Yosemite’s iCloud Drive has drawn even more of our documents and data into the Cloud. But what if our data has personal or sensitive content?
Last year the general news media highlighted, often in alarmist terms, a long succession of computer security problems, from Heartbleed to the Gameover ZeuS botnet, and seemingly endless breaches of security. Among those, the British Pregnancy Advisory Service, a charity, was fined £200,000 because it had failed to adequately protect sensitive personal data on nearly 10,000 individuals from the criminal activities of a hacker. So far this year has been no better.
At the same time, Apple and others are enticing us to use their Cloud services. Yosemite brought iCloud Drive, letting us store almost any documents or files remotely, and developers are being encouraged to build in support using CloudKit. Linked with iOS 8, it is so much easier to work on documents shared between iOS and OS X systems.
If you only ever use your iOS devices and Macs for personal matters, and the most sensitive information contained on them are your Contacts or about you, then the security of those data are your personal concern.
DPA
The moment that you start holding customer or client information, especially if it contains bank or financial details, or other personal data about individuals, and particularly if this is part of a business or other enterprise, this comes within the scope of the Data Protection Act (DPA).
The Information Commissioner’s office offers here sector-specific guides and aids that advise businesses how to keep on the right side of that law, and have produced guidance on Cloud computing here.
Information that is covered by the DPA must be stored in compliance with the law, and this raises several issues over services such as iCloud. For practical purposes, Cloud storage must remain within the countries of the European Economic Area, or the USA provided that the service provides comparable protection for rights, and freedom of access by those whose data is stored.
One simple way to achieve the latter is for the service to be approved under the Safe Harbor scheme; a list of such approved services is here. Unfortunately at present Cloud services including iCloud are not, generally, included in that scheme. For the time being, at least, an organisation would need an explicit contract with a provider of Cloud services before it could become demonstrably acceptable under the DPA.
If this seems disproportionate, consider whether you would be happy knowing that your personal medical or financial records were held in someone’s iCloud account. Also note iCloud’s current terms and conditions of service here, notably the statement: “APPLE DOES NOT REPRESENT OR GUARANTEE THAT THE SERVICE WILL BE FREE FROM LOSS, CORRUPTION, ATTACK, VIRUSES, INTERFERENCE, HACKING, OR OTHER SECURITY INTRUSION, AND APPLE DISCLAIMS ANY LIABILITY RELATING THERETO.”
As with other services, one of iCloud’s strongest selling points is ubiquity of access. Even when you are at a customer’s site on another continent, you can enjoy as full access to data stored in the Cloud as you would have when back in your own office.
But before you start browsing sensitive information when sat outside a cafe in Rome, you must think seriously about who might be reading your screen from the table behind, and who might have hacked into that WiFi network. iOS 8 does improve the privacy afforded over WiFi connections, but they remain a significant concern.
You should also remember the high penalties imposed on those whose data is stolen, or left behind by accident – not just in terms of the fine from the Information Commissioner, but also the impact on your business reputation. We would hate to read about your case in the news media.
FileMaker Pro
Databases like FileMaker Pro offer robust security with user authentication and associated privileges, which are a good basis for DPA compliance. Although configured through friendly dialogs, you must takes pains to ensure that everyone is assigned and uses their own unique user identity, and that their privileges are the minimum necessary. Privilege sets are a great time saver, and you will normally find it best to work out standard sets for different work roles alongside database design.
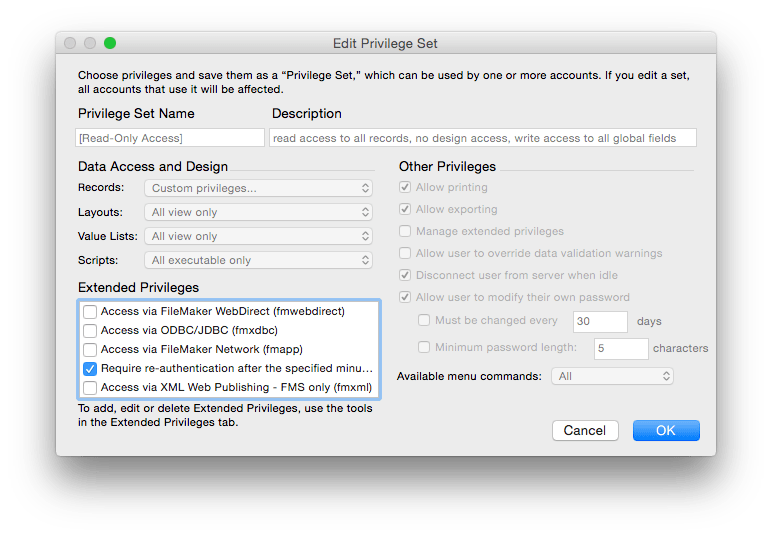
Worked through carefully, FileMaker Pro and Server provide extremely fine granularity of control down to fields within individual records. This can be strengthened by good database design, by keeping personal identifiers in a separate table to which only selected users have access.

If you use FileMaker Pro to access external data sources, for example through ODBC, consider carefully whether those external data could be copied across to the client. Unintentional leakage of sensitive data to a remote system might then become accessible to an intruder on that remote system; this is particularly important when clients could be ill-secured home or laptop computers, or mobile devices. Whilst FileMaker Go can be exceptionally powerful for iOS deployment, it requires attention to physical and network security.
Updated from the original, which was first published in MacUser volume 30 issue 09, 2014.
