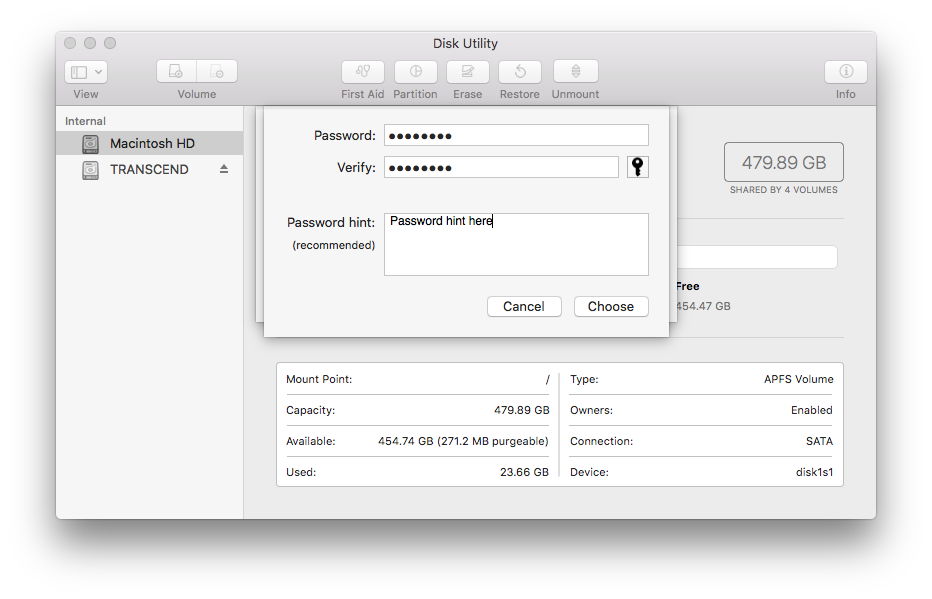
That drops another sheet down, into which you should give a password such as password, and type a different password hint, such as Password hint here. Then click on the Choose button.
Your encrypted APFS volume is then created. Select it at the left, and use the File/Unmount command to eject it. Then select its greyed entry again, and use the File/Mount command to mount the encrypted volume.
As it is encrypted, in order to mount it you have to enter its password. Up pops the password entry dialog. Click on the Show Hint button and the hint shown will not be the text which you entered as the hint, but the volume’s password.

This makes the encryption a complete waste of time, as it protects nothing.
Workaround
So how can you use an encrypted volume safely in High Sierra 10.13?
If you are already using encrypted volumes, you should be able to work around this bug by changing the password on each.
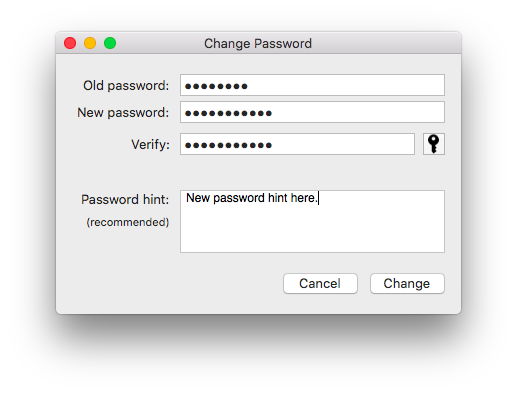
Strangely, when you do that, the plain text stored as the hint is actually the hint, and not the password itself.

Michael Tsai’s blog reports some other quirks. If you don’t enter a hint at all, then the password isn’t stored as the hint, and it appears to be safe. This behaviour only occurs when you add a new volume to an existing container. When you format a disk with its first volume in APFS (Encrypted), it does not occur.
Security implications
If you have added APFS encrypted volumes in the manner which can trigger this bug, unmount and remount them, and check if the password for that volume is given as the hint. If it is, change the password for that volume immediately, which should ensure the new password is properly protected.
If you are intending to use encrypted volumes in High Sierra, work around the bug if you must, for example by not giving a hint at all, or by changing the password before use.
Where is this bug: in APFS?
There is no evidence that this bug is in APFS, or even in macOS, but it appears confined to one short section of code in Disk Utility. At one point in that code, instead of saving the hint as the hint, the code saves the password itself, in plain text.
Is APFS encryption secure?
There is no evidence that APFS encrypted volumes are not fully secure. However, it is now known that in certain circumstances they can leak passwords.
If you want a high level of assurance that encrypted files are secure, you are probably better off not using High Sierra’s encryption for the moment. The fact that this bug made it through code review, regression testing, beta-testing, and into the release version of High Sierra suggests glaring inadequacies in each of those steps. Your security auditors may take a dim view of High Sierra for a few versions to come yet.
Fixing affected volumes
If you have APFS encrypted volumes, it is particularly important that you apply the High Sierra Supplemental Update as soon as possible. This replaces the flawed version of Disk Utility and its supporting tools and fixes the bug. However, it does not remove the password from the hint given for any volume affected by this bug.
What you should do next, to secure your encrypted volumes, depends on whether you consider the password on an encrypted volume might have been compromised. If you are using them on a laptop to protect data in the event of that laptop’s loss or theft, and the laptop has remained secure, you may consider that the passwords are still secure. In that case, changing the password to clear the hint may be sufficient.
If there is any possibility that those passwords might have been compromised, then changing the passwords now will not change the underlying encryption of the volumes, leaving them vulnerable. You will need to back the data up from all affected volumes, reformat them, setting them first to APFS and then APFS (Encrypted) format, and assign them new passwords. Apple details how to do this using Disk Utility in this article.
(Updated 6 October 2017 following Supplemental Update.)
