There are many very good, sometimes even mandatory, reasons for wanting to ensure that no one can eavesdrop on your Internet communications.
Among the most frequent situations are:
- transferring sensitive private, personal, or financial information via a public WiFi access point,
- connecting two separated networks which must not become vulnerable,
- connecting a mobile system to a static network, e.g. to obtain files using your iPad when working away from your business or home network,
- transferring over the Internet any data which are subject to the Data Protection Act or similar law,
- working in an area where Internet security is uncertain or unreliable, and transfer could be intercepted (this could now include many former Western democracies!).
VPN
The standard way to provide secure, encrypted communications over the Internet, between one point and another, is by creating a Virtual Private Network (VPN) between two routers, computers, or devices, in any combination. VPN is not a single protocol, but a family based on authentication, tunneling, and encryption.
Authentication ensures that the two ends of the VPN connection are who they say they are, and can use any of a range of different techniques, typically passwords or digital certificates.
Tunneling is the system (protocol) used to merge all network traffic into a single connection, running between the two termination points. This usually involves encapsulating normal IP packets inside a special IPSec packet (in the case of the IPSec protocol), for example. The protocol also ensures message integrity, so that packets cannot be tampered with in transit.
Encryption ensures that the contents of packets transferred between the termination points cannot be inspected en route. Anyone intercepting them will be unable to decrypt the packets, and thus the content will remain secure in transit.
When connecting two networks, VPN is often implemented in their routers, which are the termination points. Many businesses and other organisations maintain extensive, even long-distance, inter-network VPN connections as key links in their IT systems.
Greater flexibility is available from VPN implemented in software, which enables you to move termination points such as iPhones, iPads, and laptop Macs around, making Internet connections through local access points.
VPN with a proxy server
VPN can also be used to connect a system to a remote proxy server. You might want to do this to enable you to access the Internet more generally from a location where security is uncertain or unreliable, or you have to use a public access point which may be eavesdropped. Anyone intercepting or monitoring your communications will then be confronted with streams of encrypted packets passing to and from the proxy server. They will be unable to obtain details of the connections which you make (other than with the proxy server), and unable to capture the content of those packets.
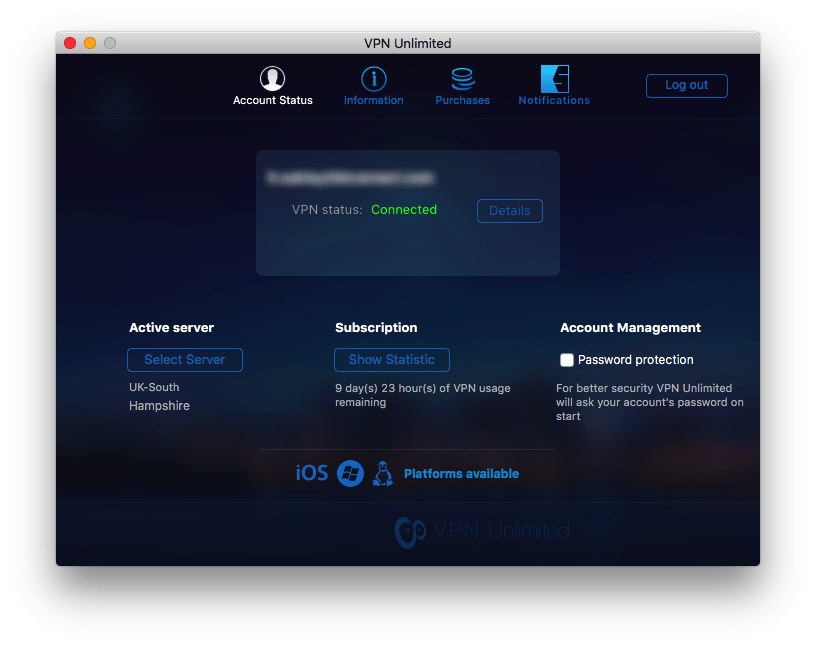
The most straightforward VPN and proxy service which I have found is that of VPN Unlimited (App Store, free with in-app subscription purchase). This is available for most platforms, including OS X, iOS, even Linux, and provides you with a ten-day trial which you can access after logging in using Facebook, Google+, or KeepSolid credentials.
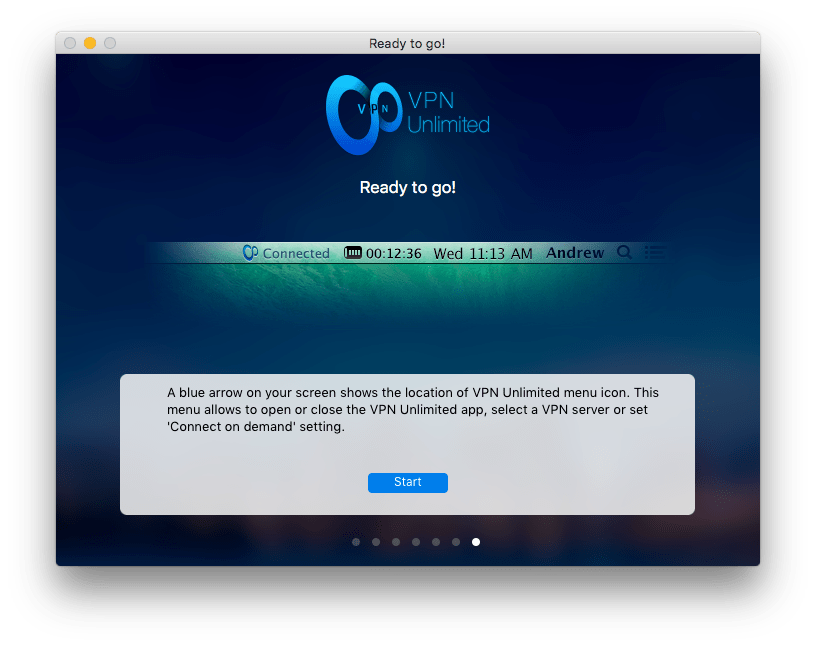 On opening the app for the first time, it walks you through setup and account creation in the most straightforward manner possible. This does get slightly involved, in that it links to your browser to download its profile, which then appears in the newly-installed Profile pane in System Preferences.
On opening the app for the first time, it walks you through setup and account creation in the most straightforward manner possible. This does get slightly involved, in that it links to your browser to download its profile, which then appears in the newly-installed Profile pane in System Preferences.
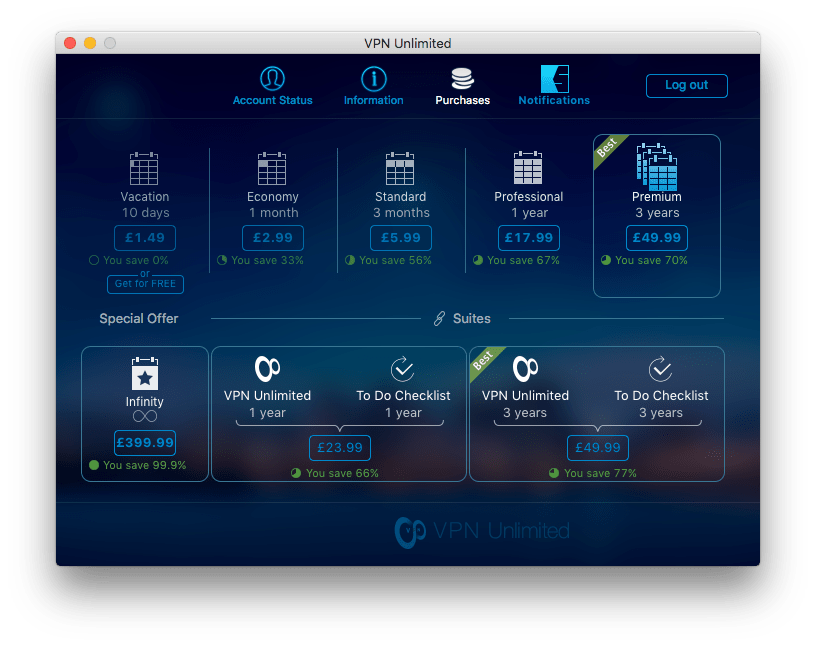 It offers a range of subscription plans from within the app, with clear pricing information, ranging from a ten-day holiday for £1.49 to Premium at £49.99 for three years, and Infinity for £399.99.
It offers a range of subscription plans from within the app, with clear pricing information, ranging from a ten-day holiday for £1.49 to Premium at £49.99 for three years, and Infinity for £399.99.
 By default, VPN Unlimited opens its proxy connections using PPTP, which gives your ISP continuing access to connection information and even content, but does secure against normal eavesdropping. Most users will surely want to switch that to full IPSec-PSK, which should be robust against most attempts to discover your connection information and content. However this is limited to 128-bit encryption.
By default, VPN Unlimited opens its proxy connections using PPTP, which gives your ISP continuing access to connection information and even content, but does secure against normal eavesdropping. Most users will surely want to switch that to full IPSec-PSK, which should be robust against most attempts to discover your connection information and content. However this is limited to 128-bit encryption.
The service provider has servers located in a wide range of countries, including several in the UK, and good coverage throughout Europe and the USA. This may change in the event that the IPA is adopted in the UK, as any UK operations might bring it within the scope of that legislation.
 VPN Unlimited is not difficult to turn off or disable, but does tend to leave residues sticking in some odd places, such as VPN as a service in the Network pane. These do not appear to cause any problems, though. Checking sniffed packets whilst its IPSec service was active confirms that it appears to be doing all the right things, and the only network connections were made with the chosen proxy server, and using encrypted packets.
VPN Unlimited is not difficult to turn off or disable, but does tend to leave residues sticking in some odd places, such as VPN as a service in the Network pane. These do not appear to cause any problems, though. Checking sniffed packets whilst its IPSec service was active confirms that it appears to be doing all the right things, and the only network connections were made with the chosen proxy server, and using encrypted packets.
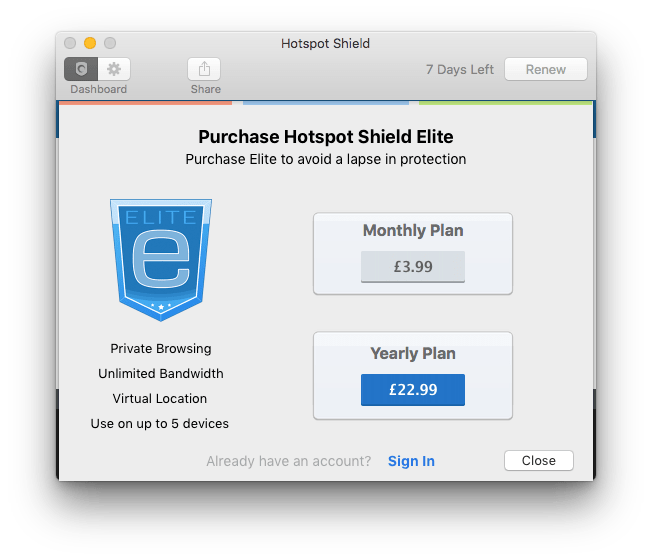 There are several other attractive products available in the App Store and elsewhere, usually free with in-app subscription purchase. I also attempted to use Hotspot Shield VPN, but it does not have any initial setup assistant and did not seem prepared to create an account for me. Your experience may be better.
There are several other attractive products available in the App Store and elsewhere, usually free with in-app subscription purchase. I also attempted to use Hotspot Shield VPN, but it does not have any initial setup assistant and did not seem prepared to create an account for me. Your experience may be better.
Using Tor’s anonymisation
If you want to go the whole hog and anonymise your Internet connections altogether, Tor is a free service which aims to do that. However even when packaged into an App Store app like XustoAnony (£3.99), it is not for the faint-hearted.
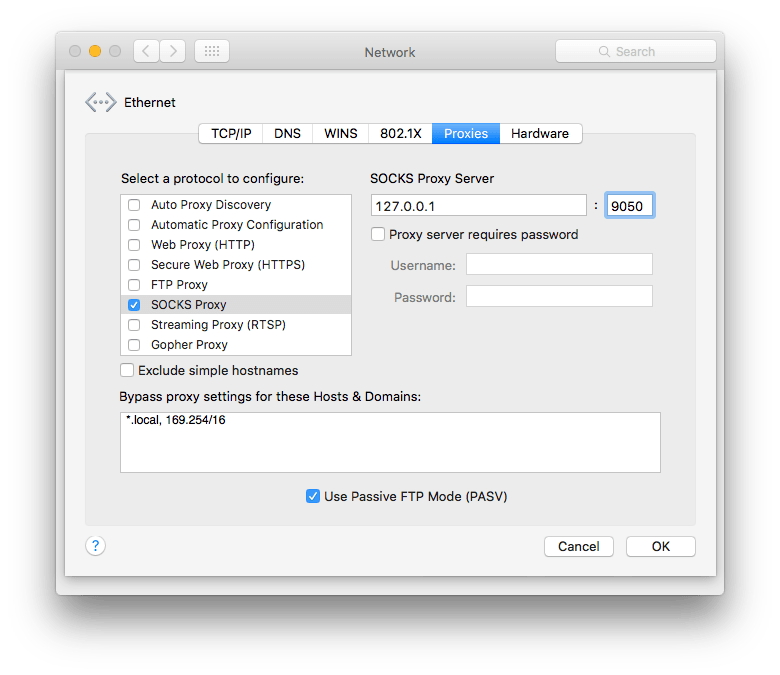 XustoAnony uses Tor v0.2.6.10 with OpenSSL 1.0.1p, which is configured by the app and settings in the Proxies tab of your Network pane. Despite following the instructions, packet sniffing showed that traffic remained unencrypted and was not directed at Tor servers. If you want to use Tor, then you will have to get your head around it properly and take great care in setting your connection up.
XustoAnony uses Tor v0.2.6.10 with OpenSSL 1.0.1p, which is configured by the app and settings in the Proxies tab of your Network pane. Despite following the instructions, packet sniffing showed that traffic remained unencrypted and was not directed at Tor servers. If you want to use Tor, then you will have to get your head around it properly and take great care in setting your connection up.
Tor offers its own browser here, which comes with a list of issues which you will also need to address before its anonymisation should work.
Secure messaging services
VPN to proxy servers and Tor are primarily aimed at protecting web browsing, and do not themselves help much in communicating directly with others. You can of course encrypt the contents of email messages, but sent using regular mail service providers the message itself is still logged and available. If you need to be able to communicate more securely, then the Electronic Frontier Foundation (EFF) Secure Messaging Scorecard is a good place to start.
The most obvious, but confined to iOS and OS X systems only, is Apple’s iMessage/Message service, bundled free with Apple’s operating systems. This uses proprietary connections and TLS end-to-end encryption, which Apple has declared to be secure even to its own efforts to decrypt. However it may be vulnerable to spoofing attacks of the kind now known to be used by security and law enforcement agencies around the world. It appears very unlikely to be vulnerable to mere criminals, though.
There are many third-party services on offer too. The best-known is probably WhatsApp, which runs cross-platform on a wide variety of phones, and now has a third-party OS X client. However the EFF does not rate it at all well.
Wire is a new contender which is cross-platform on phones (including iOS) and computers, including Windows and OS X, with its own free apps. This claims to be fully protective under EU privacy law, but details of the connection and encryption used are currently lacking. It will be very interesting to see how it shapes up.
Effects of the UK’s draft Investigatory Powers Bill
The proposed provisions in this draft Bill (most of which are already apparently in use) fall into three broad categories: mass surveillance, Internet Connection Records, and electronic wiretaps. All three are directly affected by VPN to a proxy server, anonymisation, and secure messaging.
As currently worded, it is likely – should the draft Bill become law – that UK service providers of all types will be instructed to decrypt and detail any connections made, particularly under electronic wiretapping. However it is hard to see how a company which is not UK resident, has no UK operations, or UK-based equipment, can be forced to do so. It will be very interesting to see how this aspect of the legislation develops.
A matter of trust
Finally, you have to put trust in the service provider. It is not just a matter of their using robust encryption and protocols: in using a service you are assuming that all the hidden things which go on in the creation and transmission of networking packets are working right. And that the service provider is not a front for a security agency, or working with such agencies. That perhaps is the crux.