VPN – virtual private networking – used to be a minority pursuit. Originally used mainly to provide secure internet connections between local networks, it came of age when we started connecting to WiFi networks in coffee bars and public places. Now that governments, particularly that in the UK, have given themselves almost unlimited powers to snoop on our internet usage, even more people are using VPN in the hope that it will provide some protection.
The first major blow to this rush to try to protect security and privacy has come in what might readily have become an obscure research paper: Muhammad Ikram and others’ technical analysis of Android VPN Permission-enabled apps, published last November. In case you think this is only about Android and doesn’t concern macOS or iOS, bear with me a few sentences.
Android, and both macOS (10.11 and later) and iOS (8.0 and later), now provide convenient support for developers to use VPN. This is good, but like all features needs to be used correctly. This, and the sharply rising demand from users, has led to a flood of VPN-based apps. Ikram et al. identified and analysed 283 from 1.4 million Android apps on Google Play. A quick search on the iTunes Store shows at least 100 there for iOS, and the App Store offers at least 75 for macOS.

Careful analysis of those Android apps showed that 18% didn’t even encrypt content being transmitted through the VPN tunnel, thus offered no protection at all, and 84% leaked traffic, rendering them almost useless. Many of the apps accessed private data, and a small number actually appeared to be malicious.

In other words, if you have been using VPN on an Android device, chances are that it has at best been of no protection at all, and if you were unlucky in your choice, you may even have ended up using an app which is a threat to your existing security and privacy.
So far, no one has performed comparable studies on iOS or macOS apps, but there is no reason to expect that they should perform any better. Apple does not test the security of claimed VPN connections during its vetting process for apps offered in its iOS or macOS stores.
A decade or two ago, there were well-funded print magazines, several of which had their own labs and staff who were capable of performing many of the tests used in that study. Because we have decided that we, as users, don’t want to pay for those by subscribing to magazines, these no longer exist. We have sleepwalked into a situation where the only organisations with the ability to conduct this sort of expensive study are the major security consultancies, who would need a paying customer.
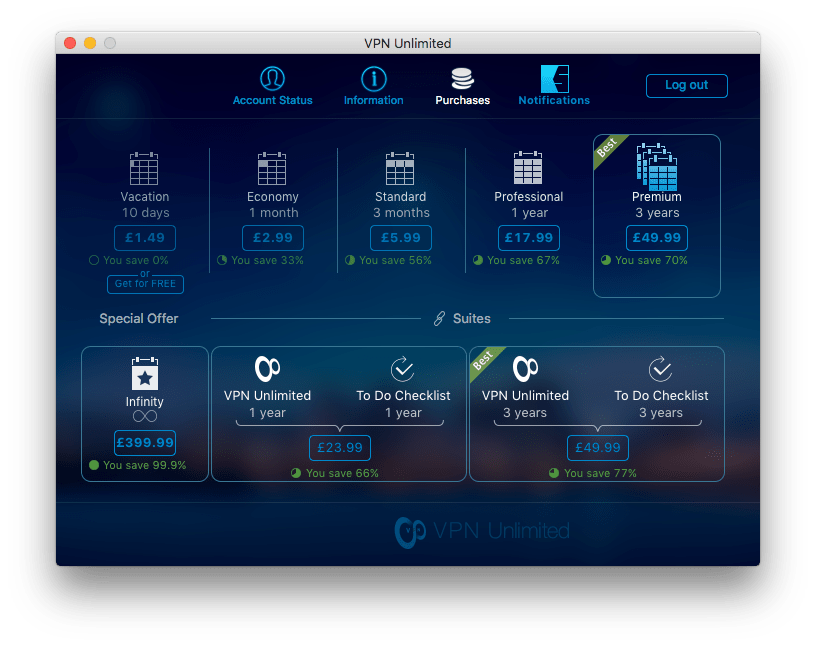
I know how difficult it is to test VPN and similar apps: you can read my brief account of a few products here. Trying to test any significant number of apps with the thoroughness required to determine if their VPN performance is acceptably secure would be a substantial undertaking.

The decline of print magazines and the rise of cheap or even free apps developed by unknown vendors who sell through app stores has effectively made the choice of software a gamble. When it comes to security products, particularly VPN, that means that many, perhaps most, users will end up with software which does not protect them.
Not only that, but as we are most unlikely to know anything about the developers of these products, we could end up using an app which has been deliberately subverted to give access to our data to a criminal gang, or to a security agency anywhere in the world. As the UK’s Investigatory Powers Act (IPA) allows UK security and law-enforcement agencies to require app developers to change their apps so as to give access, we could end up using an app into which a backdoor has been built in complete secrecy.
There is, unfortunately, no simple answer. In other products we would rely on product standards to ensure a minimum standard of acceptable performance, but the software industry has refused to embrace such a system. Although I have questioned the regular use of VPN to provide protection from snooping under the IPA, it remains essential when you are using public-access WiFi.
Perhaps now is the time for Apple, Google, Microsoft, and others who operate stores which sell these products to step in, test the products properly, and provide us reassurance. Or maybe we just have to accept that the current model of app stores is inappropriate for security products.
