Keychains have been used in macOS and classic Mac OS for well over twenty years. Although they’ve certainly had their moments, they’re now generally one of the most reliable parts of macOS. This article follows on from my introductory explanation as to what keychains are, and outlines how to tackle their problems.
Password requests
By far the most common problem encountered by users are unexpected or multiple requests for passwords to unlock keychains. Although these have been frequent in the past, they need careful handling as they can be exploited by malicious software to trick the user into surrendering their password for abuse.
Before entering your password into any dialog, check that it’s genuine and not malicious, and provides the following:
- locked padlock icon, with a superimposed miniature icon for the requesting app;
- name of the requesting app;
- name of the item it wants to access;
- name of the keychain to be unlocked;
- that it’s asking for the keychain password, not your Apple ID or other password.
The exact layout of these items has changed a little over the years.
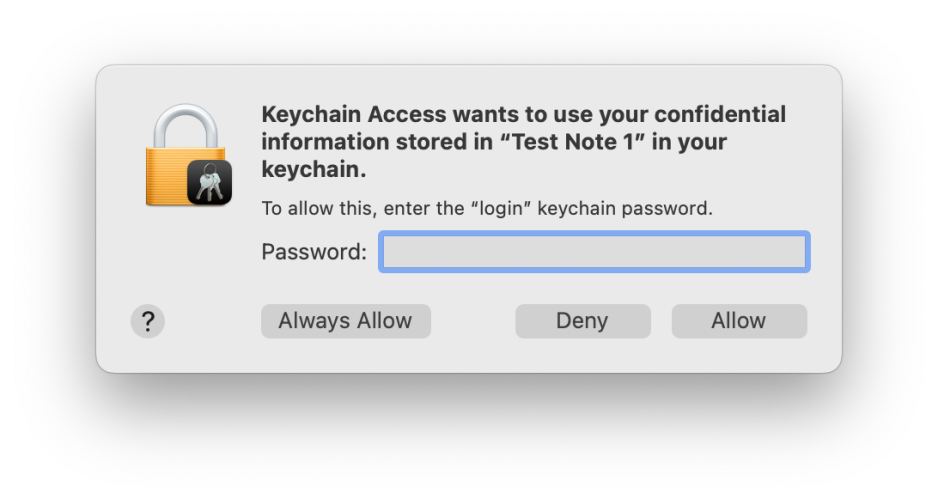
This is from Monterey.
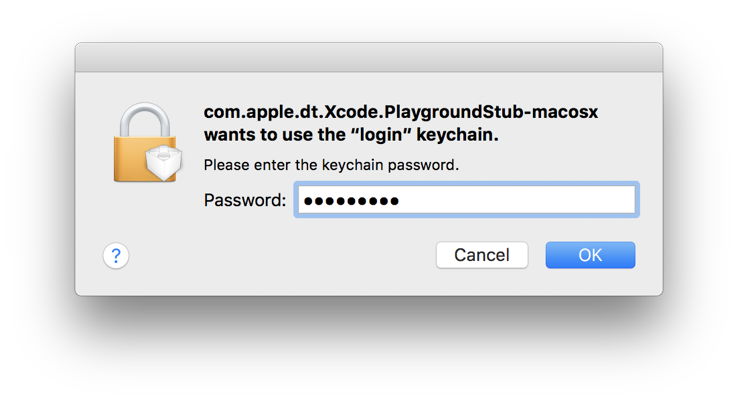
This is from Sierra.
If any request for access to a keychain or its password doesn’t meet all the above, then don’t enter any text into it, and deny the request immediately: it’s likely to be malicious.
You should also be wary of apps suddenly requesting access that they should already have. For example, Safari is normally given full access to your web and Internet access passwords, so it doesn’t prompt you for individual access. If you start seeing requests from Safari to open your login keychain to give access to passwords that it should already have, suspect that the app has been changed, forcing reset of its access rights, or that the requests are bogus; either way you should suspect a security problem. However, this can sometimes occur genuinely when an app has just been updated, for instance.
There are two normal reasons for repeated requests for authentication to unlock keychains: either the app making the request isn’t trusted to access that keychain or item within it, or the keychain is being locked again after use, something that shouldn’t normally happen for the login keychain. If you’re happy that app should be given access to that keychain, instead of pressing Return to Allow that access, click on Always Allow. Your Mac’s security system will then decide whether to give that app lasting access, so saving further requests.
Locking of keychains is simple to observe in the sidebar of Keychain Access, or in Mints’ Keychain tool.
To change locking behaviour of a keychain, select that keychain in the sidebar of Keychain Access and use the Edit / Change Settings for Keychain menu command to show that keychain’s settings. You can then increase the time before that keychain is locked automatically, or disable locking altogether.
If you have custom keychains that are being accessed repeatedly and resulting in repeated password requests, try copying the items being accessed from those to your login keychain, which should eliminate the need to keep opening that custom keychain. Even when you set a custom keychain to be kept unlocked, before you can access it the first time after each login, you’ll be required to enter its password, as it can’t be unlocked automatically in the way that the login keychain is.
Login password mismatch
By default, your user login and login keychain passwords are identical, enabling macOS to automatically unlock your login keychain whenever you log in as that user. When you change your user password, that should automatically change the password for the login keychain as well, ensuring that unlocking still works automatically. However, sometimes the two passwords become different, usually because you changed the password on the login keychain separately.
This results in login requiring you to enter two passwords instead of one. It can normally be rectified by changing the password for the login keychain to the same as the user login password.
Broken keychains
In the past, Keychain Access has also provided a First Aid feature to check and repair faulty or damaged keychains, but it no longer does. Manually reconstructing a keychain or building a fresh one, for instance after resetting the login keychain and wiping its contents, is lengthy and tedious. It’s generally better to migrate or restore from a backup or copy, which isn’t an easy choice either.
Whatever you do, if you’re going to attempt any form of surgery or replacement of a keychain, when working with the login keychain it’s essential to disable Keychain in iCloud first, otherwise changes made in that keychain could be synced across all your other Macs and devices. Sadly, it’s a not uncommon mistake to damage a shared keychain when trying to fix local problems, and that’s even tougher to put right.
Apple Support can be helpful with keychain problems, and can talk you through the steps required to get your Mac’s keychains working again.
Expired certificates
When running older versions of macOS, security certificates provided in system keychains can fall out of date, and then cause all sorts of problems accessing websites and services. If you can locate an updated certificate, install that in the System keychain in /Library/Keychains and those problems should vanish.
Passkeys
Introduced in Safari 16 and most fully in Ventura, there isn’t much to check in a Passkey. Both Safari’s Passwords in Preferences and the Passwords pane report that a Passkey has been set for individual accounts, and offer to send them to another Mac or device by AirDrop if you want. Keychain Access doesn’t yet distinguish Passkeys from other keychain contents, and you shouldn’t try meddling with them.
