Over the last ten days we’ve had two significant updates to macOS malware protection. As Apple has at last decided to revert to using plain rather than obfuscated names for the new malware these protect against, I thought it might be worthwhile to review how those updates affect us.
The first of the two updates brought XProtect to version 2166 on 22 February. This added four new detections, covering KeySteal A and three variants of Honkbox. These should now be detected and blocked immediately if you were to try running any of those on your Mac.
The second update brought XProtect Remediator to version 91 on 2 March. This added two new scanner modules for KeySteal and something named BadGacha, whose identity and nature remains unknown outside Apple, for the moment at least. These should enable periodic scans to detect and remove KeySteal and whatever BadGacha might be.
KeySteal
Although this first appeared at least a couple of years ago, it seems to have reappeared last autumn/fall, and has been described in full detail by Luis Magisa and Qi Sun of Trend Micro. It has been found as a malicious version of the ResignTool app, used to change code signatures. As its name implies, it mines for keychains and exfiltrates their contents, so could make off with very sensitive information. It may well be correctly signed, and in one case was presented in an Installer package that had the correct type of Developer Distribution signature for that.
Like all successful malware, it achieves persistence, in this case using two distinctive property lists at /Library/LaunchDaemons/com.apple.googlechrome.plist and ~/Library/LaunchAgents/com.apple.googleserver.plist. Ventura should report those in notifications should it attempt to install them.
Clearly Apple considers this is now a significant threat to macOS users, and its detection by both XProtect and XProtect Remediator is notable.

Although the signature used by KeySteal’s installer has been revoked, and that stops it from being run, it’s likely that its developers are already using a different signature.
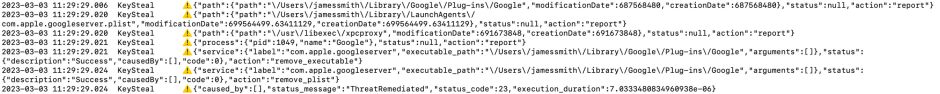
XProtect Remediator 91 now detects and remediates KeySteal effectively if it does manage to get past Gatekeeper.
Honkbox
This too goes back to 2019, when it was first reported, but seems to have reappeared more recently. It has been described in research by Matt Benyo, Ferdous Saljooki and Jaron Bradley of Jamf Threat Labs, and more recently in an update by Phil Stokes of SentinelOne.
Honkbox has been delivered in pirated software, including copies of Final Cut Pro, through PirateBay; whoever is responsible for providing these may also use other similar commercial products to install Honkbox. This is classed as a cryptominer or cryptojacker, and displays evasive behaviour when Activity Monitor is open.
Because the malicious software is embedded within an app that’s already signed, that signature fails when macOS checks it properly. Prior to Ventura, unless the quarantine flag is set on the app, a full signature check by Gatekeeper may well not take place, allowing the malware to install itself. Ventura changes that, as full Gatekeeper signature checks are now run even when there’s no quarantine flag set, so macOS 13 should block this successfully. Added support for detection by XProtect should ensure that it’s reliably blocked on earlier macOS as well.
Honkbox is compelling evidence for the avoidance of hacked apps from sources such as PirateBay: it’s not unusual for them to contain malware, and they’re often obtained using apps and tools that avoid setting the quarantine flag, so reducing the chances of their being detected by macOS, at least prior to Ventura.
Honkbox has received limited attention, and little seems known about it. Clearly Apple’s assessment is that it’s now a significant threat.
BadGacha
All I can tell you about this is that its name is derived from gacha, referring to a family of games based on toy vending machines. I have no idea whether we’ll ever discover what this is in terms of Mac malware, but will let you know if and when a researcher does.
As ever, I’m very grateful to the Objective-See Foundation and Patrick Wardle for providing the sample of KeySteal.

