When the security certificates on all of Apple’s software installers and updaters built before late September expired last month, we came to realise how complex some are. Installer packages are straighforward to check, and you can take them apart using utilities such as the excellent Suspicious Package from Mothers Ruin. But self-contained installer apps aren’t as straightforward to assess.
Apple distributes macOS and its updates in two main forms: executable apps, which are standard for complete installations including major releases of macOS, and Installer packages, which are the normal means of distributing updates. This article looks at the former; sometimes Apple has experimented with two-part installer apps, as it did in the earliest release of High Sierra. Those consist of an initial small app, which in turn downloads a full installer, and are a nightmare in several respects, so here I’ll ignore them and hope that they never return.
For regular users, installer apps are normally obtained through the App Store as an intermediary, or direct using the Software Update pane in recent versions of macOS. In the past, they’ve had a bad habit of deleting themselves once installation is complete: to ensure this doesn’t happen, before starting the installation by clicking on the Continue button on its splash screen, make a copy of it in another folder for safekeeping, or you may have to download it again in order to keep a copy to hand.
The strange thing with these installer apps is that you can’t assess them in the way that you would a normal app. Drag and drop the whole app onto ArchiChect 2, for example, and although you’ll see a signing error reported, the app gets around that, because it arrives without its quarantine flag being set, so doesn’t have to go through ‘first run’ Gatekeeper checks.
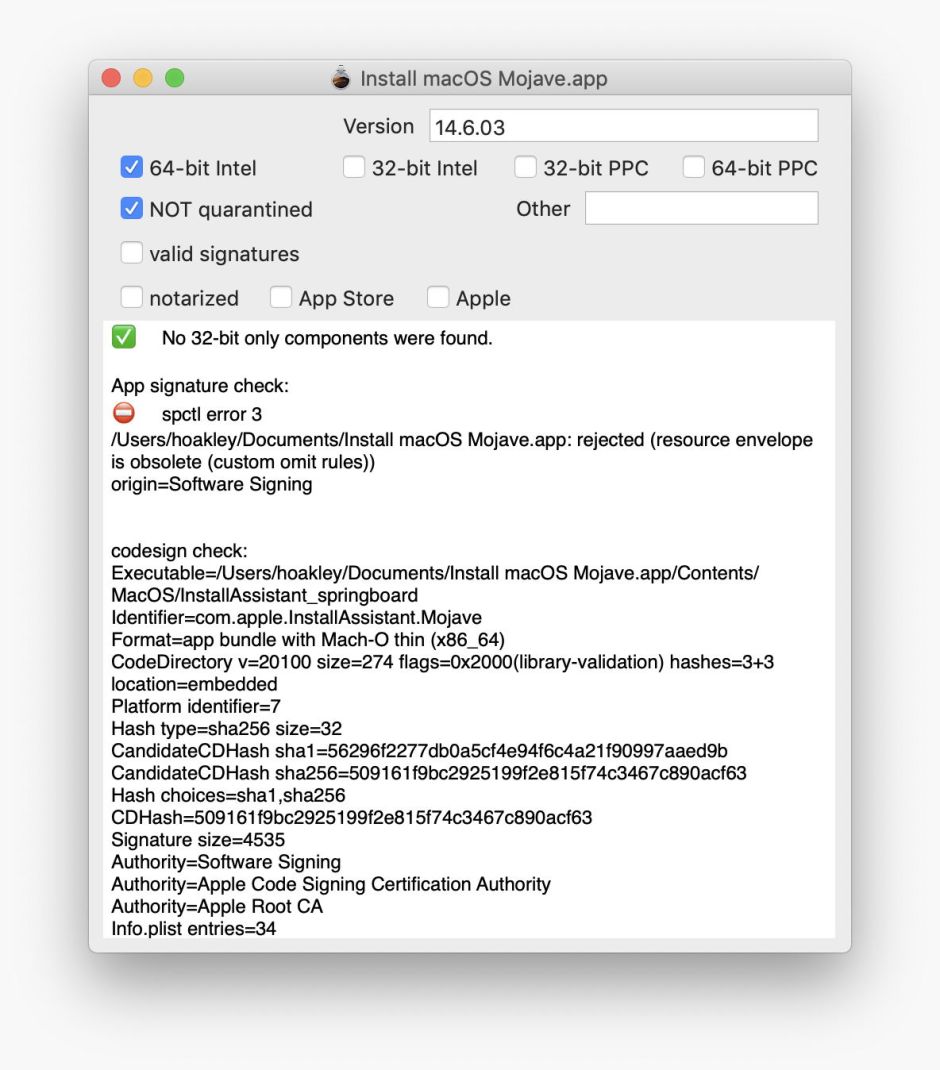
If you add a quarantine flag to a macOS installer app, Gatekeeper will report that it “can’t be opened because the identity of the developer cannot be confirmed”, which means that as far as Gatekeeper is concerned the app is effectively unsigned! What is signed is buried rather deeper inside the app.
Here’s a cautionary note for those who want to move Installer apps around: if the method results in a quarantine flag being set on the installer app, because it’s unsigned, that might require special handling when you want to open it. If you simply double-click on the app, and it undergoes Gatekeeper checks, it shouldn’t pass.
As with any app, a macOS installer contains a single folder named Contents. Within that are the normal folders you’d expect to find in a substantial application: _CodeSignature, Frameworks, MacOS, PlugIns, and Resources, with the addition of SharedSupport. There’s also a standard Info.plist Property List file, PkgInfo, and version.plist.
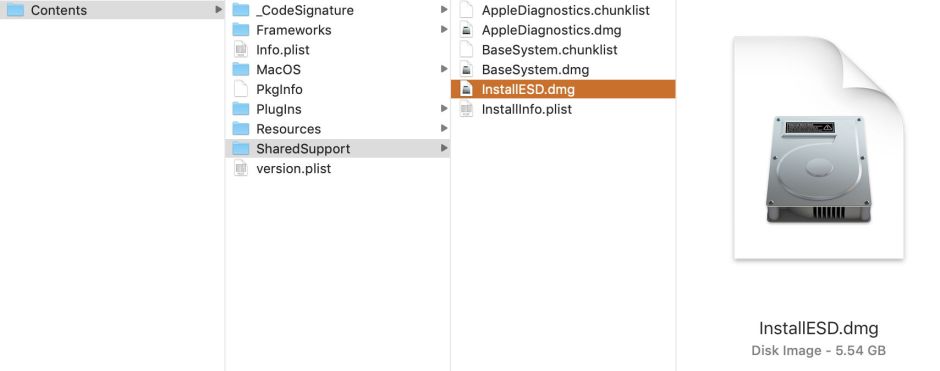
The app’s executable code is in the MacOS folder, and is based on one or more binaries with names starting with InstallAssistant. Those are the ‘app’ proper, which starts the installation process.
The files to be installed are contained in SharedSupport, and consist of several disk images, within which are separate Installer packages. In recent installer apps, the largest of these, containing the bulk of macOS, is named InstallESD.dmg. Older install apps may be different, but it shouldn’t take you more than a few moments to locate the largest of those disk images, then double-click it to mount the image.
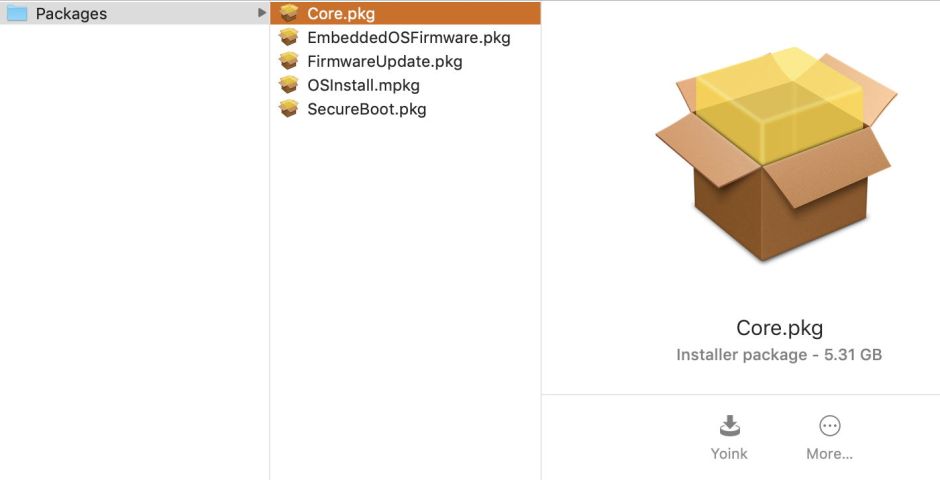
Once mounted, you should see the image contains a single folder named Packages, within which are several Installer packages, normally including the very large Core.pkg, which contains the bulk of the system folders and files. Drag and drop that onto a utility such as ArchiChect 2, and you’ll finally see whether the Installer app’s certificates are good, or have a problem.
In this case, the four major checkboxes at the left reveal that there’s no code to check as it’s an Installer package, it isn’t quarantined so won’t be put through Gatekeeper, it doesn’t have valid signatures, but was signed by Apple.
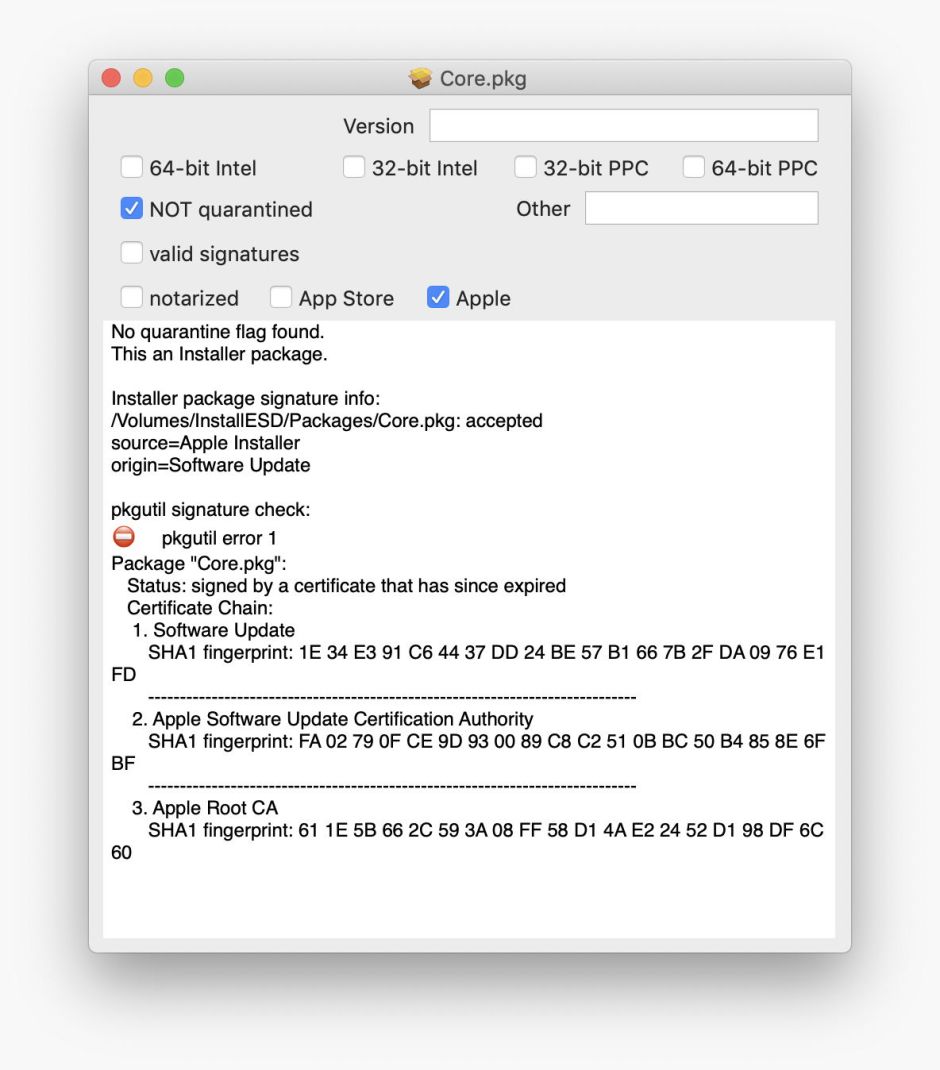
Look down at the text view for a detailed explanation. In this case, it has been correctly reported as being an Installer package without a quarantine flag, but fails the second of the two signature checks (pkgutil) because it was “signed by a certificate that has since expired.”
If you can find a file, folder or bundle which ArchiChect 2 can’t assess properly, please let me know.
