I apologise again for the interruption to my regular weekly article Last Week on My Mac, which appeared then disappeared yesterday. I’m still not quite sure what happened, but I had mistakenly concluded that Apple had changed the behaviour of the secure shell, ssh, with respect to privacy protection. Despite several sessions looking carefully at this, even studying the logs of both client and server during ssh connections, I was completely wrong.
For the avoidance of any doubt, Mojave 10.14.1 update hasn’t changed the behaviour of ssh with respect to privacy protection: if you enable Remote Login to your Mac in its Sharing pane, then anyone who gains access as a user using ssh can see all that user’s private data.
Whether this is a bug or a feature, I’ll leave you to judge when I explain how this works. It is particularly interesting, as it is one of the rare exceptions to the rule that only user interaction can modify the lists in Privacy: here, TCC adds its own item to the Full Disk Access list without any user warning or consent.
As far as access by the secure shell is concerned, Macs are in one of three states:
- never accessed, and
sshd-keygen-wrapperis absent from the Full Disk Access list; - accessed and permission granted, with
sshd-keygen-wrapperlisted and ticked; - accessed and permission now stopped, with
sshd-keygen-wrapperlisted but not ticked.
When you try to access that Mac using ssh, if it is in either of the first two states, macOS will automatically give ssh Full Disk Access. It is only when Privacy settings are in the last state that access to protected data will be refused. The only control that the user has is enabling and disabling the sshd-keygen-wrapper in the Full Disk Access list, which has the effect of toggling access to protected data for that user. Note that removing the sshd-keygen-wrapper item from the list sets it back to the first state, effectively enabling Full Disk Access: it does not prevent access to protected data at all.
With an ssh connection to a Mac, asking to list or view the contents of items which are not protected by TCC takes place through opendirectoryd and supporting services, and doesn’t involve TCC at all.

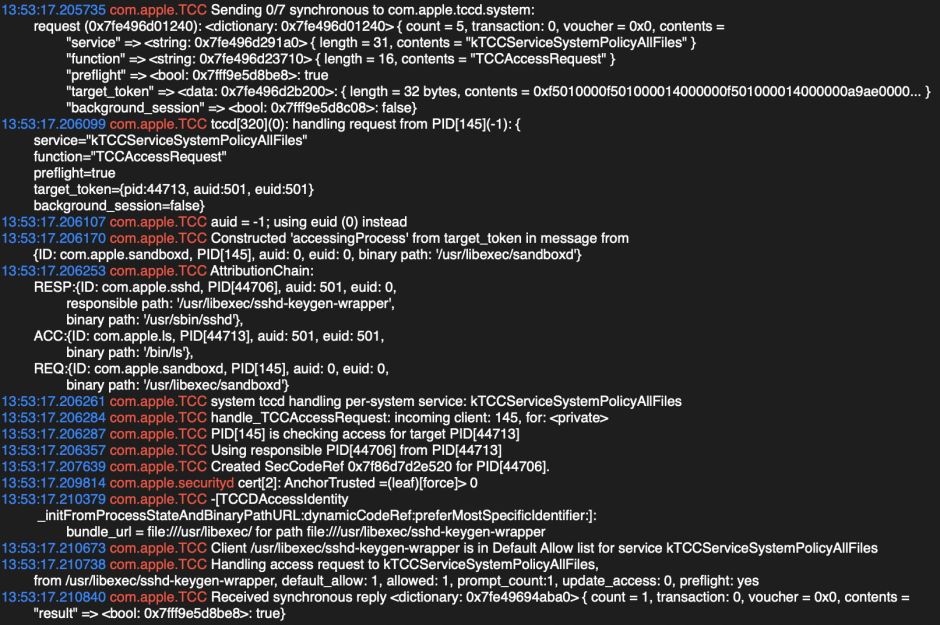
When you ask, for example to list the contents of the ~/Library/Calendars folder using ls, in the first instance a synchronous request is made to com.apple.tccd.system for the service kTCCServiceSystemPolicyAllFiles and function TCCAccessRequest. TCC constructs the attribution chain for this with the requester (REQ) as /usr/libexec/sandboxd, the access requested (ACC) as /bin/ls, and the responsible process (RESP) as /usr/sbin/sshd with a responsible path of /usr/libexec/sshd-keygen-wrapper.
sshd-keygen-wrapper is a tiny bit of code which is inevitably undocumented, and concerned with generating keys for ssh. It has in the past acted as a proxy for ssh/sshd in configuring firewalls, and here it also seems to act as a proxy for sshd.
The first time that you connect to a Mac using ssd, sshd-keygen-wrapper isn’t in the Full Disk Access list, which securityd complains about in the log:
could not enable test hierarchy: no UAT pinning preferences set
Presumably UAT pinning is the internal term for the user listings set in Privacy. This results in additional checking with securityd:
com.apple.TCC -[TCCDAccessIdentity staticCode]: static code for: identifier /usr/libexec/sshd-keygen-wrapper, type: 1: 0x7f86d7c5abc0 at /usr/libexec/sshd-keygen-wrapper
com.apple.securityd cert[2]: AnchorTrusted =(leaf)[force]> 0
and the result of the query with TCC is true – the access can go ahead, and sshd-keygen-wrapper is magically added to the Full Disk Access list by TCC.
This illustrates how, using current mechanisms, third party apps cannot add themselves to the Full Disk Access list, even with a user’s consent: to do so here requires TCC to have it on its defaults list, to recognise it as static code of a particular type (and presumably protected by SIP), and for securityd to confirm that it is signed by Apple.
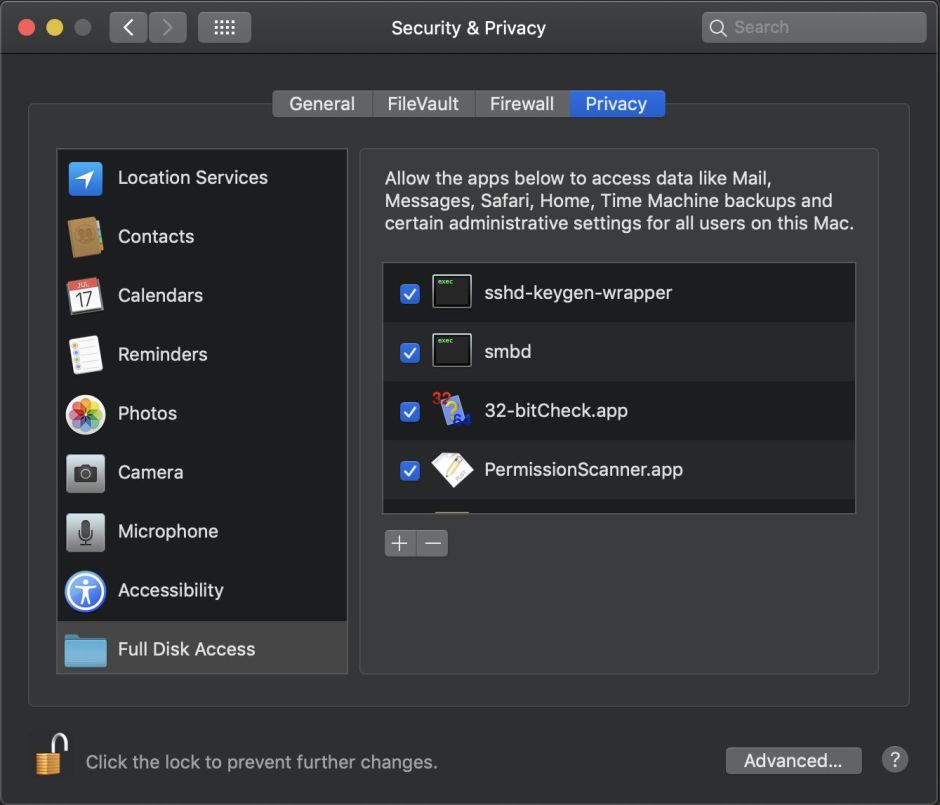
The next time around, with sshd-keygen-wrapper in the Full Disk Access list, TCC authorises access direct from the allow list, which saves those couple of steps.
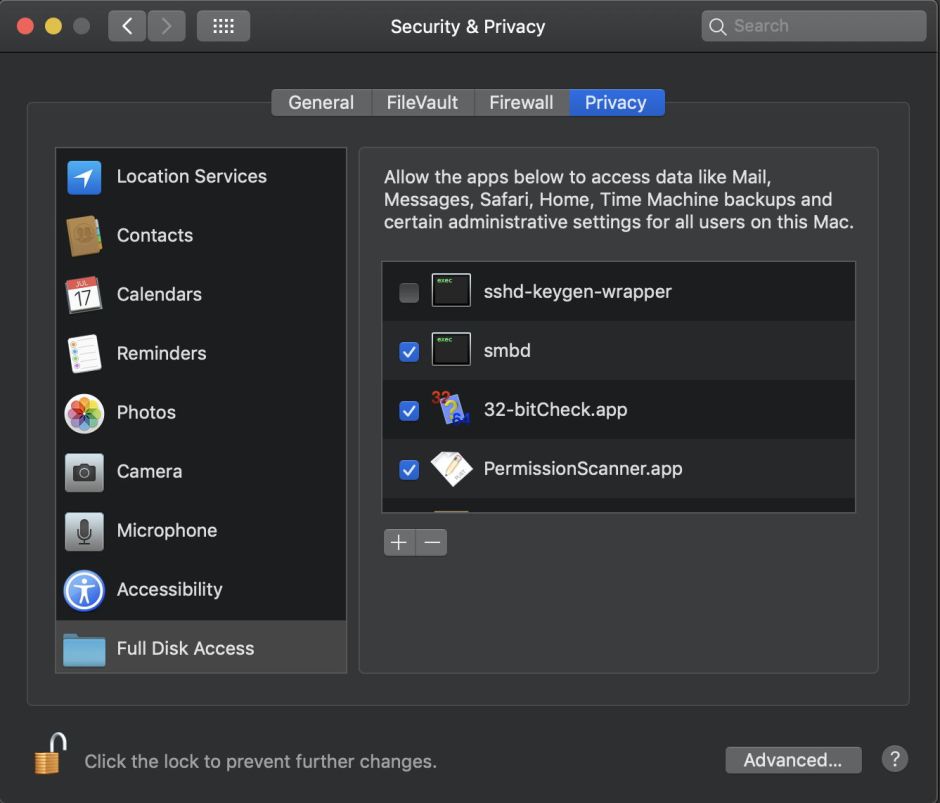
If you then disable (by unticking, not removal) sshd-keygen-wrapper in the Full Disk Access list, this first and most general request is refused:
kTCCServiceSystemPolicyAllFiles is denied.

TCC then tries a more specific access list, that for Calendars alone, with a synchronous request for the service kTCCServiceCalendar and function TCCAccessRequest. To that, TCC responds preflight_unknown, meaning that it doesn’t contain the expected information which could enable access to be granted, and sandbox then points out
kTCCServiceCalendar would require prompt by TCC for ls
In other words, this is a faceless command tool which would have required TCC to seek user consent.
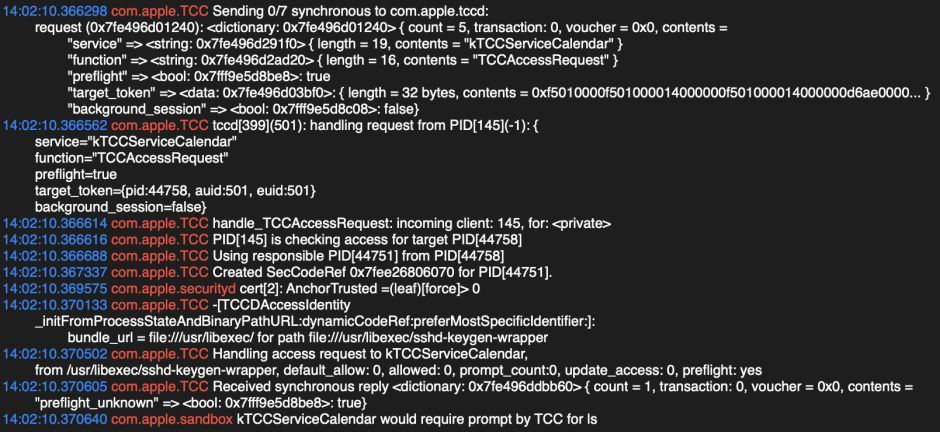
As that is not possible here, the request fails.
TCC continues to try and repeats other requests, for the services kTCCServiceReminders, kTCCServiceCalendar, and eventually the sandbox reports
Sandbox: ls(44758) System Policy: deny(1) file-read-data /Users/hoakley/Library/Calendars
for the responsible sshd-keygen-wrapper stub.
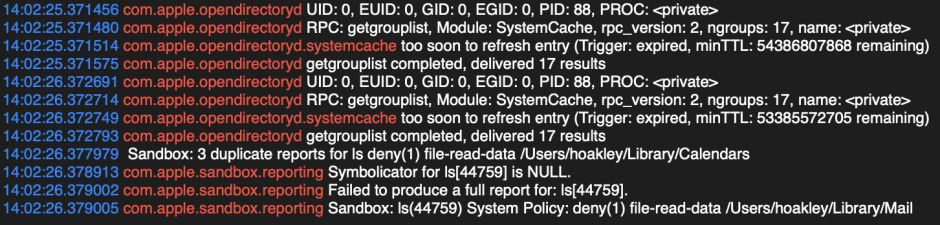
If you then go on to try listing another protected folder, such as ~/Library/Mail, this process is shortcircuited, and the failure of the previous request is recognised:
Sandbox: 3 duplicate reports for ls deny(1) file-read-data /Users/hoakley/Library/Calendars
So the sandbox reports for that too
Sandbox: ls(44759) System Policy: deny(1) file-read-data /Users/hoakley/Library/Mail
This all looks excellent, and presuming that it’s robust, seems good to use. It has two significant issues, though, as far as I can tell:
- The effect of removing
sshd-keygen-wrapperfrom the Full Disk Access list is exactly the opposite of all other items in that list, in that (because of the default behaviour ofssh) it enables access rather than blocks it. - This is the only part of privacy protection in which the default is to allow, without any user warning or interaction.
Together these are inconsistent design which will lead to human error.
I also believe that none of the above is documented anywhere by Apple, which is a major omission for such a key command tool. As a minimum, Apple should document this in:
- the man pages for ssh and sshd,
- the user help for the Sharing pane,
- the user help for the Privacy section of the Security & Privacy pane,
- the full supporting documentation for privacy protection in Mojave, which merits a manual of its own.
Given the design issues noted above and the potential for user error, not to have drawn these to the attention of users and administrators is a serious omission.
