Unlike iOS devices, a great many Macs use external storage in the form of removable volumes. Perhaps their commonest use is for backups, particularly Time Machine, which can’t of course be made to the single internal disk which is all the vast majority of Macs are capable of. A great many users also keep some or all of their user Home folders on external drives: with the high cost of additional internal storage, this makes excellent sense.
So long as you don’t run macOS Catalina, this all works fine. There are different ways of linking folders on your external storage to your internal startup volume, and if you want it’s not hard to link a complete Home folder – that’s the power and flexibility of macOS at work. Standard apps like iTunes/Music and Photos also make it simple to keep large libraries externally, and many users have to. The snag is that, according to Catalina’s new privacy protection, anything on a removable volume, which inevitably means all external storage, is treated as different, and non-sandboxed apps may have to be given special permission to access it. What was previously a neat and trouble-free arrangement now becomes a series of exceptional cases, tedious dialogs, and the occasional intransigent failure.
Unlike the rest of macOS, Catalina’s privacy protection is completely inflexible in its model of what goes where. It provides special protection to:
- ~/Desktop,
- ~/Documents,
- ~/Downloads,
- removable volumes,
- network volumes,
- iCloud,
- third-party cloud storage.
If you have chosen to keep files which would normally be in your Home folder on an external volume, then they’ll likely be protected as being on a removable volume, even if they don’t otherwise qualify. If you prefer to keep documents for projects in the folder ~/Projects instead of ~/Documents/Projects, then they won’t be protected at all.
In theory at least none of this should apply to apps and other software which access files using only ‘standard’ methods which establish ‘user intent’, such as the regular Open File dialog, and others which work through LaunchServices. I’ve previously reassured users that would make it most unusual to be prompted by macOS to give access to a protected folder. However, Catalina doesn’t seem to work so simply or helpfully, and I fear my reassurances were over-optimistic.
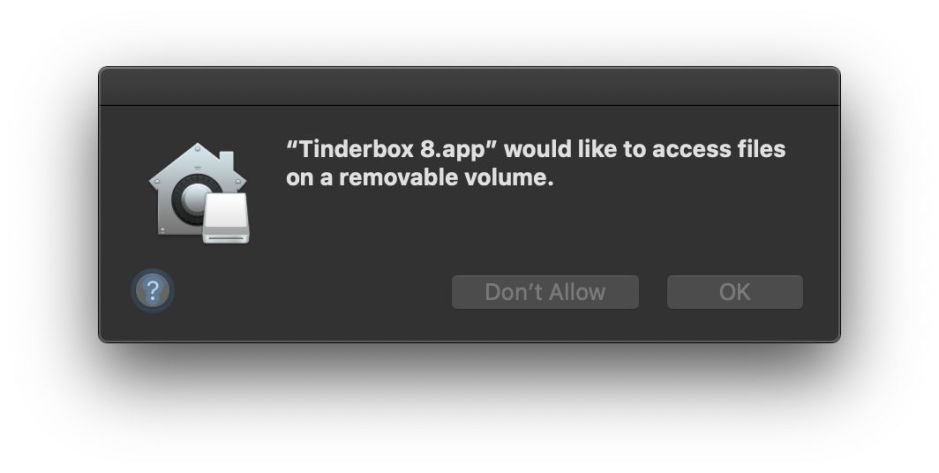
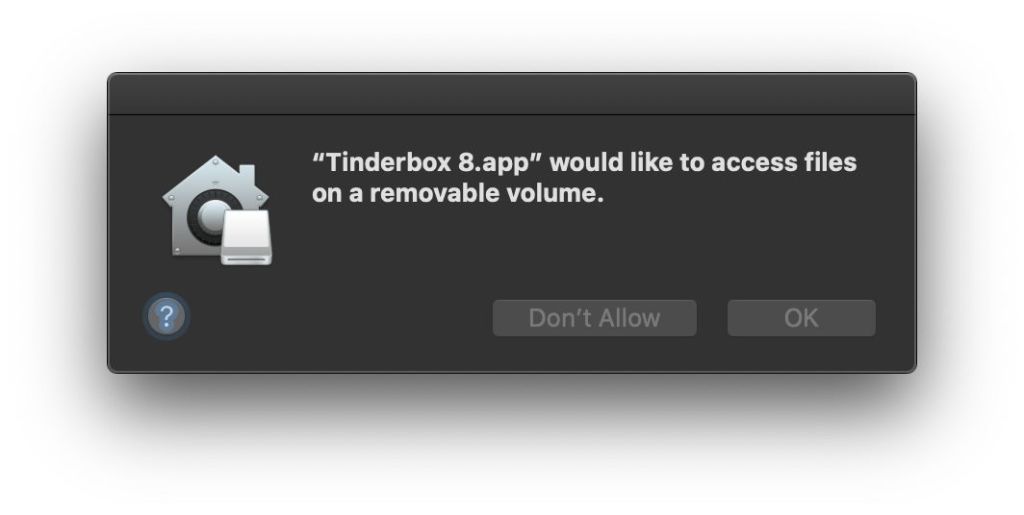
For example, yesterday I wanted to open one of my regular Tinderbox documents, which is stored in an extension to my ~/Documents folder on an external SSD. Although I selected this through the Open Recent command in the File menu, I was asked whether I wanted to give the Tinderbox app access to “files on a removable volume”, and when I agreed (could I really have refused?), that app was then added to the steadily growing list in Files and Folders of the Privacy tab in the Security & Privacy pane.

The user is here almost without options: you can’t exclude an external volume from this protection, and you can’t add an app to this list directly. The only control which you can use to avoid these dialogs is to give most of your apps Full Disk Access, which is much more than you’d want to in most cases. The developer can’t do much about this either: although they can supply a Usage string, which provides more information to the user when macOS decides a consent dialog is needed, there’s no entitlement that a non-sandboxed app can claim which pre-authorises access (a longstanding complaint about Apple’s privacy protection generally).
Not only does Catalina appear to ignore user intent, but I have recently demonstrated a situation where it refuses to respect user intent or privacy settings, and blocks an app completely from writing to a removable volume.
I happen to use a lot of apps which aren’t sandboxed. For a start, there are getting on for 40 free utilities of my own which sooner or later could fall foul of this erratic protection of removable volumes. Or does Apple want all apps to be sandboxed and hobbled so many can’t do their jobs properly? In this article, I have considered only the problems arising with respect to removable volumes, and not examined similar issues arising for those using networked volumes more extensively, or for cloud storage.
macOS is a desktop operating system, which empowers its users and provides a great deal of flexibility. Any privacy protection system which assumes that specific named folders will be used for stereotype functions, and that all storage beyond the internal volume requires full protection, is too blunt and inflexible.
If you rely on folder and volume layout and usage which departs from Apple’s rigid expectations, you might want to think twice about upgrading to Catalina. For the moment at least, it’s not capable of accommodating your needs, and will unnecessarily protect some locations, whilst leaving sensitive data in others completely unprotected.