We all put blind faith in that little padlock icon which appears in our browser to indicate that this connection is being delivered securely, using the HTTPS protocol and SSL (which is now actually TLS). It is then OK to enter credit card details, sensitive personal information, and whatever else is needed to get the goodies which we want to order, or to obtain the service we want.
SSL has had its vulnerabilities, but they are old hat now, and the site that we are connected to couldn’t possibly, could it?
If I have sown seeds of doubt in your mind, perhaps the burning desire to check that your browser and the sites to which you connect it are secure, then look no further than Qualys SSL Labs – and yes, that does run securely, as the padlock points out.
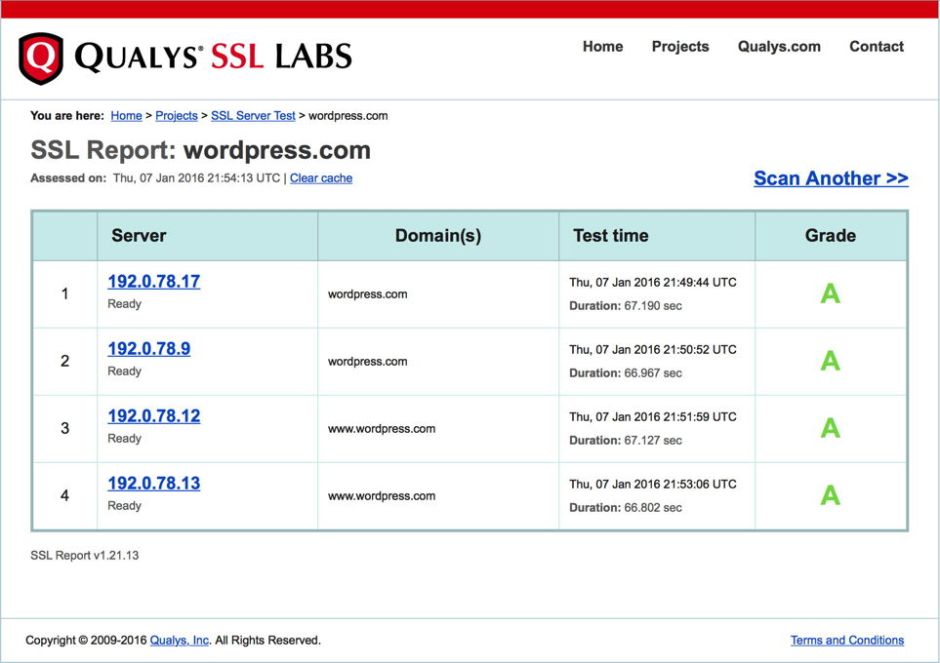
 The top option allows you to check your own sites, such as eclecticlight.co. As that is hosted by WordPress, it results in a check on the WordPress hosts, which are encouragingly excellent.
The top option allows you to check your own sites, such as eclecticlight.co. As that is hosted by WordPress, it results in a check on the WordPress hosts, which are encouragingly excellent.
 You can also use the same page to check other sites, such as those of your ISP. If you do, be prepared for some shocks, as it is amazing how many fall far short of WordPress’s excellence.
You can also use the same page to check other sites, such as those of your ISP. If you do, be prepared for some shocks, as it is amazing how many fall far short of WordPress’s excellence.
 The next option lets you check your browser, in my case Safari 9.0.2 in El Capitan 10.11.2. This report is long and gets rather overburdened with acronyms and the like, but basically it says that it suffers from none of the significant vulnerabilities, supports robust secure connections, but could do better in some details.
The next option lets you check your browser, in my case Safari 9.0.2 in El Capitan 10.11.2. This report is long and gets rather overburdened with acronyms and the like, but basically it says that it suffers from none of the significant vulnerabilities, supports robust secure connections, but could do better in some details.
 The third option gives you a broad overview of how well the 141,890 most popular web sites perform. This might seem like nerd fodder, but there are some chilling figures which might make you much more careful in putting blind faith in that comforting padlock icon.
The third option gives you a broad overview of how well the 141,890 most popular web sites perform. This might seem like nerd fodder, but there are some chilling figures which might make you much more careful in putting blind faith in that comforting padlock icon.
Using the figures published on 3 December 2015:
- 27% of sites only achieve a grade C overall;
- 18.5% – that is nearly one in five – sites achieve a miserable failure of F;
- 326 sites, admittedly only 0.2%, are still vulnerable to the Heartbleed bug, which was fixed in April 2014;
- nearly 10% of sites only support SSL 2.0, which was replaced in 1996 and officially deprecated in 2011;
- 90% of sites are still vulnerable to the BEAST attack, which was ‘solved’ in late 2011;
- over 15% of sites only support the old SHA-1 hashing scheme, which browsers will soon refuse to accept, resulting in those sites becoming blocked.
(There are many excellent resources also available in the SSL Labs for those operating their own servers, and other interested parties.)
It is very easy to work up a head of steam about major security breaches such as those which affected TalkTalk, Ashley Madison, and most recently Steam. But when so many sites still use protocols which were outdated twenty years ago, and are still vulnerable to widely-publicised attacks which were addressed over 4 years ago, it makes me wonder whether it is time for action against their operators.
Shouldn’t this be something which, for example, the several EU and national organisations responsible for data protection should be leading on? Don’t they have a protective, preventative role too?

