SilentKnight and its command line companion silnite are by far the most popular of all my little utilities. Although the app has extensive help pages, I get plenty of questions about what all that information means. This article explains what it checks and reports, and why they’re important.
I originally wrote LockRattler, SilentKnight’s predecessor which is still available for those who prefer it, after Apple inadvertently released a whole batch of MacBook Pros with SIP turned off. At that time, there was no easy way for a user to discover such basic information about their Mac, and I tried to fill that gap.
For advanced users, LockRattler was and remains useful, but it requires you to compare its results with those expected. For firmware in particular, that becomes complex, and my primary aim in SilentKnight was to simplify that by checking against a database of current versions and values.
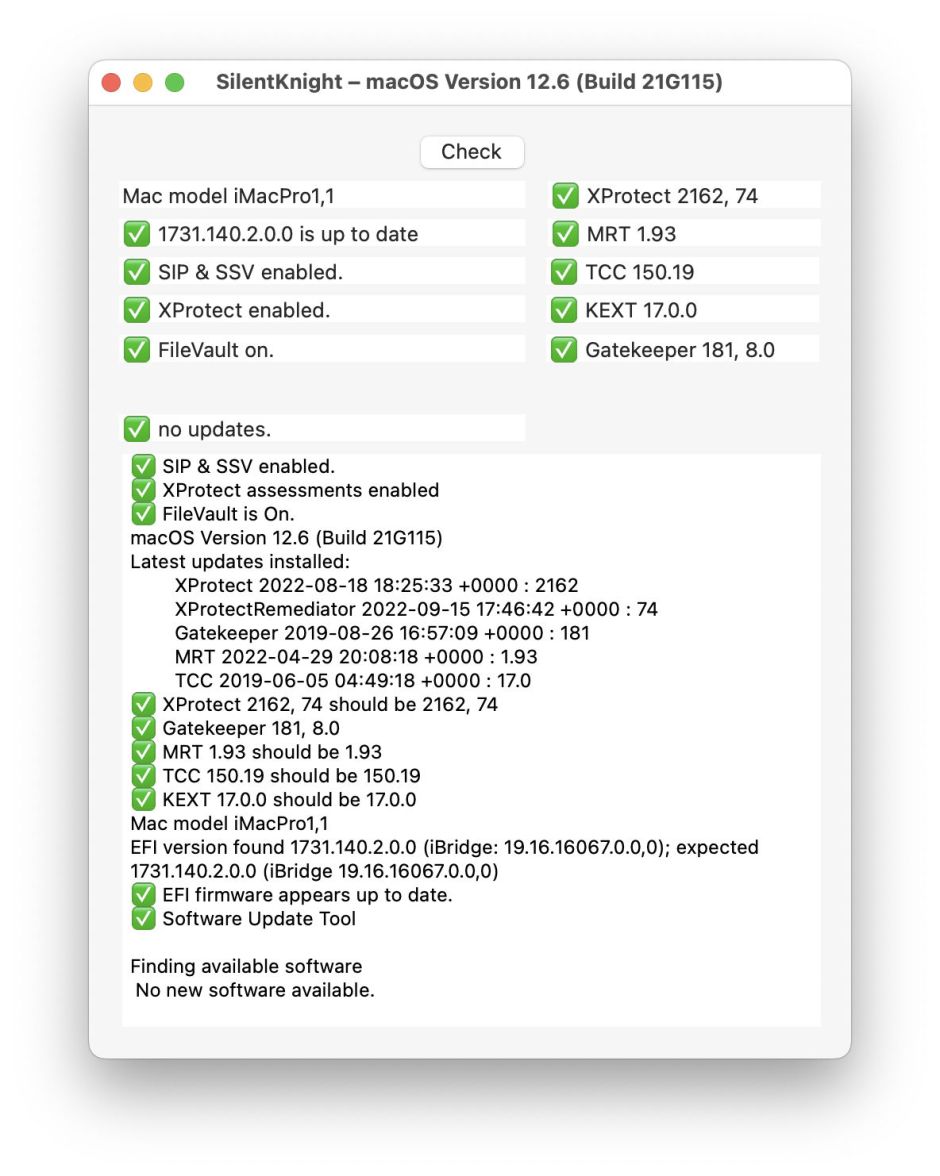
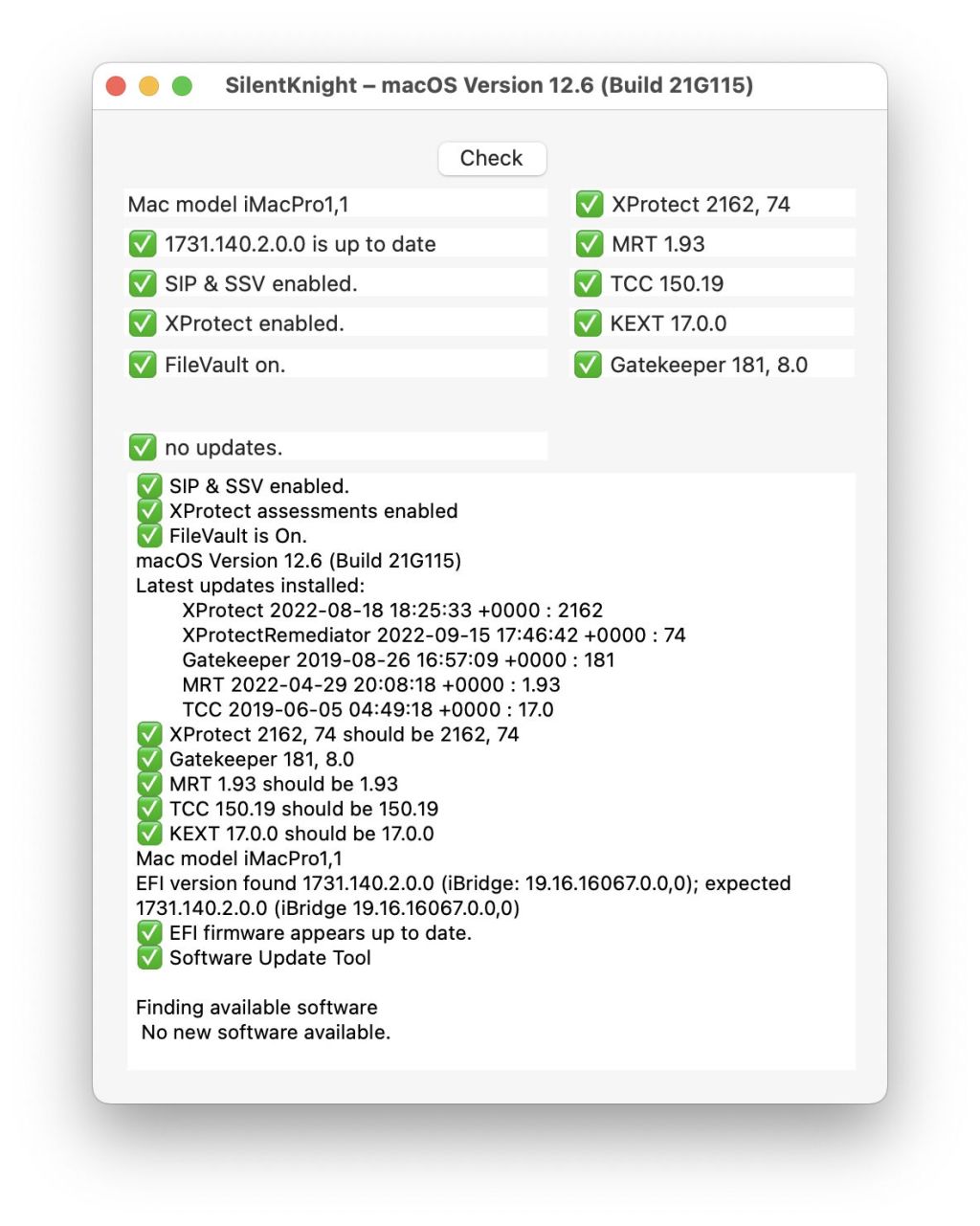
SilentKnight’s window has three different zones, which I’ll consider in turn, from the top left.
Security settings

Mac model gives the standard abbreviated model indicator. The type of Mac is given first, e.g. MacBookPro, then two numbers separated by a comma to identify the series and specific model, e.g. 10,2.
Firmware version is the currently installed firmware. In Intel Macs without a T2 chip, this is the EFI firmware; for models with a T2 this only gives the EFI part, with iBridge being given in the text view below; Apple silicon Macs give the iBoot version, which is different again, and not strictly speaking even firmware. These are fundamental to your Mac’s security and stability, and can now only be updated as part of macOS itself.
Security settings including SIP and SSV are also fundamental. System Integrity Protection (SIP) ensures that nothing can tamper with your Mac’s system files, and extends to all the bundled apps in macOS and more besides. Although sometimes it can be helpful to disable SIP, you should never run a Mac for any longer than is essential with SIP turned off.
In Big Sur and later, this also checks and reports whether the Signed/Sealed System Volume (SSV) is correctly sealed.
Apple Silicon Macs have several additional protections in their Platform Security as well as SIP and the SSV. To evaluate those, SilentKnight checks all that are available, and summarises results in this box. Full details of each security setting are then given in the text box below.
XProtect here refers to whether this checking is enabled. XProtect is responsible for checking apps and some other files for tell-tale signatures indicating that they are malicious. It should always be enabled: if it’s reported as disabled you need to correct that urgently.
FileVault protects the contents of disks by encrypting them. Internal storage of Intel Macs with T2 chips and Apple silicon Macs is always encrypted, although their default encryption doesn’t use your password. If there’s any risk that someone else could gain access to private or sensitive data on your Mac, turn FileVault on. This is an option you control in the Security & Privacy pane of System Preferences.
Security data versions
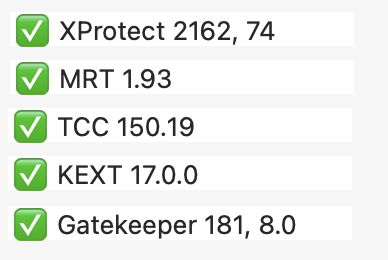
XProtect versions show the current data files used by XProtect to check for malware. In Catalina and later a second version is given for the new XProtect Remediator malware scanners, as those operate using a separate system. That now replaces MRT on those versions of macOS. Both of these versions need to be up to date to ensure your Mac is properly protected against the latest malware.
MRT version gives the version of this older anti-malware tool installed. This is the only such protection on Macs running Mojave and earlier, but has now been replaced by XProtect Remediator in Catalina and later. It hasn’t been updated since April 2022, and may be on its way out now.
TCC version was introduced to protect private data in Mojave, in Transparency Consent and Control (TCC). That uses private data which Apple periodically updates, and changes substantially in new versions of macOS.
KEXT version is a kernel extension exclude list to prevent some old and conflicting kernel extensions from being loaded. This changes with new versions of macOS, and is sometimes updated as well.
Gatekeeper version includes lists of revoked developer security certificates and other information used in old versions of macOS when checking the authenticity of apps and some other items. This has now become disused. Because of that, newer Macs may now have very old versions of Gatekeeper installed. When that’s found, it’s simply reported as being unused.
Apple Studio Display. When you have one or more Apple Studio Displays connected, a new row appears at the foot of the information before that about updates. This states the display recognised, and on the right the current firmware versions are given for each connected Studio Display. If SilentKnight isn’t able to find an Apple Studio Display, this row remains blank.
Text view details

This section provides a complete listing of the results above, and some valuable additions.
Latest updates installed gives the date and version number of the latest update installed for items in the security data versions above. Depending on how they’re installed, these don’t necessarily match the latest version present.
SilentKnight then lists each of the security data versions found, together with what they should be.
It also provides a full statement of the firmware found and that expected. For Intel Macs with T2 chips these include the iBridge version of the T2 itself.
Apple silicon Security
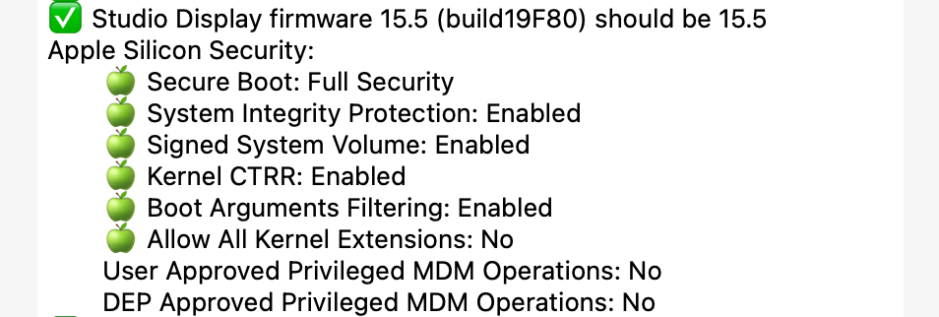
Apple silicon Macs have extensive additional security, normally summarised at the top and detailed in the text view below. Unless you have changed those, Secure Boot should show Full Security, the next four should be enabled, and the final three read No.
Unfortunately, if you’re using a primary language other than English, these results can only be returned in your localised language, which makes it impossible for SilentKnight to decide whether your Mac’s settings are ‘perfect’. In that case, it warns you that you need to inspect these detailed results to determine whether your Mac is fully protected or not.
Warnings

SilentKnight uses green Apple and Tickbox emoji to distinguish results which appear normal, good and current. Where the results need your attention, it shows a yellow warning triangle. Those often aren’t errors or problems, but items you should look at carefully to ensure they’re correct. Where versions are out of date or you should do something about them, it shows a red X. Full details are available in the Help file and Help reference, in the Help menu, which explains what you can do to address problems.
Errors updating
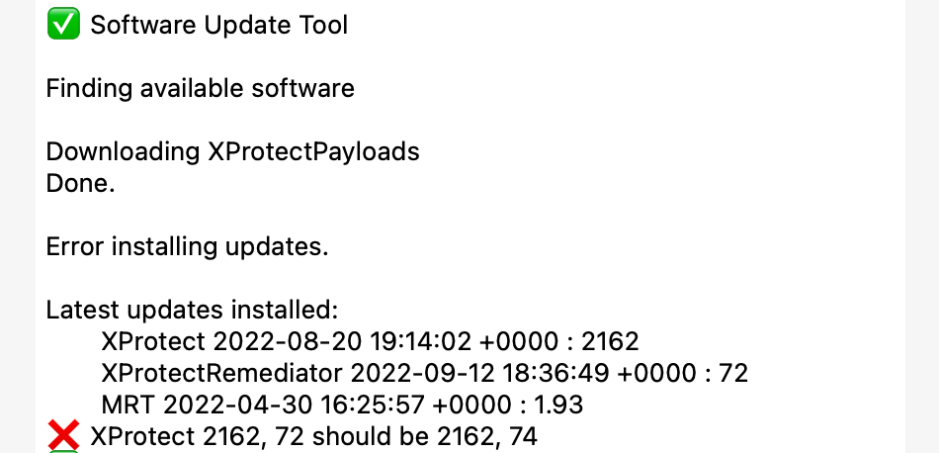
The commonest problem seen using SilentKnight at present is the result of a bug in macOS and security data installers, shown in the screenshot above. SilentKnight finds updates, you click to Install all updates, they’re downloaded, but fail to install on your Mac, leaving it without the updates.
The most common cause of this is when running a local Content Caching server. The remedy then is simply to quit SilentKnight, temporarily turn the Content Caching service off in the Sharing pane, open SilentKnight and try installing the updates again. Once they’ve installed successfully, enable the Content Caching service once more. Further details are here.
SilentKnight, LockRattler and silnite are all available from their Product Page.