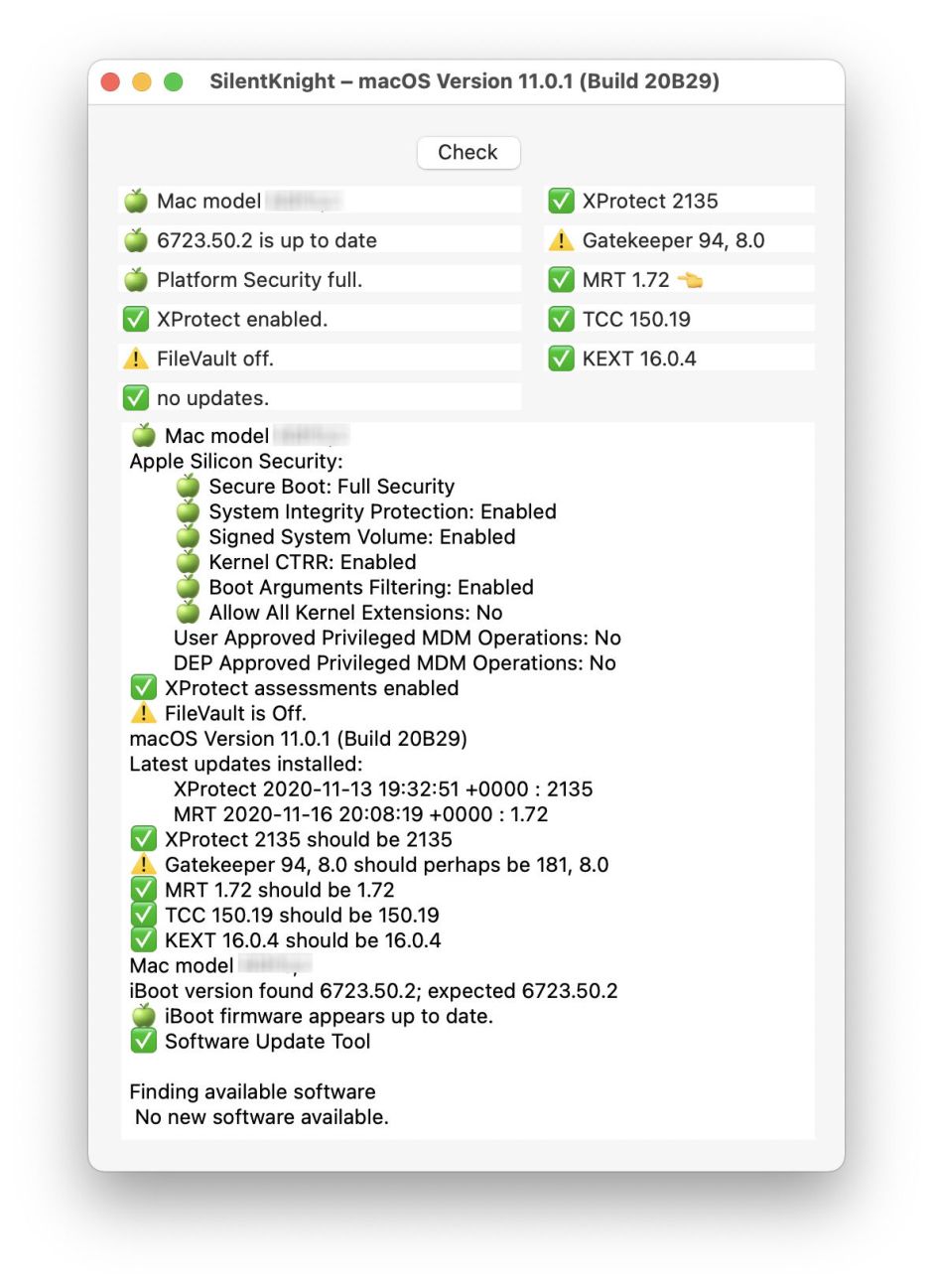
I’m delighted to release the next version of my free utility SilentKnight, which checks the firmware and security settings of your Mac. This new version is primarily aimed at the latest M1 models of Apple Silicon Mac, and makes them first class citizens. There are no significant changes for those using Intel Macs, though. One small change worth mentioning for those who have low version numbers for the Gatekeeper database in Big Sur, is that the warning is more considered:
⚠️ Gatekeeper 94, 8.0 should perhaps be 181, 8.0
rather than an error.
I have extended my GitHub database to include the iBoot firmware versions of Apple Silicon Macs, so this version should now check that your Apple Silicon Mac is fully up to date:
iBoot version found 6723.50.2; expected 6723.50.2
🍏 iBoot firmware appears up to date.
Apple Silicon Macs also come with a whole new suite of Platform Security features. Rather than clutter up the upper part of the display, when running on an Apple Silicon Mac, SilentKnight now performs a full survey of the following:
- Secure Boot
- System Integrity Protection
- Signed System Volume
- Kernel CTRR
- Boot Arguments Filtering
- Allow All Kernel Extensions
- User Approved Privileged MDM Operations
- DEP Approved Privileged MDM Operations.
These may not be available on all Silicon Macs.
Where it previously reported the status of SIP, it now gives an overall assessment. If any of those security features isn’t set normally, then SilentKnight warns you. It then gives an itemised listing in the lower text box so that you can decide whether that’s what you intended.
SilentKnight version 1.14 is available from here: silentknight114
from Downloads above, from its Product Page, and via its auto-update mechanism.
One final warning: if you force SilentKnight 1.14 to run using Rosetta 2, you’ll see some different results from those in ARM-native mode. This is because, when running in Intel mode, all its calls to use command tools are also run using Intel versions, which don’t return the same results. I don’t intend working around that bug.