Every year we are told that Mac security has finally become a real issue. Is software a simple solution, or do we each hold the key to our own security?
It is shockingly easy to get many computer users to part with vital secrets such as their passwords and personal details. Time after time, when security professionals test how easy it is to penetrate a corporate system, they demonstrate that the easiest portal is to trick a user into revealing how to access their account. Humans are invariably the weakest link, for which no end of smart hardware and sophisticated software can compensate.
Good criminals know this well. Although you may think that you can spot phishing from genuine email, and a bogus website from the original, every day thousands get it wrong, and fall into the clutches of crooks. Sometimes they are protected from themselves by security or anti-virus software, but all too often such measures kick in too late. Other users assume that the obstructive security policies of their network will protect them from all ills, only to discover how a cunning intruder can sneak through, exploiting that confidence.
Psychology and social engineering
The effective criminal understands your motives and desires, so as to see where they can be exploited. Many people cannot resist the temptation to make money, particularly if they think they can do so with minimal effort, and without paying tax. Although you may think that you can resist invitations to profit from a huge legacy, or ill-gotten gains in the Middle East, the crafty criminal is unlikely to offer anything so obvious. They may offer modest discounts, desirable software products at massive reductions, or PDF versions of key books that you are searching for.
Like a good pickpocket, they love to catch you when you are concentrating on something else. The occasion when my charge card details were stolen online, I was frantically trying to book accommodation for quite a large group in London, to enable us to catch an early Eurostar train to France. One hotel looked ideally situated, but I could only discover whether they had vacancies by providing full booking details, including payment information. Within 48 hours, in a series of transactions handled through weird businesses in Australia, my account was debited over 10,000 Australian dollars before its fraud detection service cut in and blocked the card.
Sometimes you have to work close to danger. In the recent past I started to study the Georgian language, purchasing books and other items from their only sources in Georgia. Rather than using my charge card, with its invitingly high credit limit, I have instead used a card with a low limit, consequently lower capacity for criminal abuse.
I am also fastidious about selecting the online shops with which I trade, creating accounts and sounding them out before providing any card details. If you travel in such countries or need to do more extensive business, consider using local banking and payment services that limit your liability even more, or discuss safe solutions with your card provider.
Phishing and email scams
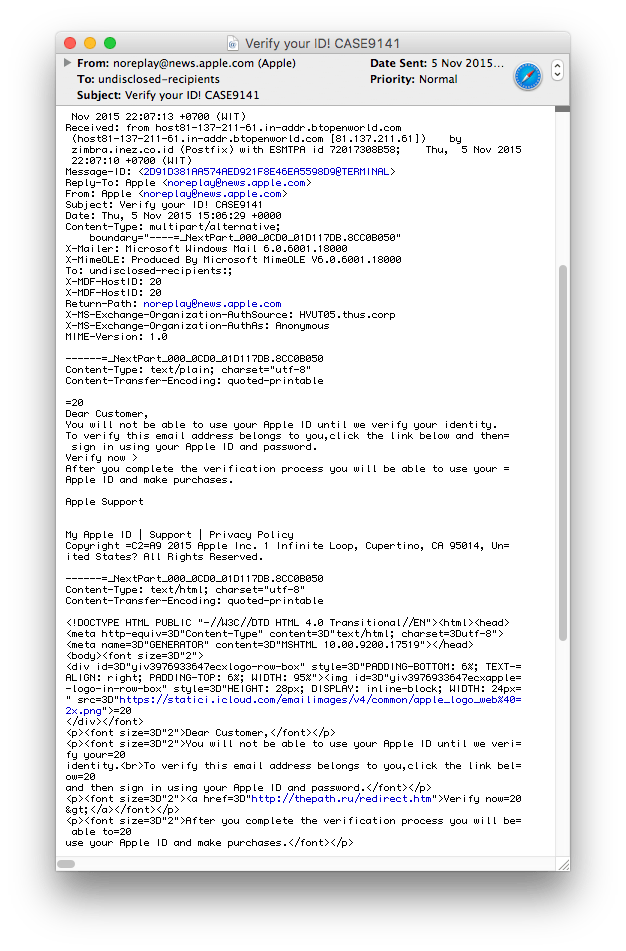
Forging emails is remarkably easy, and it can be difficult to see clues to their real nature. Here you need to understand the system of domain names and the contents of Internet headers, which all good mail clients can display as an option. Many of us have received highly plausible emails purporting to offer an Apple discount card, or threatening to block our access to iCloud documents if we do not supply our connection details urgently.
Their subtle giveaway lies in their origin, from addresses such as apple@store.com, rather than an address within Apple’s domain of apple.com. Recently several have been forged as coming from noreplay@news.apple.com, which is a more credible but still odd address. If in doubt, check the location of the servers that it has passed through and compare these with known locations, using the Lookup and Traceroute tabs in Network Utility.
Downloads
Downloading software from untrusted sites is another excellent way of getting into trouble. Still images and movies can contain malware, and when you search for them using apparently reputable engines such as Google, some of those hits will contain malicious material. Watch carefully for the address shown for each item and avoid those looking suspicious, with unusual domain names and countries such as .ru (Russia) and .cn (China): see the official Root Zone Database. Insist on obtaining software updates by secure connections (HTTPS) from trusted sources, anthologies like Download.com, or checked vendor sites. Even these may become forged or diverted, so be alert for fakes.
You must understand the goals of those trying to catch you out: to get you to surrender card, bank, or personal details, or to get malware onto your Mac. By and large this is now accomplished via HTML, sometimes by exploiting security flaws in other file types such as Office documents, or PDF. They are trying to trick you into opening their mail enclosure or web page, which then uses JavaScript, Java, Flash, or similar to do the dirty to you.
Keeping OS X, ancillaries such as Java, plugins, and your applications up to date is essential. Although there is usually a time-lag between exploitation of a vulnerability and release of a patch to address it, if you are still using OS X 10.5 with its multitude of known vulnerabilities, you are a sitting duck every minute that you are online. Gone are the days when the wise would let early adopters find the flaws in updates over a couple of weeks before deciding to upgrade themselves. That fortnight is now an unacceptable period at risk, 14 days of unnecessary exposure.
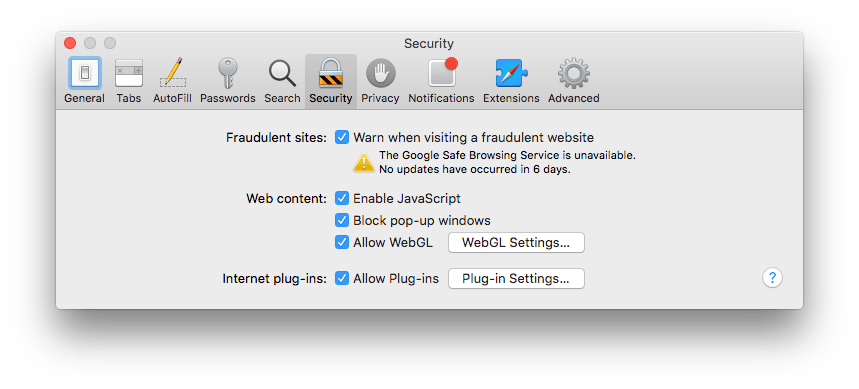
If you don’t need Flash or Java, or any browser plugin or extension, disable and remove them to ensure that nothing can take advantage. Don’t leave old exploited versions hanging around just in case you need to enable them.
Software protection
If you do decide to install security or anti-virus software, you must keep it completely up to date, and it must augment rather than replace your human security. If you need an update subscription to keep your protection current, budget for that and keep the subscription up. If you cannot, uninstall the product as it may cause system problems as well as becoming increasingly useless. Beware of risk compensation – the ‘Volvo syndrome’ – whereby increasing your absolute margin of safety induces you to compensate by behaving more dangerously.
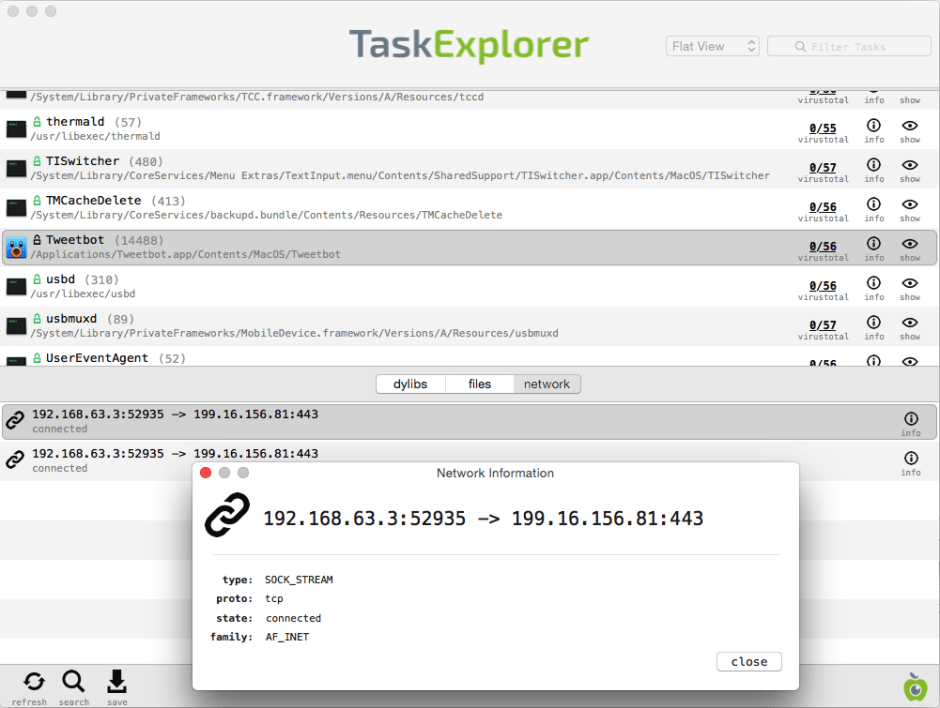
You should also look at less conventional methods of protection. Little Snitch will watch for software making outbound connections. These are normally hard to handle in your firewall settings, as they could become a serious obstruction to your normal Internet use. Little Snitch traps these well, and could alert you if a Trojan installed on your Mac tried to contact its controller, for instance. However this is very late in the day, and your efforts should be focussed on preventing the Trojan from getting near your Mac in the first place.
Powerful protection can also be so restrictive that you are driven to subversion. In the days of Classic Mac OS, some widely used commercial virus protection behaved so painfully whenever you inserted a floppy disk that most users had to disable it before doing so; many then left it disabled afterwards. This was doubly dangerous, as they were left without the protection that they assumed was in place, and if they engaged in risk compensation on the assumption that their virus protection would save them, they were easy victims.
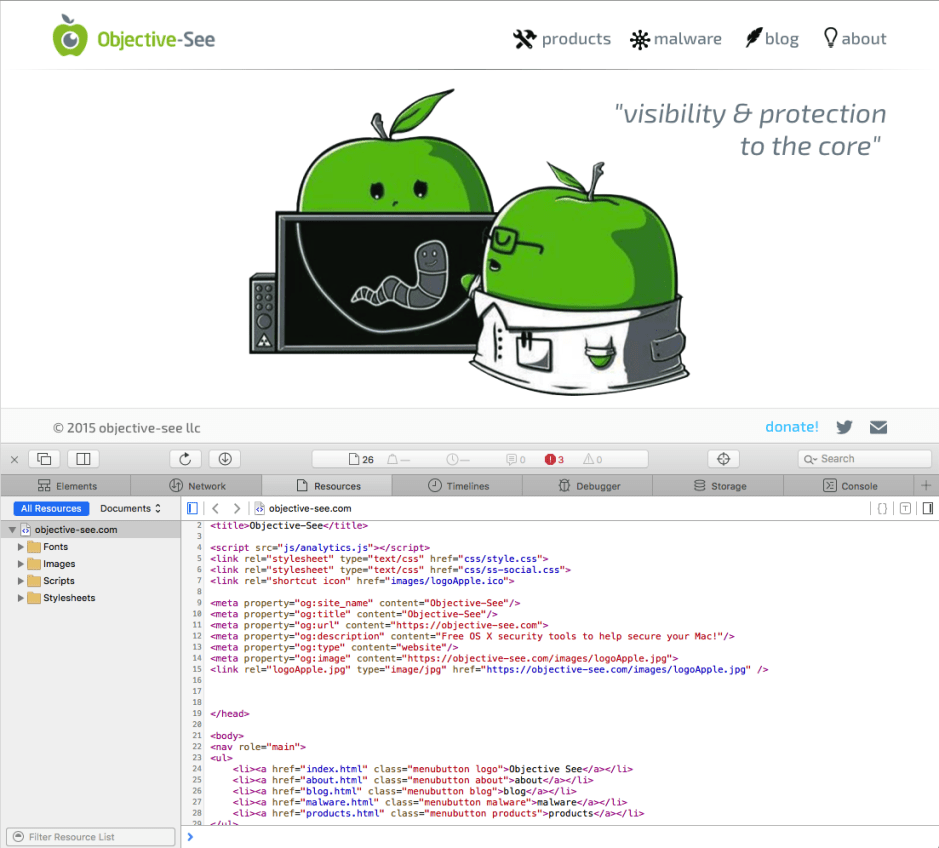
Modern protection need not cost much, or even anything, and the best is tailored to where exploits might occur. One excellent resource is Objective-See, which offers a range of free tools which scan the most vulnerable parts of OS X and your apps, to check for suspicious signs. Use those tools to check your Mac periodically, and run them whenever you think you may have had a near miss, perhaps with a website that wasn’t what you thought it was.
Further helpful articles cover firewalls and important protection measures, wireless network security, and additional SIP measures in El Capitan.
There are no instant answers to securing your Mac and iOS devices from attack. But whatever you decide to do, you must be honest to yourself about the risks that you run, and how you can best avert them. Never underestimate the importance of the human element, as it is that which is most readily exploited.
Technique: Defensive Mail
Malicious mail can either put something nasty in your mailbox, delivering the malware straight to you, or lure you to connect to a malicious site or send details that can be exploited. Either way you must collect and read it in a modern client with a sound first level of protection. Old clients have flaws in them that could expose you to risk when receiving or reading mail.
Although aesthetically pleasing to view RTF and HTML messages fully formatted, and with images displayed in place, this increases risk. Some mail clients, such as the free Mailsmith, cannot themselves display anything beyond plain text; they strip text embedded within other formats, allowing you to screen the mail before you choose to view it. This also helps you sort through your mail very quickly, without having to wade through prettified content.
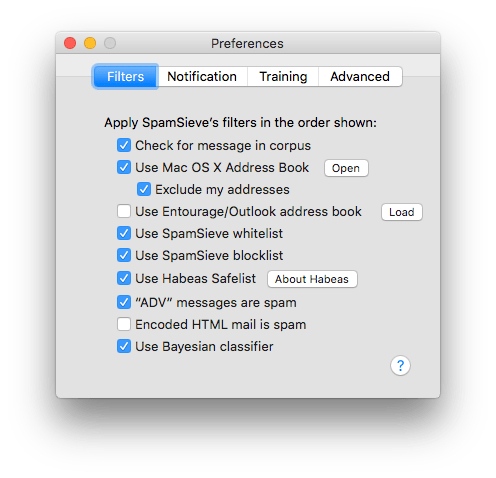
Sorting mail automatically into wanted and unwanted (spam and scam) mailboxes is even more useful, but not a perfect science. The best spam filters do not destroy or bounce spam, and must be trained by sorting received mail manually. Training is essential to achieving good accuracy, and you should not simply delete spam that is not correctly identified as such. The better filters, such as SpamSieve , work across several different mail clients, and following training can achieve 99% accuracy.
Learning to understand mail internet headers also takes a little time, but has worthwhile rewards. Look at those in typical genuine messages (including benign and wanted bulk mail), and those in obviously malicious mail. You will see that some elements are easily forged, but tracing the series of servers through which the message has passed is usually the best way to discover that they first appeared in a system that has nothing to do with their claimed origin.
If you are suspicious of any message attachment, don’t open it: it is likely to contain malware, and even if your version of Adobe Acrobat or Microsoft Office is fully patched, it is an unnecessary risk. Trash the message complete with its attachments as soon as you can.
Technique: Wise Browsing
There are three key elements to enjoying the riches of the Internet without fear of attack. You need to configure your browser appropriately for the sites you might encounter, assess the risk of every click, and handle downloads wisely.
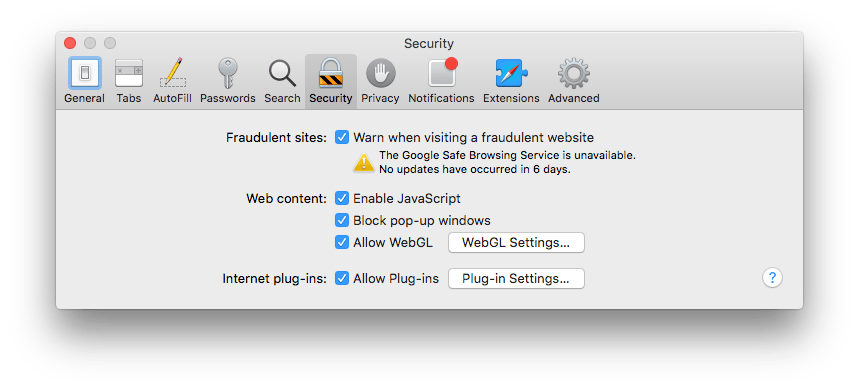
Browsers have security settings which should not be left at their defaults. The most dangerous option is to open downloaded files automatically, which you should never do. In ordinary use, you will almost certainly need to accept cookies, enable Java and JavaScript, and popups. However when you think you could be entering higher-risk sites, such as those in Eastern Europe, Asia, and the Far East, tighten your settings up, possibly turning those off for the time being. Changing settings on the fly is unusual, but an excellent habit to get into.
Enable the status bar and other tools that display addresses of links, so that you can screen where any click will take you. Beware of links that take you outside the current domain, particularly if you do not recognise the address. If you remain keen to follow a link but are deeply suspicious as to where it will take you, view that page’s source and see if you can be reassured or alarmed by what you see. Avoid at all costs being hijacked to a distant malware server.
Anything, even images and web pages, that you download from a site that you do not have total trust in should be carefully checked. Most anti-virus software lets you set up a watched folder, whose contents will be automatically scanned. Apply that to your Downloads folder (or the alternative that you have set in your browser’s preferences) so those files will get the once-over before you try to open them on your Mac.
Updated from the original, which was first published in MacUser volume 28 issue 13, 2012.