The most important security feature in Big Sur is its new Sealed System Volume (SSV), which locks away all immutable system files with an ingenious method for preserving their integrity. So how can you check whether your Big Sur System volume is correctly sealed?
If your Mac is an Intel model, then I’m afraid that utilities such as System Information or Disk Utility don’t seem to know. Things are a bit different on an M1 Mac, which I’ll return to later. One perhaps obvious way to see the status of each volume, including the SSV, is using the Terminal command
diskutil apfs list
only what you then see may lead you to think that something has already broken the seal on your Mac’s SSV.
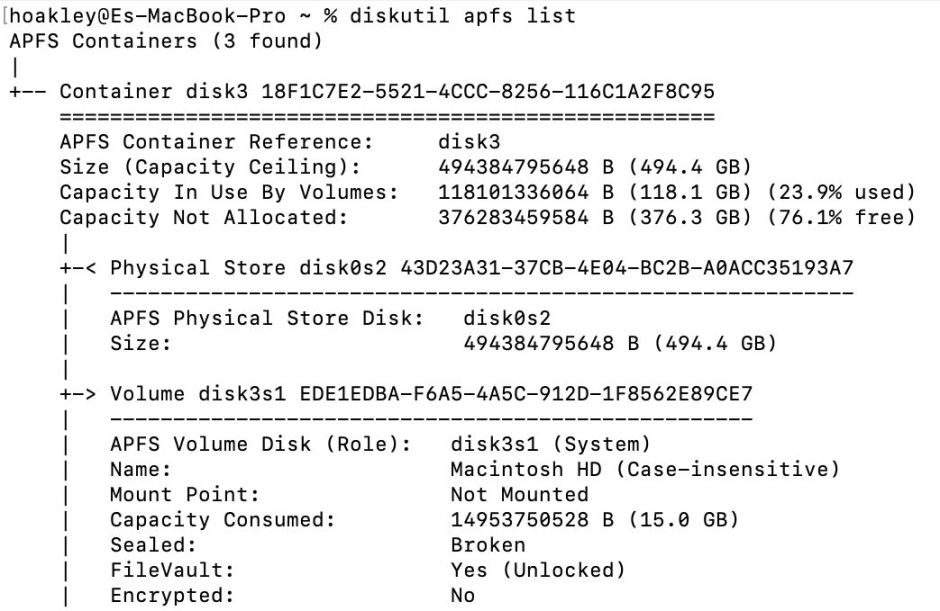
So the System volume at disk3s1 (your numbers may differ) has a broken seal?
To understand why that’s perhaps the wrong question, we need to step through how Big Sur creates the SSV in the first place. During system installation, the whole system is created on the System volume. Once complete, and protected by SIP, the installer then creates the Merkle tree of hashes up to the Seal, the one hash to rule them all, and makes a snapshot. The tree of hashes and its Seal are then stored in the file system metadata which make up that snapshot. The sealed snapshot is then mounted and the System volume itself is unmounted.
So it’s not the System volume which is sealed now, but that snapshot. Scroll down a little and you’ll see that there’s separate information given about that.
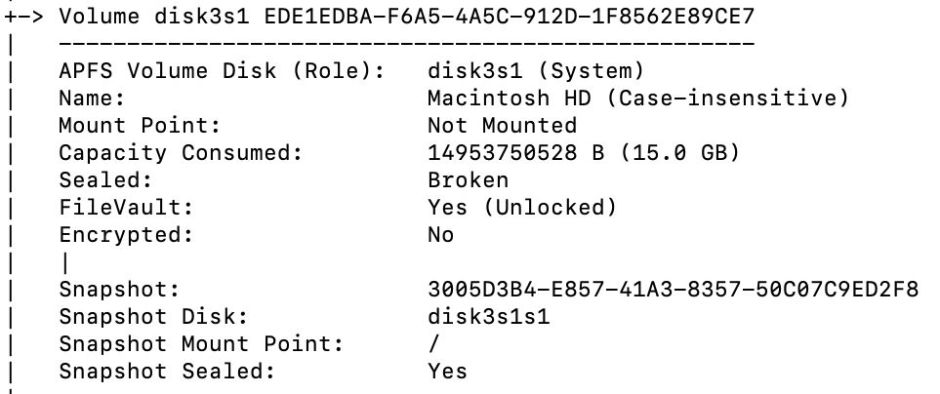
That snapshot, which is mounted as the root /, is sealed after all. That crucial piece of information appears to have been omitted from other locations in Big Sur when it’s running on an Intel Mac.
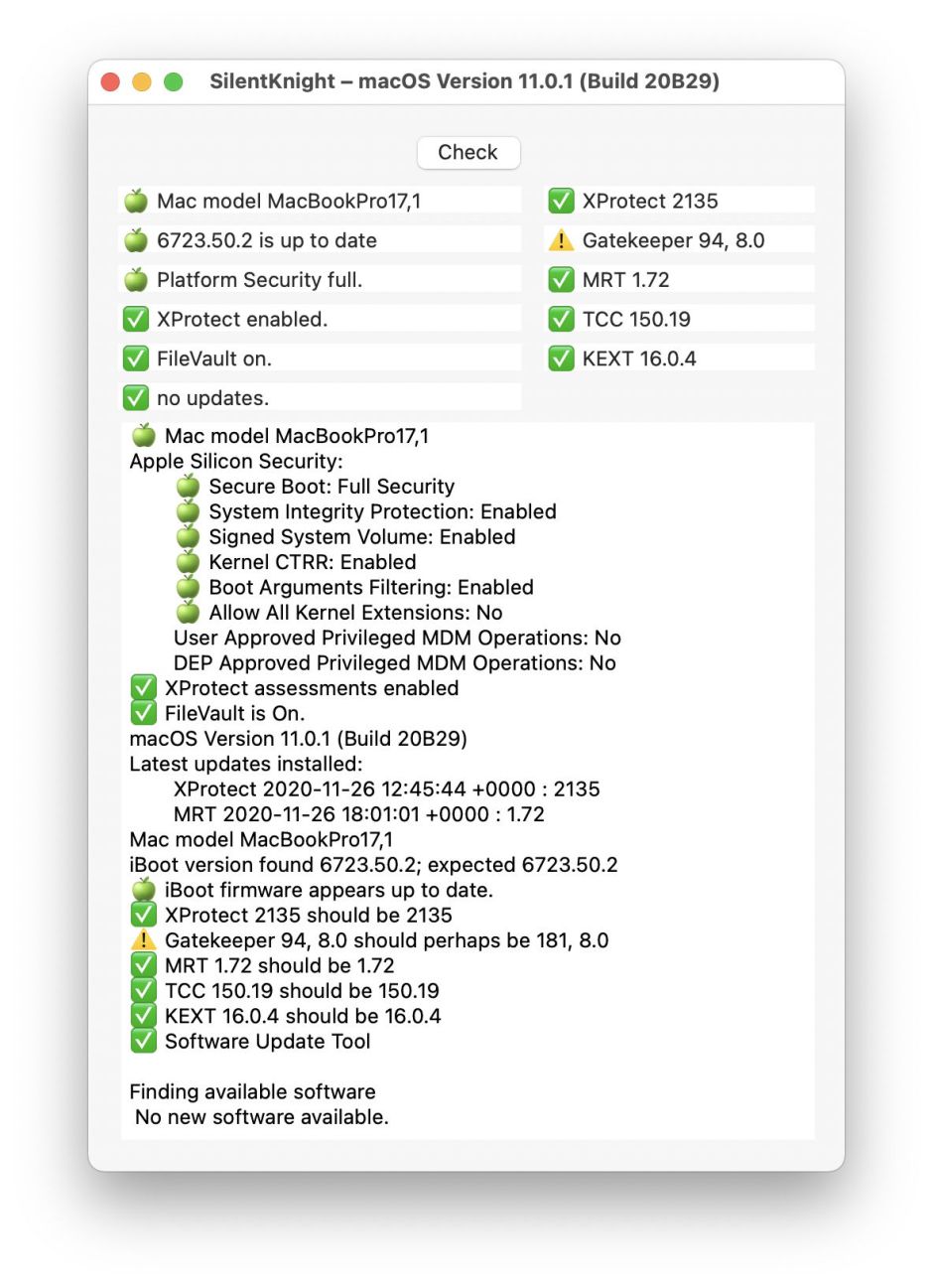
This is slightly less confusing when viewed on an M1 Mac: in System Information, select the Controller item in the Hardware section, and you’ll see, under Boot Policy:
Signed System Volume: Enabled
which I presume is synonymous with Sealed System Volume.
Those same security settings are given in my free utility SilentKnight too.
There is a more specific informative command available on both Intel and Apple Silicon Macs which gives a clear answer:
csrutil authenticated-root status
which should return
Authenticated Root status: enabled
to settle the matter.
But what’s currently shown on Intel Macs, and in diskutil, remains far from clear. Hopefully in a future version of Big Sur, Apple will put our minds more at ease.
Thanks to Sarah Edwards @iamevltwin for asking the question.
