Most Macs have got vulnerabilities, and the most worrying are those that we don’t know about. Well-run networks in businesses should keep a careful watch on those vulnerabilities using a network audit system like Tenable Nessus.
Nessus Professional, the most popular product for business and organisational networks, will cost you an annual subscription of $2190, so unless you have got money to burn, using that on a home network is out of the question. But Nessus Home is available free of charge. It is the same basic product, limited to scanning a maximum of 16 IP addresses, and is for personal use in a home environment.
To use Nessus Home, you’ll need to obtain an activation code via Tenable’s website, and download its OS X installer.
Installation is a bit fiddly and left me with a feeling of discomfort. The installer which you download is but the start of the process: this eventually takes you through to the Nessus web interface, which then downloads further and unspecified packages and installs them somewhere. For a security tool this is worryingly opaque and obfuscated, and I cannot see any convincing reason for having to do it that way.
Once installed, Nessus is driven from its web interface, using your browser, with full support for Safari and others. Although I am not a fan of such interfaces, in this case it is only very slightly awkward in use, and I soon got used to those minor quirks. Its web interface is generally well designed and implemented.
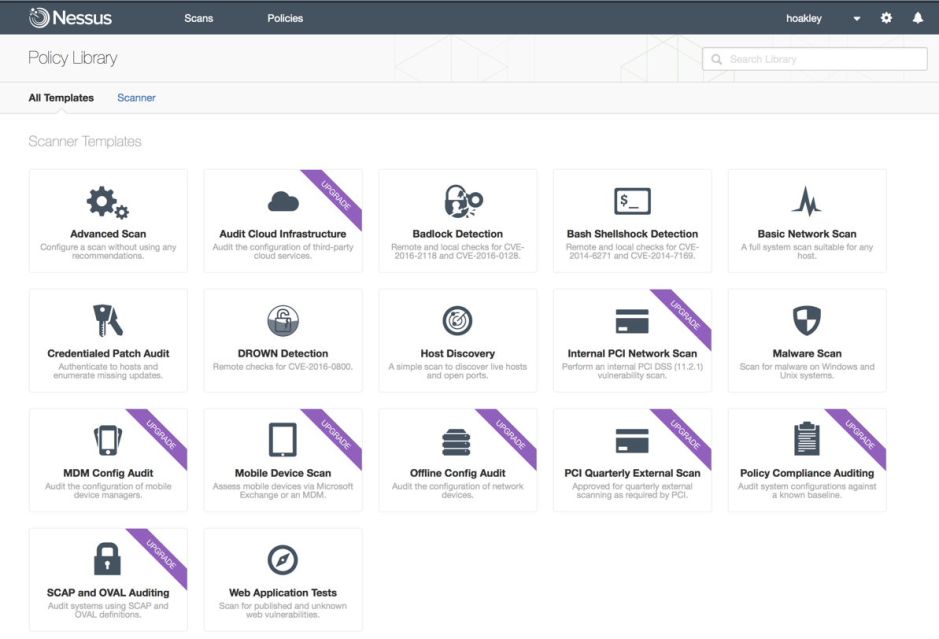
The standard range of scans and tests is impressive, although the free version offers several as upgrades and not within its free bundle. The most important for Mac users are likely to be the Basic Network Scan, which is anything but basic, and the Malware Scan. Mobile device scans do not include iOS (or tvOS or watchOS) devices, which I will return to later.
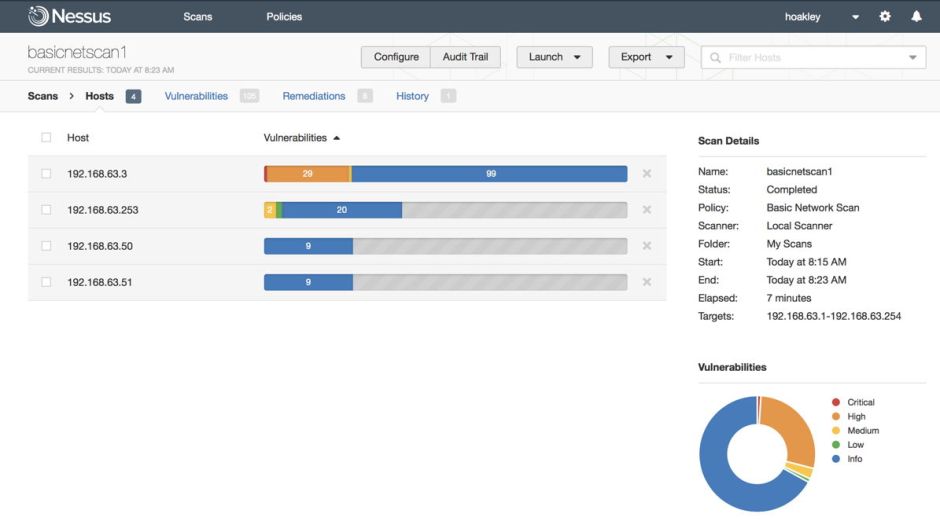
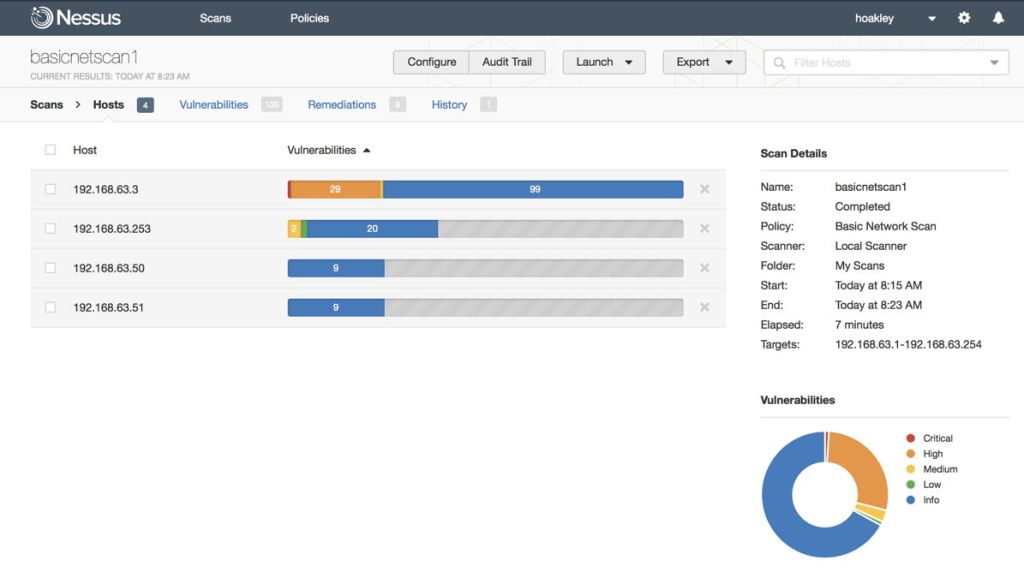
Running the Basic Network Scan takes several minutes even on a small network, and is extremely thorough. If security matters throw you into panic, it’s at this point that you will probably need to take a long, calming walk: vulnerabilities do not mean that your Mac is about to be taken over by hackers. It’s an unfortunate tendency in the security community to hype problems into alarming terms, and Nessus is no exception to that pattern.
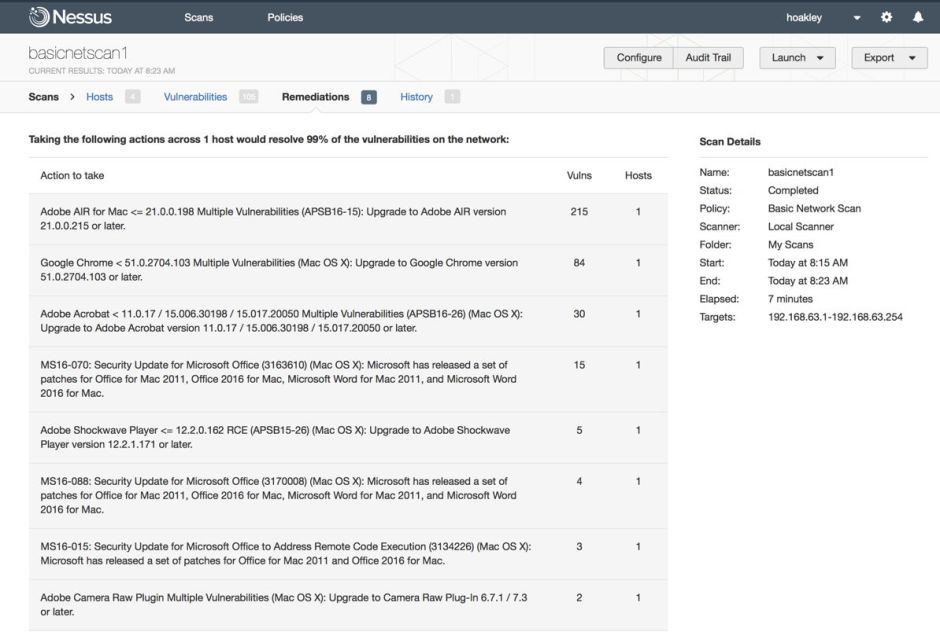
Although it is good to wade through the list of vulnerabilities detected, you should really be more interested in the listed remediations: these are the things that you can do something about, normally fairly easily. And on most Macs, they involve updating products which you probably haven’t used for a while, and have fallen a bit behind in updates. I don’t know of any other tool which can check installed software in this way.

To illustrate the need to interpret its results, here is my one Critical vulnerability: the fact that I still have Adobe Photoshop CS6 installed and refuse to pay Adobe Tax to upgrade to CC. While this is a vulnerability, it is one which I am living with, and wouldn’t want it any other way.
Nessus relies on auditing the apps and other software on your Mac, then looking that up on Tenable’s vulnerability database. This works best for the major business apps from Microsoft, Adobe, and the like. I am less convinced that it would, for instance, pick up an old version of an OS X only app from a small vendor which still has a Sparkle update vulnerability (not requiring HTTPS connection). You could, though, argue that such minor apps are far less likely to be exploited.
For OS X, Nessus Home is an excellent and thorough tool which should be installed on all home networks which do anything beyond the most trivial. With support for OS X, Windows, Linux, and Unix systems, it is the best way of ensuring that your computers are as secure as you wish to make them.
The big problem with using Nessus is iOS. Because iOS devices are inherently mobile, they will come and go from a network, making their scanning a hit or miss affair. So instead of tackling those devices, Nessus approaches them through mobile device management systems, for iOS, Apple Profile Manager. In other words, it doesn’t scan the device, just its profile stored on your Mac.
One potential answer might be an iOS app, but because these have to operate within their sandbox, iOS security would deny them access to almost everything they would need to do their job. It would be really great if Apple and Tenable were to get together to put a Nessus client into iOS itself, but I can’t see that happening just yet, which is a shame.
If you care about the security of your home systems, then you should install Nessus Home and use it.