If you’re having problems with keychains, or wish to keep an eye on them, you’ll want to know which tool to use. The short answer is that there are hardly any, although the situation isn’t quite as bad as that may sound.
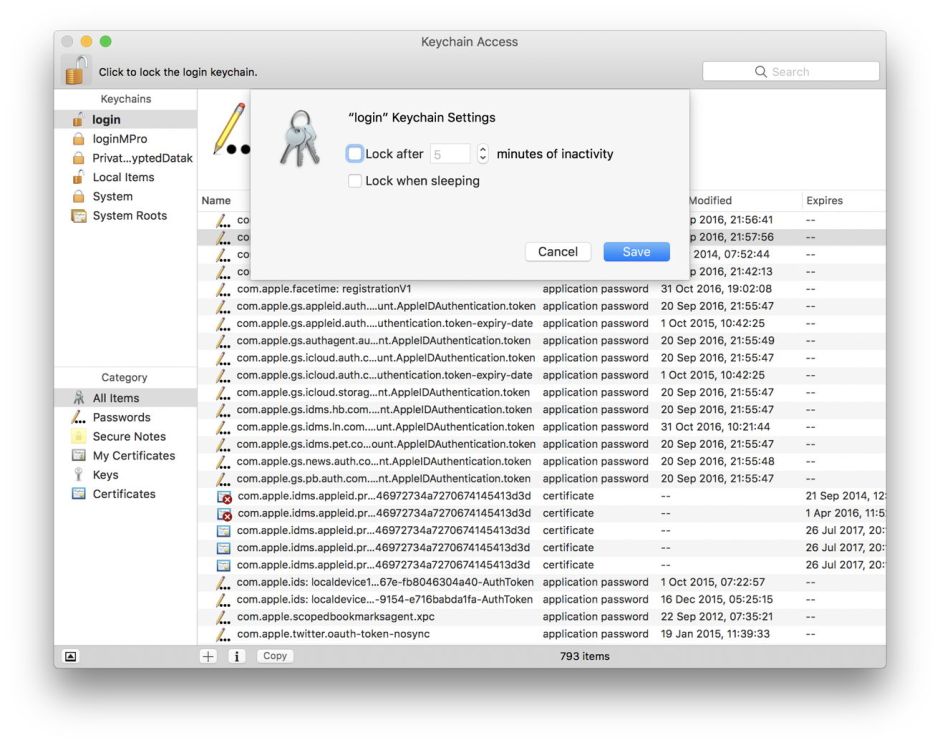
The essential tool is Keychain Access, one of macOS’s bundled tools kept in /Applications/Utilities. This gives access to all the visible private and system keychains on your startup volume, and gives you good control over them. It can be ponderous in use, such as when copying items from one keychain to another, and no longer offers any facility to check or repair a damaged keychain. That ability was removed from OS X 10.11.2 because of a major security vulnerability, and has not been restored since.
If you cannot do what you need in Keychain Access, you may need to look at Apple’s bundled command tool security. This is a formidable collection of functions stuck together by using command verbs, such as list-keychains and unlock-keychain, and not for the faint-hearted. I have described some of its features in this article, but you will need to read its manual carefully using man security.
security doesn’t offer all the features necessary for working with system keychains such as /Library/Keychains/System.keychain. That is the default target of the separate command systemkeychain, which creates system keychains, lets you use one keychain to unlock another, and more. As ever, man systemkeychain provides full details.

My own free tool KeychainCheck, available from Downloads above, lists known user keychains, identifies which is currently recognised as being the login keychain, and informs you of whether it is set to be locked automatically. If you discover a problem, you will have to resort to Keychain Access to do anything about it, even to change the lock settings for your login keychain. KeychainCheck works using three calls to security:
security list-keychains -d user which lists all current user keychains
security default-keychain -d user which identifies the current login keychain, and
security show-keychain-info ~/Library/Keychains/login.keychain-db which shows the current locking settings for the login keychain for the current user.
None of those needs to be run as root.
Few more generic tools offer much for keychains. Even the otherwise comprehensive EtreCheck doesn’t currently attempt to identify which keychains are in use, or which is the default user keychain, and these details are omitted from Apple’s System Information too.
Those wanting forensic analysis should look at the Windows app Password Digger, from Elcomsoft, a commercial product costing around €200. For keychains in El Capitan and earlier, the open source chainbreaker might be useful, but doesn’t appear to have kept pace with Sierra and later.
I have been unable to discover any tool which keeps a watch on keychain activity, such as which apps open any given keychain, but in Sierra at least records are available from the unified log. To filter for them in your active log over the past hour, use a command such as
log show --predicate 'eventMessage CONTAINS[c] "keychain"' --style syslog --info --last 1h
which you can pipe into a file for further assessment.
It is extremely simple to do the same thing in Consolation. Open a new window, and set the Filter to use a pattern consisting of eventMessage CONTAINS[c] keychain, for a period such as the last hour.
You can also browse those entries when you Command-click on a chart bar in Woodpile: simply turn on a custom style for the log, tick the All log entries box, and enter the word keychain as a filter. When you next Command-click on a bar to view log entries for the period set by that bar, you’ll be shown all the messages containing the text keychain.
As I pointed out yesterday, though, using log excerpts will only be useful when running macOS Sierra. High Sierra, at least versions 10.13 and 10.13.1, doesn’t keep useful log records of keychain access.
One major feature which is largely ignored by all the above is the use of iCloud keychains: all are primarily intended for use with local keychains, and none (for example) provides any facility to make a copy or backup of a keychain held in iCloud. As keychains are the most important items held in iCloud which are not backed up there, this is a significant omission. You can make a manual backup, as detailed here.
Some time ago, I started work on a second version of KeychainCheck which uses direct calls to macOS rather than working through command tools, which opens up some more powerful features. I abandoned this largely because the interfaces to macOS calls had not been ported to Swift, and using them was tedious. As there isn’t anything available which will help those with keychain problems beyond the features of Keychain Access, I have started to dust off that project and have already ported it to Swift 4.0 in Xcode 9.1.
If you know of any other useful tools for working with keychains in Sierra and later, please let me know.
