Wired network security is straightforward to set up and monitor. Turn on the WiFi, throw in a few iPhones, iPads and unwired laptops, and you could easily end up with unwelcome visitors. Is it possible to make wireless networks really secure?
A few years ago, most commercial and institutional computer networks could make a good case against supporting any form of wireless connection. With a steady stream of security breaches, and frequent press reports of WiFi hacks and vulnerabilities, the simplest answer was no access. Now, with the popularity of the iPhone, iPad and other devices that make good business use of WiFi, such a Luddite defence has become untenable. If your network is going to move with the times, it has to support wireless clients.
The threat
Breaking into a wired network without having physical access to the premises is an old and well-understood crime. There are really only two classes of approach: penetrate the firewall, or get a user to run malware, either as a downloaded Trojan, or by connecting to a malicious website.
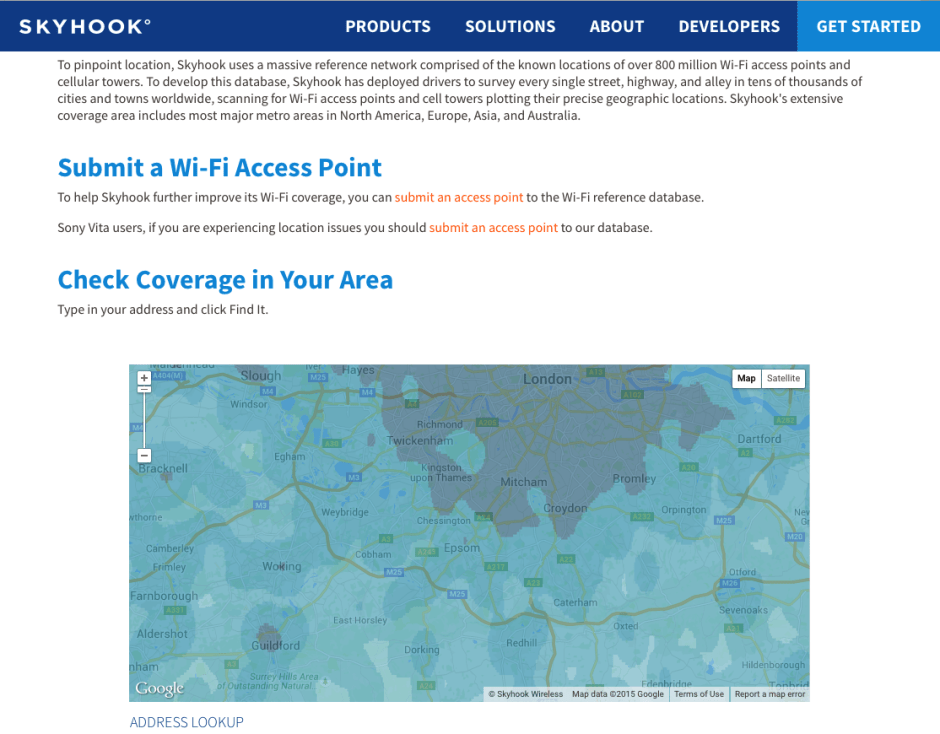
The moment that you turn your first WiFi base station on, it is advertising the presence of an invisible and ill-defined area within which potential intruders could hack their way into your systems, and act as if they were physically connected. Not only that, but Skyhook Wireless and others who ‘wardrive’ around compiling lists of wireless networks could sooner or later add your access points to their databases – hardly a help to your security.
WiFi-enabled devices have also become immensely popular. In addition to many mobile phones and computers, you can readily purchase cheap devices that can detect, even probe and analyse WiFi networks. Would-be intruders no longer need to be technically knowledgeable or well-equipped to take on your security measures. However the specialist criminal can now break almost all wireless security, even many configurations that use the more secure WPA2 protocol.
The strength of radio waves is that they normally disseminate quite widely; without this, radio and TV could not have worked. But it is also a great weakness if you want only certain individuals to be able to use a radio signal. Military communicators have tried all sorts of ingenious tricks to lock the enemy out, encrypting signal content, dancing very quickly between different frequencies, and so on, but none has proved invulnerable. The bottom line is that any networking performed using radio transmissions is inherently vulnerable to intrusion.
Location
If your home or premises are in the middle of hundreds of acres of roadless open countryside, then the chances of someone passing by and trying to crack their way into your wireless network are pretty slim.
But most people live and work in much more crowded surrounds, with public foot and vehicle access just a few metres away from where they will site a WiFi base station. In these circumstances you should expect people to attempt to intrude. Where homes, shops and offices are quite dense, other legitimate WiFi users and networks may well overlap in their coverage; good WiFi security is then important to prevent inadvertent or non-malicious intrusion.
Power and spillover
When you need wireless networking, only use it where necessary, and site your base stations to minimise signal leakage outside your premises. Don’t flood your whole street with full-strength signal blasted out from high-gain aerials. Remember that wireless networking relies on low microwave radio frequencies, which are essentially line-of-sight and attenuate rapidly when passing through substantial structures such as metal, brick, and stone. Put a base station near an external window, though, and its signals will spill out until blocked by the next solid wall.
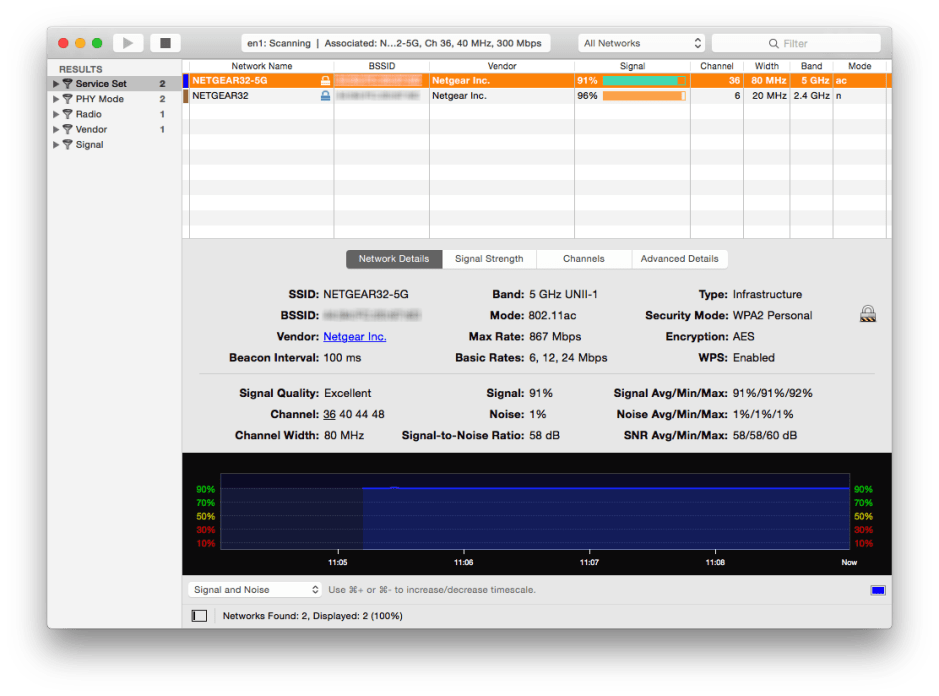
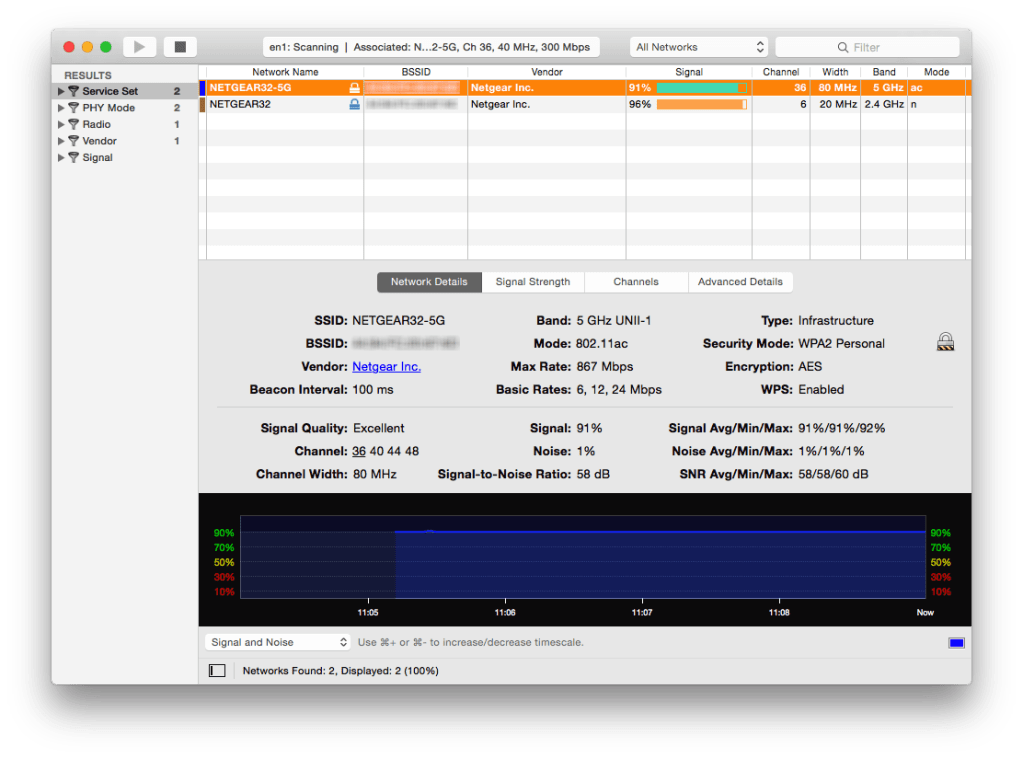
Many WiFi base stations and others now have transmit power controls allowing you to fine-tune their coverage and spillover. Using a signal sniffer or a laptop, walk round the internal areas that need to be reached, checking that signal strengths are adequate. Then repeat outside, adjusting the configuration and position of base stations to make external reception difficult at best.
Repeat this when you replace or upgrade wireless access points. Potential intruders will be most attracted by the biggest signal on the block: make it harder for those in public areas to find your signal and you are much less likely to attract attention.
Controls
There are four aspects of wireless networking that you need to control if you are to have a reasonable chance of remaining unhacked:
- equipment vulnerabilities,
- publication of your network’s existence,
- individual access control,
- and protection of the content of network traffic.
All devices that form part of your network – particularly wireless access points or base stations – and all devices that will connect to it must be kept fully up to date with firmware and software security patches. Failure to do this could allow intrusion through a well-documented hack.
Unlike some server updates, you cannot afford to leave wireless security patches until you have tested them on a non-production system; once released they must be applied as soon as possible. A good example of this was the bug in Apple AirPort Extreme firmware that allowed unlimited incoming access over IPv6, a serious vulnerability until patched by the 5.1 update.
Although it may seem obvious, you do not want a private wireless network to advertise its existence and name to all and sundry. Check that SSID Broadcast is disabled, forcing new joiners to enter the name of the ‘closed’ network manually before they try to connect. Although this will not stop the determined intruder, like many car security devices it will slow them down, possibly sufficiently to encourage them to go and trouble someone else.
When choosing access control, ignore WEP completely. As it is so quick to hack, retailers who charge credit cards over wireless networks are forbidden from using WEP. As an absolute minimum, use WPA2 (which has superceded WPA), appropriately enhanced by limiting the systems that can connect, either using MAC controls or a full-blown wireless security server.
Not all WPA2 implementations are equal, though. Whilst WPA2 ‘home’ is not generally as resilient as WPA2 ‘enterprise’, the latter might still use relatively weak extensions such as LEAP and EAP-FAST, so you need an eye for detail when selecting options. Choosing WPA2 also assures you of a high standard for encryption of network traffic, the final aspect of wireless networking that you need to control.
If your network is of any size, say more than a dozen systems, or handles sensitive information, you really need to install a RADIUS server that is capable of IEEE 802.1X-2010 access control. Educational organisations that wish to support the eduroam international roaming service have to authenticate guests using the 802.1X standard; the 2010 specification addresses known vulnerabilities by encrypting data between logical ports using MACSec.
Construct unguessable passwords of at least 10 characters length, using digits and letters of both cases, for access to your wireless network and to alter the configuration of each access point. For a mere $17, anyone can use the WPA Cloud Cracker service to crack weak passwords within 20 minutes or less.
You will still need to check wireless access logs (don’t even consider buying an access point that does not support detailed logging), and periodically that users are not cheating your security by working illicit point-to-point connections or private access points, for example.
When no-one requires wireless access, out of working hours, cut back the transmit power or shut your wireless access points down altogether. Unfortunately, Apple’s AirPort Utility no longer appears to be scriptable, so you cannot script power changes at present.
If this sounds a little over the top, consider the consequences of the theft of all and any data transmitted over your wireless network – personal information that you are obliged to safeguard under the Data Protection Act, customer details that could be sold to a competitor or for identity theft, access keys that would compromise other databases and servers, and more. It may not attain the vast scale of those stolen in publicised attacks, but the consequences to your business could be just as devastating.
Tools: WEP, WPA, WPA2, and AirPort
WEP is a worthless deterrent against anyone intending to break into your network, WPA has been superceded, leaving WPA2 as the only serious option.
This come in ‘home’ and ‘enterprise’ variants: the former, also known as ‘personal’, requires a single passphrase that can be used from any connecting computer or device, the pre-shared key referred to as WPA2-PSK. This offers simplicity, accommodating visitors easily, but inevitably makes it much easier to penetrate. If you must use it away from a domestic setting, you should also impose timed access control according to the MAC address of the client. This will at least limit the periods available in which your network will be vulnerable to techniques such as MAC spoofing.
WPA2 Enterprise is much more sophisticated than simply limiting connections by the client’s MAC address, but requires access to a RADIUS authentication service, either through a local server or online. Recent systems should be compliant with IEEE 802.1X, the standard for port-based network access control.
All good modern access points, including AirPort base stations, should meet this requirement, thus be controlled from your RADIUS server. Macs have enjoyed support since Mac OS X 10.3, and iOS devices since iOS 2.0. However there have been improvements to the specification have been made to address vulnerabilities: look now for compliance with 802.1X-2010. The most significant changes in these are the use of MACSec or 802.1AE data encryption, and 802.1AR Secure Device Identity or DevID authenticated devices.
If those standards and acronyms are not sufficiently confusing, there are many more in the clutch of protocols that come with Enterprise wireless security, such as EAP, the Extensible Authentication Protocol on which 802.1X depends, and which is the basis for MACSec and DevID. Access points may wrap all these up in 802.11i compliance.
Tools: RADIUS and IEEE 802.1X Access Control
If you already run OS X Server, or have Windows server(s), the simplest way of implementing WPA2 Enterprise is to enable and configure the RADIUS servers provided as standard in those.
In the current version of OS X Server, the way to do this is to select the AirPort device used as the route in the Server app, and then enable Require user name and password login over Wi-Fi. This will start the RADIUS server and authorises all current users to gain access using the server’s default SSL certificate. However any further configuration has to be made manually, using the radiusconfig shell command in Terminal, as root (sudo).
There are times when you may prefer to make your access control server a different computer from your main servers; if your network relies on wireless to connect wired segments you should operate a separate RADIUS server within each wired network rather than relying on the wireless connection to a single server. A standalone RADIUS server may also be required where shared services are distributed peer-to-peer rather than concentrated in a server.
FOSS products include FreeRADIUS and OpenRADIUS. The commercial Radiator, costing €1500 upwards. These third-party servers will install on OS X client.
A newer and innovative option is the AuthenticateMyWiFi service. Provided that your network has a reliable Internet connection, this will deliver a RADIUS service with IEEE 802.1X/PEAP authentication on a volume subscription basis. This could be ideal for smaller networks that cannot run their own local RADIUS server, and networks that are distributed across several different sites.
Summary
- Few networks can operate the only completely robust security policy of not offering wireless connections at all.
- Unless properly secured, wireless networks are very easy to break into, allowing intruders access to your most sensitive data.
- Design, site, and configure wireless access points to minimise spillover into areas to which the public has access. If potential intruders cannot find a signal, they cannot hack into your network.
- Disable SSID Broadcast, so that network details are not broadcast to the public. This will also keep details out of databases compiled by Google, Skyhook, and others.
- Ignore WEP, using only WPA2 security on all access points.
- In businesses and organisations, if possible set up a RADIUS server and use WPA2 Enterprise to control access rigorously.
- If you cannot run a local RADIUS server, consider an online service, or at least limiting access by day, time, and MAC address.
- Ensure all wireless passwords are 10 characters or longer, with mixed digits and letters of both cases.
Updated from the original, which was first published in MacUser volume 26 issue 13, 2010.