Controlling access to and the ability to change files is one of the fundamental tasks of all operating systems like macOS. It’s not only required for security and privacy, but to maintain order and stability. Unfortunately, it has now become complex, and as a result can block you from performing simple tasks that you should be able to do, like saving one of your own documents. This article tries to disentangle some of the different systems to help you tackle their problems.
Permissions
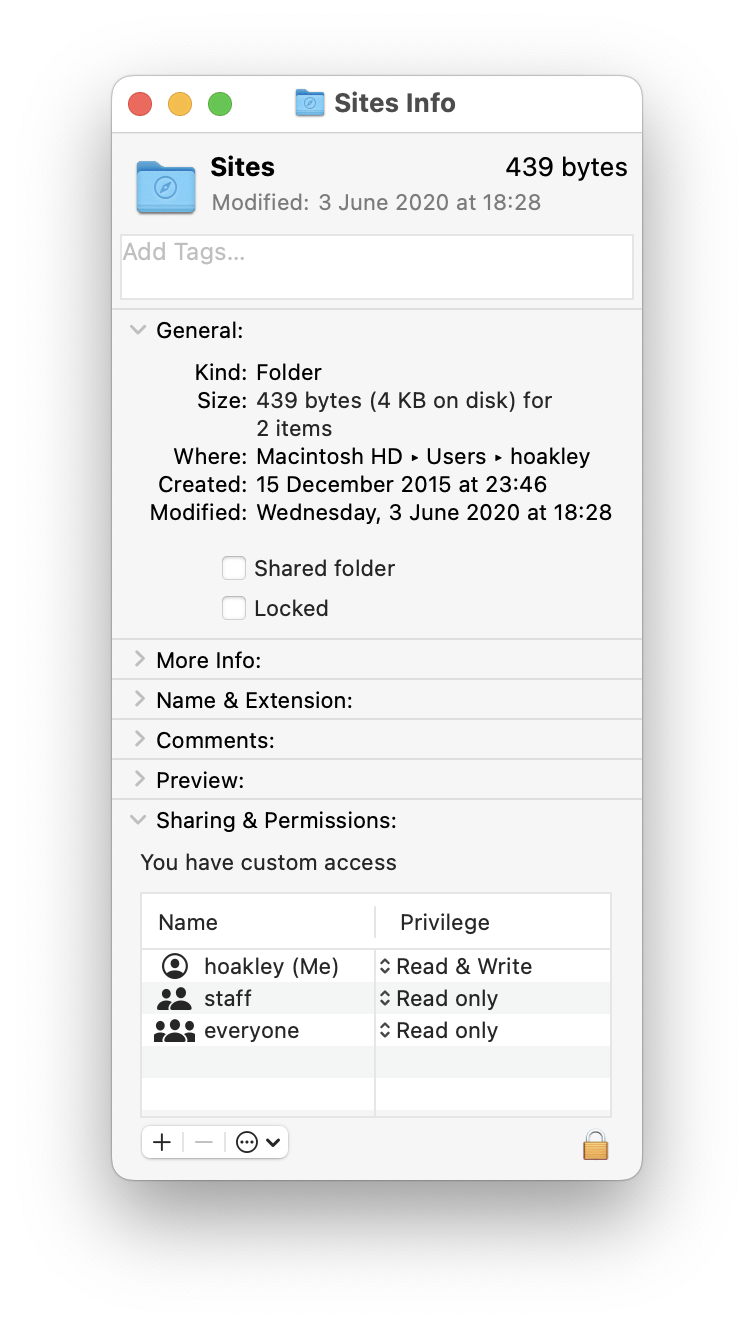
These are the simplest and most basic, and can be inspected and changed in the Finder’s Get Info dialog for all accessible files and folders. They control the ability of apps and other code to read and write each file and folder. Normally, if you’re the named owner of a file or folder, you expect to have both read and write access, and that ensures that the apps you use can open, edit and save changed files. There’s also the Locked checkbox that might seem obvious, although it often gets overlooked as a cause of problems saving a file.
Some locations are particularly sensitive to errors in permissions, such as all those property lists containing settings for apps and services, stored in ~/Library/Preferences. They are mostly handled by a background service cfprefsd, but if permissions have become changed so that it can’t access a property list it needs to use, all sorts of strange errors can result.
A few years ago, this was frequent enough to be a recognised problem, and Apple provided a series of support notes and tools to deal with it. Since then, incorrect permissions have become rare, and Apple has withdrawn its advice. If you really feel that your Home folder has incorrect permissions, then read this article carefully before trying to correct them. It isn’t as simple as you might think.
ACLs
Access Control Lists, ACLs, add a more sophisticated system for enforcing more specific restrictions that cover a wide range of features. In yesterday’s article I showed how they can be used to prevent quarantine flags from being attached to downloaded files, quite a sinister feature. Their only common use in modern macOS is to preserve standard structures of folders in the Home folder. Regular Posix permissions don’t do that at all well, so a common ACL used is
group:everyone deny delete
that prevents anyone from deleting the folder to which it’s applied.
You should find that ACL on each named user folder and the Guest folder in /Users. Within each user folder, it’s normally applied to all the standard folders, including Desktop, Documents, Downloads, Library, Movies, Music, Pictures, Public and Sites.
Within each user’s Library folder, it’s normally found on: Application Support, Assistants, Audio, Caches, ColorPickers, Colors, Compositions, Favorites, FontCollections, Fonts, iMovie, Input Methods, Internet Plug-Ins, Keyboard Layouts, Logs, PreferencePanes, Preferences, Printers, Screen Savers, Services, Sounds, Spelling and Voices.
The result of that ACL is that any attempt to remove that folder fails silently, so preserving the standard layout. But it doesn’t affect access given to the contents of those folders, and can’t be held responsible for errors when trying to read or write files within a protected folder. Unfortunately, the Finder’s Get Info dialog isn’t exactly forthcoming about the presence or effects of ACLs, merely stating that the user has “custom access”.
Thankfully, some GUI tools give good access to ACLs, and my favourite remains TinkerTool System, which has excellent support for them, and much more besides.
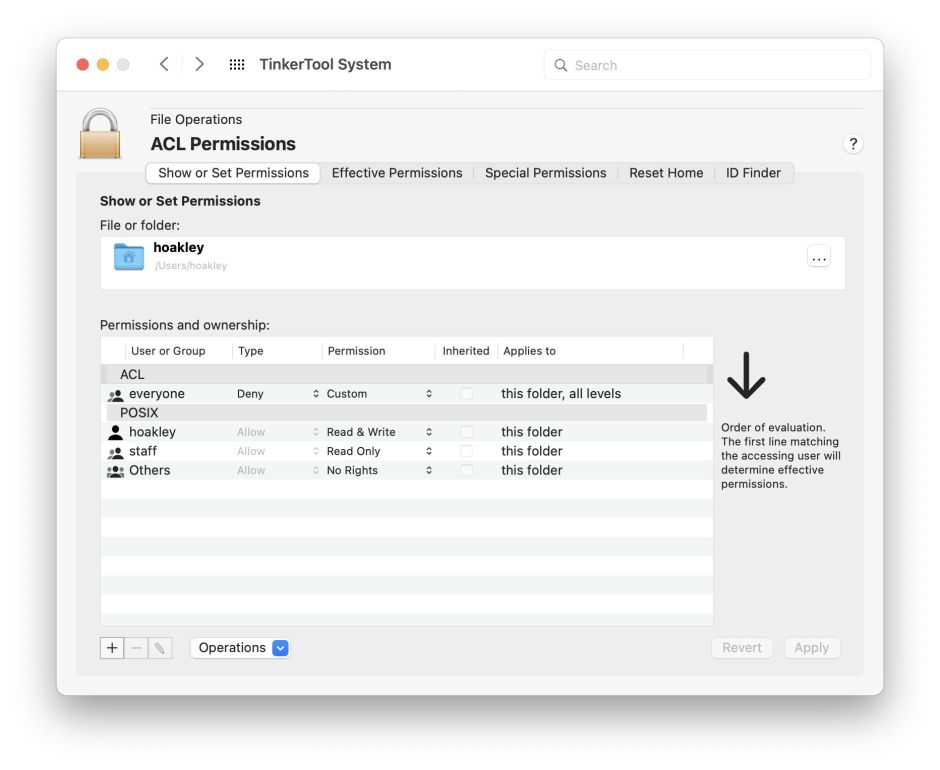
Use its Show or Set Permissions view to inspect any item to see whether it has an ACL, and to edit it if necessary.
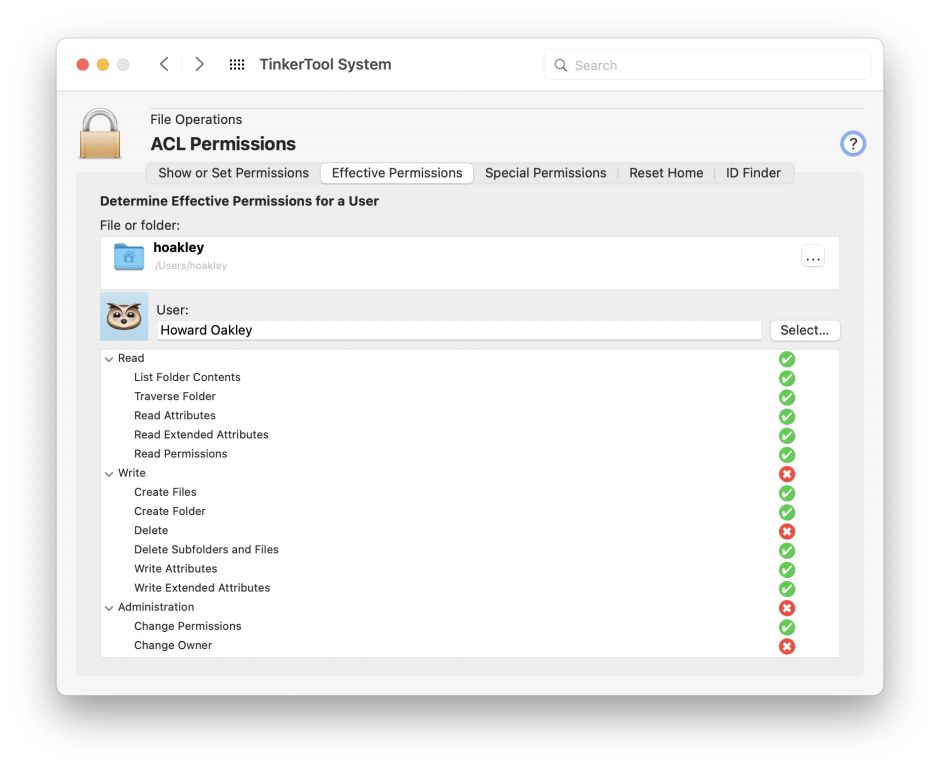
Where TinkerTool System is invaluable is displaying Effective Permissions. Drop the item at the top, select any user from its popup menu, and the ticks and crosses show exactly what that user can and can’t do according to the ACLs and permissions set.
Otherwise, the only built-in tools are those in Terminal. Show all ACLs using the command ls -le, which should return entries such as
drwx------@ 5 hoakley staff 160 27 Mar 22:53 Desktop
0: group:everyone deny delete
drwx------@ 84 hoakley staff 2688 9 Apr 21:06 Documents
0: group:everyone deny delete
You can add an ACL using chmod, such as
chmod +a "everyone deny delete" MyFolder
Privacy protection
macOS designates certain locations and resources as being private, and protects them using its Transparency, Consent and Control (TCC) system. Among the folders that this protects are the Desktop, Documents, Downloads, and removable storage. While access to individual folders has fine control, if you do encounter problems it’s usually simplest to add that app to the list of those with Full Disk Access, in Privacy & Security settings, in the first instance. That can leave a lot of apps with unnecessary access to private data, so you should periodically check through the list of apps with Full Disk Access to check that they all still require it. Note that Full Disk Access can’t override permissions or ACLs.
SIP and security
In principle, System Integrity Protection (SIP) should only apply to system files, but it’s also used to lock down some other components, including com.apple.macl extended attributes, which can be attached to user files. Those have been implicated in some problems in which regular user documents become locked down, and typically won’t save any changes. Although the exact role and use of this extended attribute isn’t yet clear, it’s generally accepted as designating an app that’s approved to edit that file, so providing document-specific privacy control.
com.apple.macl extended attributes are normally protected by the same mechanism that applies SIP, so any attempt to remove them is likely to fail. One workaround for that is to pass the file through another volume, so that when it’s copied back the extended attribute is no longer protected, and can be stripped.
These problems appear most likely when apps other than that set as the default app to open a document type are used to edit files. Another approach to their solution is to select an affected document in the Finder, Get Info, set it to Open with the default app, then click on Change All… to reset all others to that default app. Another helpful tool is lsappinfo.
macOS now attaches quarantine flags of type com.apple.quarantine to many documents, although in few cases does this appear to be the cause of any problems. As they’re not protected, they can be removed, provided that you’re confident that the document isn’t in any way malicious.
Correcting errors
We all like instant solutions, and the promise of a command that will simply fix all file access problems like magic. Because of the different systems involved, from permissions to undocumented extended attributes, there can be no single solution. The first step is to discover the cause of a problem, which should lead you to know which controls you need to fix. Without that, you’re reduced to guesswork and pain.
Thanks to MrChad for reminding me to draw attention to those embarrassing times that saving a file has failed because it was locked (see comment below).
