The Isle of Wight, where I live, has many puzzles, like a Lake where there’s only dry land, Freshwater that’s surrounded by sea, and Cowes where there are mostly yachts. This article presents two conundrums from macOS: an APFS (Encrypted) volume that isn’t encrypted, and an unencrypted volume with FileVault active.
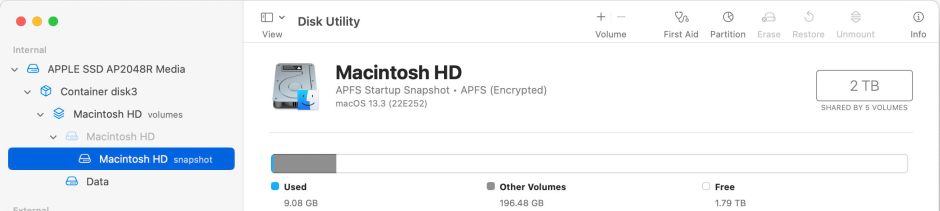
These start with snooping on the internal disk of an Apple silicon Mac using Disk Utility. Select the boot snapshot (SSV), and read how Disk Utility describes it being in APFS (Encrypted) format.
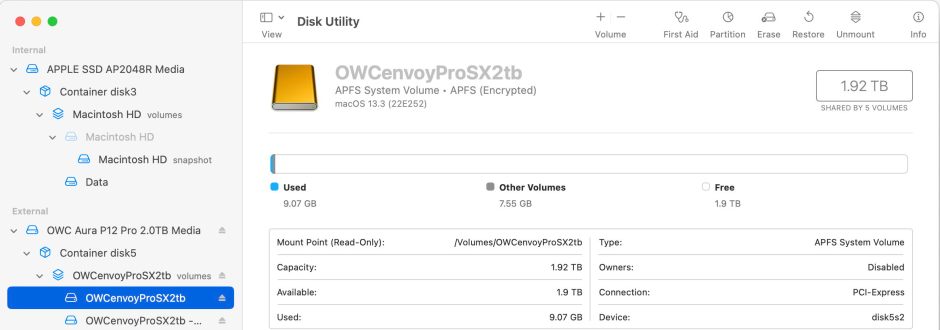
Not only that, but it claims the same is true of the System volume on a bootable external disk, although admittedly that too has FileVault enabled on its Data volume.
Reach for Terminal and try
diskutil apfs list
to disambiguate, and you’ll come away more confused: the Data volume on that external disk does have FileVault active and is unlocked, but the System volume also has FileVault active and isn’t encrypted at all.

So, just which volumes in the Boot Volume Group are encrypted, and which aren’t?
Platform Security Guide
Apple’s definitive statement on each of the volumes in the Boot Volume Group (BVG) is found in its Platform Security Guide, where it gives the following:
- disk3s1 Macintosh HD, the System volume, is unmounted and contains the snapshot SSV, which in macOS 11 and later is unencrypted;
- disk3s2 Preboot, is unencrypted;
- disk3s3 Recovery, the paired Recovery volume, is unencrypted;
- disk3s4 Update, isn’t mentioned;
- disk3s5 Data (named Macintosh HD – Data in Intel), the Data volume, is encrypted and may additionally have FileVault active;
- disk3s6 VM, is unencrypted.
So the only volume within the BVG that is encrypted and can have FileVault enabled is the Data volume.
diskutil
If you get information from the diskutil command tool, you’ll see that the only volume for which it doesn’t give encryption status if disk3s5, the only one that Apple states is encrypted, but FileVault is reported as being Yes on both the System and Data volumes. However, disk3s1, the System volume, is reported as being unencrypted.
APFS
Each time that APFS mounts a volume, it reports its encryption status. During a normal, Full Security boot on an Apple silicon Mac, all six of the standard volumes on the BVG are mounted, and the only one reported by APFS as being encrypted is the Data volume. The System volume and mounted SSV snapshot are both reported in the log as being unencrypted, for example
disk3s1 vol-uuid: [UUID] block size: 4096 block count: 487113810 (unencrypted; flags: 0x201; features: 21.0.12)
disk3s5 vol-uuid: [UUID] block size: 4096 block count: 487113810 (encrypted; flags: 0x100; features: 41.0.2)
What’s correct?
Without wishing to deepen the conundrum, all these answers are correct: the System volume isn’t itself encrypted, but it can only be mounted when FileVault has been unlocked, because of the firmlinks that splice the Data volume into it. I still don’t think I’d express this the way that Disk Utility does, but it has a point.
Now, did I tell you about the Needles you can’t sew with, or Ryde where you walk?
