A week ago, Mac users were alerted to a sinister danger: if you had previously installed certain conferencing software, in particular that for Zoom, then even though you may have removed that, it probably left behind a hidden web server which could have been exploited remotely. Because that was a serious vulnerability, Apple pushed an update to its malware removal tool MRT to remove the old Zoom web server.
A couple of days ago, Apple pushed a third update to MRT which removed all similar hidden web servers which had been installed by other related products. The product vendors should over this time have updated their software, so now is a good time to check that your Mac is clean. This article explains how to do so.
1. Is your MRT up to date?
The primary tool to remove these web servers is MRT, and by now your Mac should have been updated to version 1.47. To confirm that is the case, Apple recommends that you consult the list of Installations in System Information. However, that isn’t reliable: the listing there only states what has been downloaded and ‘installed’. It is perfectly possible for one of the installations to have failed to complete the update.
The only reliable way to check that the MRT installed on your Mac is 1.47 is to use my free SilentKnight, LockRattler, or to inspect the version yourself. You can do the latter by selecting the app at /System/Library/CoreServices/MRT.app in the Finder and reading its version number. If that’s anything earlier than 1.47, then you’ll need to check for the update and install it. Again, that’s easiest using SilentKnight or LockRattler.

When these updates are installed, they should run automatically soon afterwards, but some users have reported that hasn’t worked. The only other time that MRT will run normally is soon after starting your Mac up. So if you haven’t started up since the MRT 1.47 update was installed, it’s worth restarting now, to make sure.
2. Has the hidden folder gone?
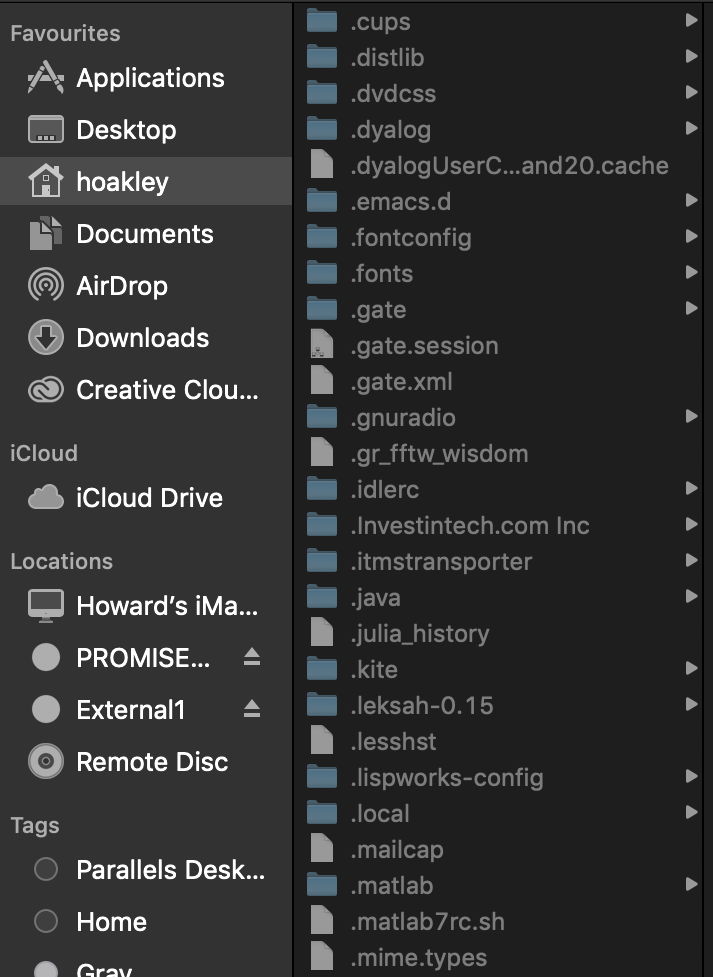
Although the web server was intended to be hidden from view, it’s actually quite easy to see. In a Finder window set to Column View, select your Home folder in the sidebar, and press Command-Shift-. (⌘⇧.) to reveal hidden files and folders. Look for a folder with a name similar to any of the following:
- accessionmeetingopener
- attvideomeetingsopener
- bizconfopener
- btcloudphonemeetingsopener
- earthlinkmeetingroomopener
- huihuiopener
- officesuitehdmeetingopener
- ringcentralopener
- telusmeetingsopener
- umeetingopener
- videoconferenciatelmexopener
- zhumuopener
- zoomcnopener
- zoomus
One trick which has been used to prevent these web servers from being installed is to write a file of the same name and lock its permissions. So if you find a file with one of those names, rather than a folder, it could have been placed there as a defence, and should remain. Once you’re happy, don’t forget to press Command-Shift-. again to turn hidden items off.
3. Has the app been removed from the Privacy list? (updated)
This is more complex than I first thought. When you uninstall an app which has already obtained your consent for access to protected resources, such as the camera and microphone, macOS removes it from the lists in the Privacy tab of the Security & Privacy pane but doesn’t remove it from its database. If you were to reinstall the app, it would automatically be given the same access to those protected resources as it had at the time of removal.
To ensure that any reinstalled app would have to go back through the same process of obtaining your consent to access protected resources, you need to remove your consent for those resources in the Privacy settings before uninstalling that app. If you don’t, macOS will remove the app from the privacy lists, but they will remain in its database and be reactivated should you ever reinstall the app.
If you did at any time install the Zoom app or one of its siblings and give it access to your camera or microphone, you will probably want to install the app again, untick it from those lists in the Privacy tab, then uninstall it. Although this is tedious and messy, that will ensure that the app can’t access them without obtaining your consent again.

That way, if you do ever install and try using one of these apps in the future, it will have to go through the process of obtaining your consent. Who said that Mojave’s privacy wasn’t acting in the user’s interests?
(Updated 19 July 2019 to add details from MRT 1.47 update, and to change privacy info. Thanks to Jeff Johnson @lapcatsoftware for pointing out the problems with the latter.)
