Last year there was a lot of fuss and some bluster about embarrassing photos of certain celebrities which hackers had gained access to, in some cases apparently through their Cloud accounts. No doubt the next such incidents are not too far away. Even though images of you may not be as sought after, it is a wakeup call which should make us all sharpen up our Cloud security.
iOS devices may not be computers, but the moment that you start using one, or connect a Mac to iCloud, you need to think computer security.
In the excitement of the store where you tried or bought your iPhone and/or iPad, it all seemed deceptively simple: enter your Apple ID and password (something easy to remember alongside your device and card PINs, and other vital items), and all your apps, images, and stuff are there, wherever and whenever you want them.
Unlike secure corporate Cloud services, iCloud and most other consumer remote storage is not designed or intended to protect data to the standard required by, for example, the Data Protection Act. Would you not be justifiably outraged to discover that your doctor or solicitor was storing your personal records in their iCloud account? If not secure enough for those purposes, you must think carefully and critically what information and files you can trust to the various remote storage services such as iCloud.
Consumer cloud services should be assumed to be only as secure as your password, and only as well protected as that password is. Additional forms of protection, such as iCloud’s ‘two-step verification’, should be seen as a bonus, and not relied upon to safeguard sensitive information. Apple makes it clear that two-step verification does not cover images, other documents, backups, or anything else stored in your iCloud allocation, and more robust authentication schemes of that kind will probably prove too intrusive for everyday data access.
Making cloud services truly secure, as for corporate or government use, requires additional layers which would be too complex or inconvenient for consumer use, particularly with a plethora of mobile devices. Requirements commonly include virtual private networking (VPN), encryption, fixed IP addresses, authentication using hardware devices such as USB ‘dongles’, frequent forced password changes, and enforcement of strong passwords based on random strings. Although we may see some of these, and other security enhancements, offered in the wake of recent breaches, the only way to enjoy their full protection is with a heavyweight corporate service.
Two simple changes that all consumer cloud users can make to significantly increase their security are to change their Apple ID to a private email address, and to change to a really robust password which you do not use for anything else.
There are a lot of evil people out there trying to break into iCloud and other accounts. The first piece of information that they need is your Apple ID. If it is the same as the email address which you use for public services, such as online forums and social media, then it is easy for them to harvest that and use it. Try Googling yourself and see which email addresses appear in the results: if one of those is your Apple ID, you now know how easy it is for others to obtain it.

You should already know how to create a password which is almost impossible to guess, mixing upper and lower case letters, numerals, and non-alphanumerics in at least eight, preferably ten or more, characters. Further details are here.
Make your Apple account password unique to that account, completely different from the passwords that you use for other online services, and unrelated to anything in your Facebook and other accessible profiles. And despite the many offers from every quarter, never store that password on or with anything which could readily be lost or stolen, such as an iPhone, iPad, or laptop.
Finally, think twice before putting any data or documents into cloud storage. Ask yourself whether they could be damaging or dangerous in the hands of others. If you need to secure Cloud data properly, further details are here.
Technique: Control your content
Perhaps the most obvious lesson from the theft of embarrassing images is to know what is stored on cloud services that you use. Although this can be easier in Yosemite, Mavericks and earlier provide only hidden indirect methods for listing iCloud contents, depending on the type of data being stored. You can always browse documents stored by individual apps, such as the iWork suite, from the Open File dialog within each app.
To browse the bulk of the documents stored in your iCloud account, open the iCloud Drive item which should be listed in your Favorites in a Finder window.
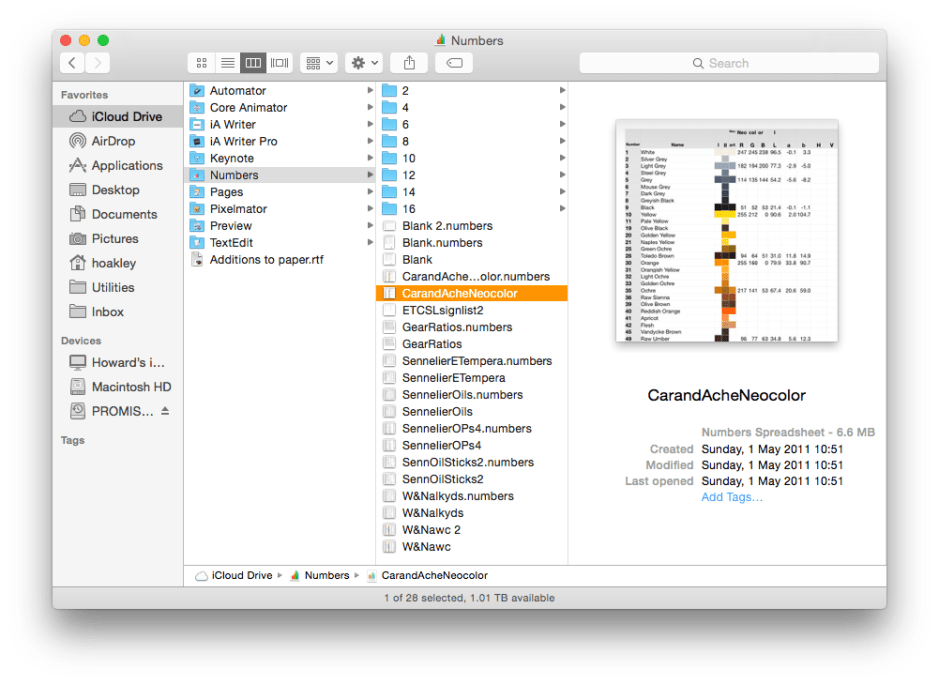 If that is not shown and cannot be enabled, hold the Option key and select the Library command in the Finder’s Go menu, to open the Library in your Home folder. There open and browse the Mobile Documents folder, where iCloud content is listed by the app which owns it. The Finder helpfully puts the iCloud icon at the bottom left of the window when you select a folder or its contents to remind you that this is stored remotely. Selecting a document within an app folder starts its download, and a progress bar appears.
If that is not shown and cannot be enabled, hold the Option key and select the Library command in the Finder’s Go menu, to open the Library in your Home folder. There open and browse the Mobile Documents folder, where iCloud content is listed by the app which owns it. The Finder helpfully puts the iCloud icon at the bottom left of the window when you select a folder or its contents to remind you that this is stored remotely. Selecting a document within an app folder starts its download, and a progress bar appears.
Other specific iCloud content, such as Contacts, Calendars, and images, is shown in the relevant app, with local indications such as those detailing photo streams being kept inside Photos, iPhoto and Aperture libraries.
Updated from the original, which was first published in MacUser volume 30 issue 12, 2014.

