Wherever you look in macOS security, the name Gatekeeper keeps appearing. According to Apple, it’s “a technology designed to help ensure that only trusted software runs on a user’s Mac.” This article goes in quest for this beast.
There’s no Gatekeeper app or tool
Search your Mac high and low, and you’ll not come across an app or other executable named Gatekeeper. Neither does it run as an identified process that you can follow in Activity Monitor. If you plough through your Mac’s logs, the closest you’ll come to seeing Gatekeeper mentioned there is the rare reference to “GK checks” being performed, and whether they’re successful.
Few apps seem to mention Gatekeeper either. My own SilentKnight and its sibling LockRattler do refer to Gatekeeper, but there only to data and databases that are long since disused. The names of those databases contain the letters gk to make that association, but that’s now just a blind alley, and all new Macs come with ancient versions of those databases which are never brought up to date. Gatekeeper has moved on since those days.
What Gatekeeper does
According to its description in Apple’s Platform Security Guide, when a user opens an app, plug-in or installer package that they have downloaded from outside the App Store, Gatekeeper:
- verifies the software has been signed by an identified developer, and notarised by Apple, and hasn’t been altered;
- asks the user to approve opening downloaded software the first time, even if it is notarised;
- opens apps from randomised, read-only locations “when necessary” to protect against the distribution of malicious plug-ins with benign apps.
As we have deeper understanding of those processes, we can list in more detail the individual components and processes involved.
Checking app signatures is normally directed by AMFI, Apple Mobile File Integrity, although signature checks are also requested for other purposes by other parts of macOS. When you try to run an app with a broken signature, and it’s deliberately crashed because of that, it’s normally AMFI that initiated the check.

Checking signatures thoroughly is a complex process that involves checking that the certificates haven’t been revoked, which in turn can require online checks with Apple’s OCSP service. It also involves verifying the cryptographic hash, which then matches against notarisation.
Once those are complete, the user is presented with one of two dialogs depending on whether the software or installer package has been notarised, as the second action listed above.
The third action, known as app translocation, is obvious in the log. Although my example log excerpt here is from Sierra, where XProtect called Gatekeeper checks explicitly, this shows the type of path you’ll see during app translocation.
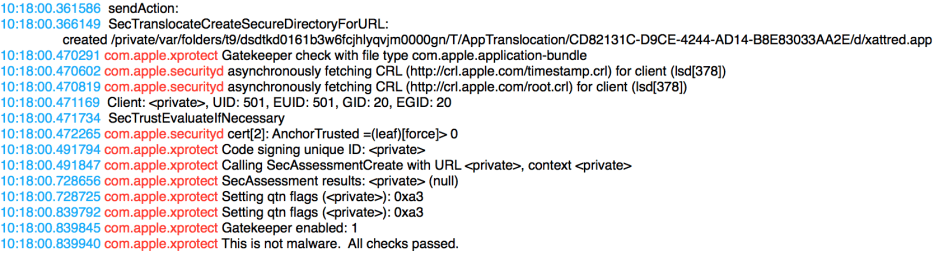
How fast and simple Gatekeeper checks were in those days!
Apple draws a clear distinction between Gatekeeper and XProtect in either of its forms (Yara signature-based malware detection performed on demand, and background scanning to detect evidence of malware infection and remediate it).
I hope that this explains how Gatekeeper is a set of features involving different subsystems and services in macOS, none of which is actually named Gatekeeper, but that the name is a simple and convenient way of describing their concerted actions.
