I’m not in the habit of checking the security certificates in my login keychain, but after the 10.14.4 update Jeff Johnson @lapcatsoftware tweeted to ask if anyone else had noticed the magical appearance of a new certificate. Sure enough, there it was in my login keychain. “member:” followed by two UUIDs: it sticks out like a sore thumb, and looks like it was added by Apple.
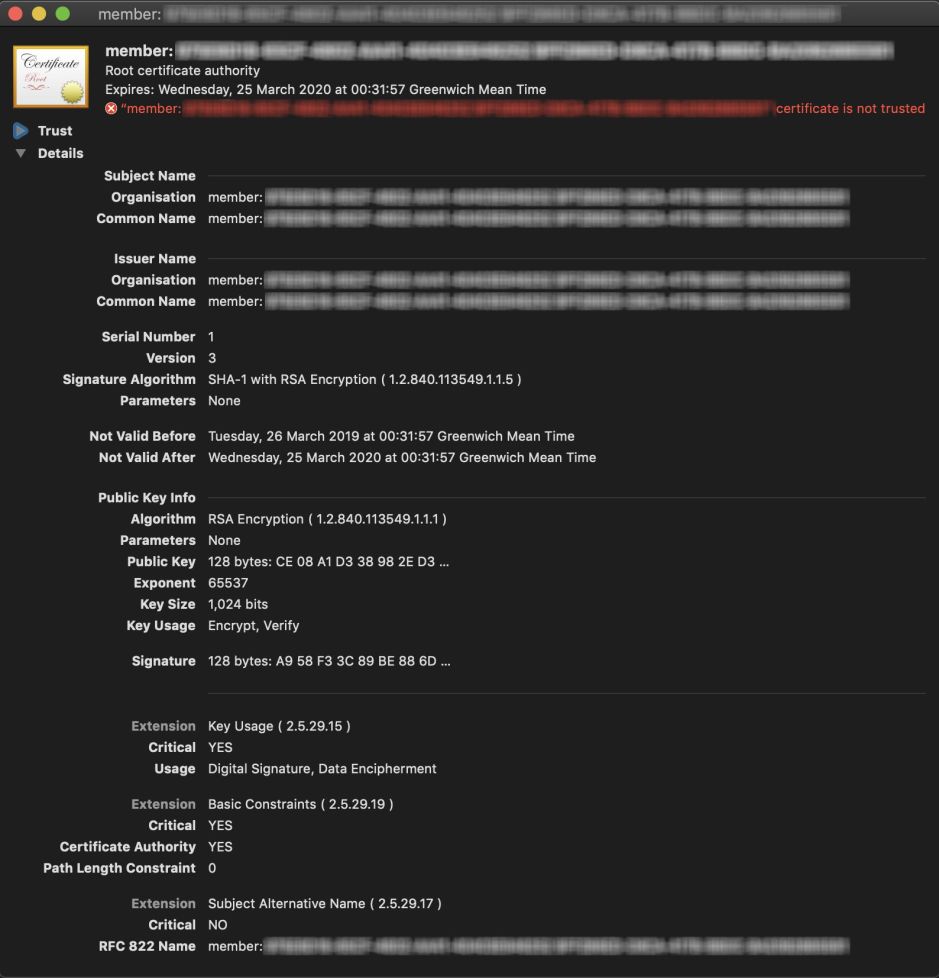
It purports to have root certificate authority itself, but macOS isn’t convinced about that and declares that it isn’t trusted. Which would, in the normal run of things, make it a pretty useless security certificate.
Looking at times, it appears to have been created just after logging in when the 10.14.4 update had completed. I know from SysHist that the update datestamp was 00:24:35 UTC on 26 March 2019. The certificate is only valid from 00:31:57 that same day, which would have been the time of its creation. Then at 00:40:48 I installed the Gatekeeper update using LockRattler.
Browsing the unified log for the time in question, I am struck by the number of entries referring to studentd and com.apple.classroom. I’ve browsed through many logs, including a lot of boots and logins, and have never noticed these before. This new certificate appears to have been created at a time when those processes were active, at the time that I was signing back into my account. Of course, they also coincide with my Mac signing back into things like Adobe Creative Cloud, but Adobe’s security certificates are normally easy to spot. This looks like the work of macOS rather than any third party software.
The use of UUIDs is strange, and neither matches anything obvious such as my Mac’s UUID or that of any mounted volume. As I don’t know of any central registry of UUIDs, trying to trace them any further is likely to prove fruitless. I’ve been there before.
studentd is an unusual process to see on this standalone iMac Pro at login time too. I’d not come across it before, and its man page gives little away:
studentd manages the Classroom experience for students. studentd should not be invoked directly. studentd might be running without classes configured.
What is more interesting there is that, unlike most man pages, this one was written after Mojave shipped. Unless you use Macs or iPads in education, Classroom probably means nothing to you: Apple describes it here, with a full user guide. Needless to say, this Mac hasn’t been near it since I bought it new late last year.
Apart from studentd and Classroom, the other new contender for creating this certificate might be Apple’s News+ service. As News+ hasn’t yet launched in the UK, that would appear somewhat premature.
So something, almost certainly an Apple process, created a new root certificate which isn’t trusted, in my login keychain when I was signing back into my account after updating to macOS 10.14.4. So it did on Jeff Johnson’s Mac, and probably yours too.
If you have any idea what this security certificate is for, and what generated it, I’d be fascinated to hear from you. Apple just loves us to have a good mystery.
Thanks again to Jeff Johnson for piquing my curiosity. I’m sure that he’s already got this worked out.
