Everywhere that you go you need user names, passwords, and other means of proving your identity. In OS X and iOS these are normally stored in a keychain.
Whatever you want to do with your Mac, iPhone, or iPad, you need to prove who you are using authentication. Although there are alternatives based on physical devices or biometrics, such as the Touch ID system built into the most recent iOS devices, from first logging on to shutting down, this normally means a succession of user names and passwords. Whether you are connecting to Facebook or paying the Inland Revenue online, many things in life demand authentication.
In early versions of Unix, user names and passwords were stored in a weakly protected text table. Hackers quickly learned that once you managed to steal that table, it was only a matter of time before you could decrypt its passwords, and they were then able do whatever they liked on that system.
As Mac OS was becoming better geared to multi-user and network use, back in the days of System 8.6, Apple realised that there needed to be a better repository of authentication information, the keychain. This was originally intended for use in Apple’s email system PowerTalk, to enable you to connect to a range of different mail servers and work with several mail accounts. It was then incorporated into OS X as a generic system service, open to all applications.
Keychains
A keychain – and OS X and iOS routinely handle multiple keychains – is simply a container in which passwords and other sensitive information are kept in encrypted form. When OS X, iOS, or an application requires details for authentication, such as when a website prompts you to enter your user name and password, this can be looked up in the keychain and automatically passed to complete the authentication process without your having to type everything in from memory.
Keychains store more than just user names and passwords. They also hold copies of security certificates that are used to verify the authenticity of sites and services, cryptographic keys that you might use in encryption tools such as X, and text notes (in OS X, not iOS) that you can add arbitrarily, perhaps containing the answers to security challenge questions, or similar.
Only passwords, keys, and the contents of notes are held in encrypted form within the keychain, but the method used to encrypt them (TripleDES) is extremely resistant to attack; whilst the professionals in national security agencies might be able to break into them, even a highly skilled hacker cannot. Note that certificates are not encrypted, but remain accessible.
Macs and iOS devices always have multiple keychains, which can be open simultaneously. OS X keeps these in the Keychains folders in your Home Library folder, in the top-level Library, and libraries of certificates and some other system-related information in /System/Library.
Generally speaking those specific to each user are kept in their personal keychains in their Home Library, whilst those required for all users are kept in the Library folders accessible to all users. Servers also keep keychains in the Network Library folder, for access by networked clients.
iOS is different, as it keeps its apps running apart from one another in ‘sandboxes’, limiting their access to shared facilities as much as possible. So each iOS app has its own separate keychain, and cannot access those owned by other apps: hence password details stored by the iOS version of Safari should not be available to other apps that might have web access, for example.
Apple’s Keychain is a trade-marked implementation built on the open source Common Data Security Architecture (CDSA), and its interface Common Security Services Manager (CSSM), but those are not universally supported on other systems.
Access
Conforming Mac applications, such as Apple’s Mail and Safari, enjoy full access to keychains: log onto most sites using Safari, and it will store and recall your user name and password, just as it will also try to autocomplete web forms, when set to do so. Not all sites permit that, and sometimes Safari does not recognise prompts for authentication made on a different page from that which Keychain is used to.
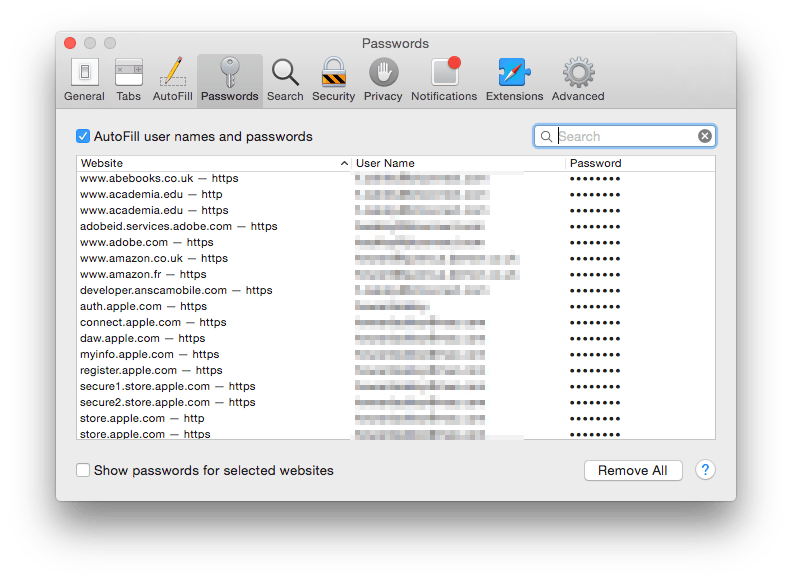
Recent versions of Safari also allow you to view and edit your passwords which are being stored in your keychain, through the Passwords tool in Safari’s Preferences, which saves you from having to open Keychain Access.
Your default personal keychain is named ‘login’, and as that suggests, is opened when you first log into that account on your Mac. Once opened, any application or service can request passwords and other information from that keychain without your further authentication. However once the keychain is locked, encrypted information in it is only accessible when you have authenticated again by entering your user name and password.
In normal circumstances, requests for protected information in a keychain should only come from trusted software. However if a hacker gains access to your Mac or iOS device, perhaps by getting a Trojan onto it, that could easily try to steal passwords from keychains. Accordingly it is good security practice to keep keychains locked as much of the time as possible. Then any Trojan that tries to access passwords will have to prompt you to enter your user name and password, which should trigger your suspicions and let you refuse their request.
Security
By default, the password used to authenticate for access to encrypted information in a keychain is the normal password used to log onto OS X. You can change the keychain access password independently of those for users, and another good way of increasing the security of your system is to require a different and even stronger password for keychain access.
OS X uses Access Control Lists (ACLs, the same as those used for extended file permissions in the Finder) to protect individual items within a keychain. These also list those applications that are trusted to access each encrypted item in the keychain.
Thus, if Safari is one of the trusted applications for your online banking password, and your keychain is left unlocked, when you log onto the online service using Safari you will not be prompted to authenticate in any way. If your keychain is set to lock itself automatically, you will be prompted for your user name and password before Safari can unlock the keychain and complete your user name and password.
If an untrusted application tries to obtain the password for your online banking service from your keychain, even if the keychain is left unlocked, you will be prompted with a dialog asking you if you wish to grant it permission to access that item in your keychain. If the keychain is unlocked you will not be asked to authenticate, but that dialog is intended to provide an additional layer of protection from malware, for instance.
Information stored in your keychain is important, and needs to be carefully backed up. Policies differ between OS X and iOS: Macs that use Time Machine or other tools to keep backups of the contents of Library folders automatically back up the keychains stored there. However iOS devices do not include keychains in their backups performed through iTunes.
Either way it is most important that you keep independent records of all important access and other details that should be stored in your keychains. Accidental corruption is unusual, but does occur; keychains are a potential target for destructive malware, and clumsy efforts to break into them could lead to damage.
In the cloud
Now that many of us have two or more devices which connect to iCloud, Apple has added a cloud-based keychain service to iCloud. When you use iCloud Keychain in Mavericks or Yosemite, all your other trusted Macs and iOS devices running 7.0.3 or later can access the same authentication information. This includes login details for websites, passwords to access WiFi networks, and credit card details, although it stops short of providing any CVV information.

This can be a great help, but makes your security even more dependent on the security of your iCloud connections. If your iCloud password is easily guessed, then it makes all your other passwords easy to acquire. There is also the (hopefully theoretical) risk that a more general iCloud hack could yield your keychain information, but that should be next to impossible.
Armed with this understanding of how keychains work, you should be able to keep your Mac and iOS devices more secure, and cope with occasional glitches.
Tool: Keychain Access
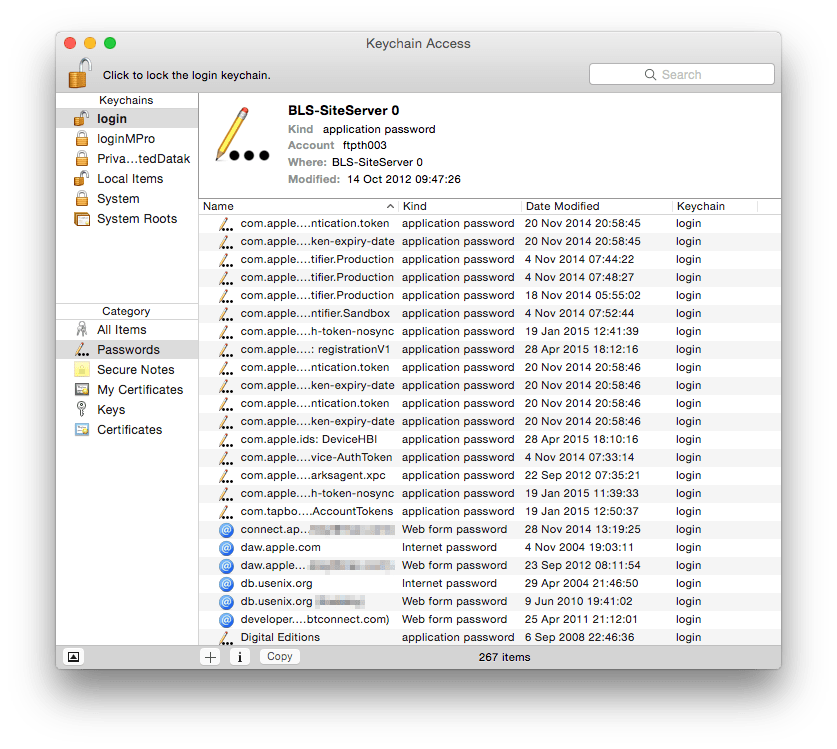
Keychain Access, in the Utilities folder in your main Applications folder, is the one-stop tool for checking, editing, and controlling entries in OS X keychains. When opened it gives you choice between all the different keychains that it is aware of on your Mac, in the top left of its window, different classes of item stored in each chain below that, then a listing of those items in the main area.

If you have forgotten a user name and password, and it has not been autocompleted by Safari or another application bearing the prompt, locate the site or service in the list of Passwords, and double-click on it to view its settings. You may then need to authenticate to unlock the keychain before you can view the password that has been set. Use similar processes to change details, such as when you start using a new password, and to clear away expired certificates, passwords, and the like. Store sensitive text information in encrypted form as a note, if you wish.
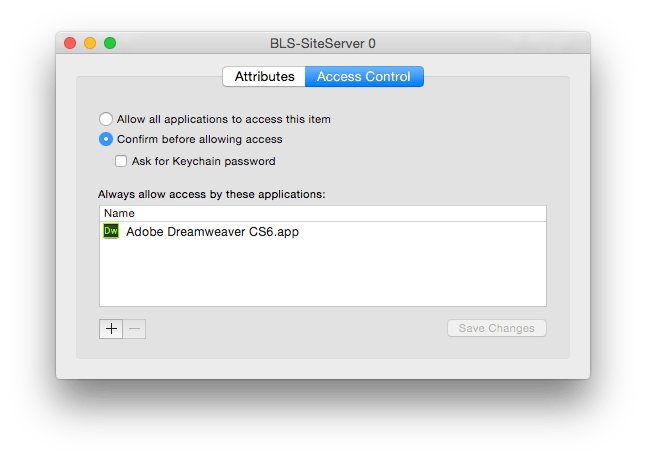
You can also view which applications are set to have instant access to each item in a keychain, by opening the item and clicking on the Access Control tab. This does not prevent other applications from being able to gain access, but you will be prompted to permit this, either as a one-off or to add the application to that Access Control List (ACL).
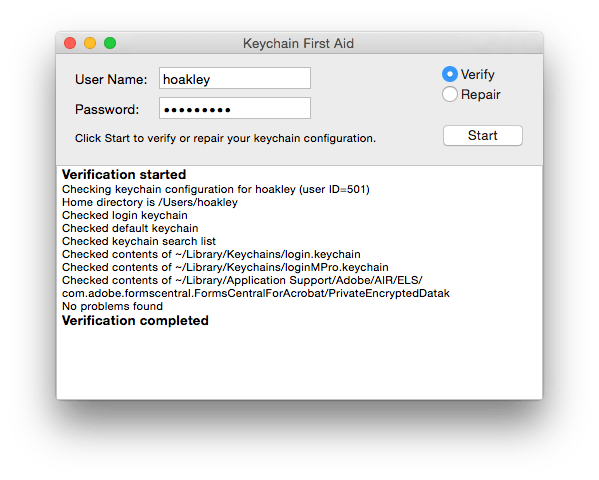
Keychain First Aid used to be a separate utility, but the ability to check the integrity of a keychain and repair it if necessary has now been rolled into the single application, accessed through its entry in the Keychain Access menu. You can also use its padlock icon to lock your keychain immediately, and preference settings to force automatic locking, for additional security.
Technique: Robust Passwords
Your security is only as good as the passwords that you use. If they are easy for potential intruders and online criminals to guess – and you would be shocked at how many people still use ‘password’ – then your account(s) will be compromised and your identity could be stolen too. Be very wary of using the same password for different services and systems: if one becomes compromised and your details stolen, a criminal could use that to gain access to your other accounts, such as online banking.
One of the main purposes of keychains is to allow you to use a rich range of passwords that cannot be broken easily, but which would be more difficult for you to remember and have to keep typing in manually. It includes an excellent service to suggest and test the strength of different passwords, Password Assistant.
Password Assistant is launched whenever you click on its special key icon, normally found in the right of any system dialog that prompts you to create a new or edit an existing password. An easy way of gaining access to it is to open a password item in Keychain Assistant, where its icon is then shown immediately after the password.
Passwords can be suggested according to several different criteria, of which the most useful is generally the Memorable option. Try to make their length 12 characters or more, and never use any password that is shorter than eight.

Most people can think of more memorable passwords that contain combinations of small and capital letters, digits, and non-standard characters such as punctuation marks, rating highly in Password Assistant’s strength indicator. Avoid using words that could be discovered from a dictionary search, which includes most personal and place names, as that is a common strategy to break passwords.
Updated from the original, which was first published in MacUser volume 28 issue 12, 2012.