On 29 April 1956, the diver Buster Crabb entered the water in Portsmouth Harbour on a covert mission for MI6 to examine the hull of a Soviet ship. What was presumed to be his body was discovered just over a year later. There’s still speculation as to how Crabb died, but it’s almost certain that he was using a closed-circuit oxygen rebreather diving set, well-known for their role in diving deaths. If his death was accidental, it occurred in a complex scenario which is best understood using slices of Swiss cheese.
Thirty years later, James Reason, professor of psychology at the University of Manchester, proposed a new model for accident causation based on slices of Swiss cheese with holes in them. Originally developed in his work investigating accidents in the nuclear industry, it has since been widely applied across aviation, healthcare, and engineering more generally. Although Wikipedia identifies is as “the principle behind layered security” and defence in depth, I suspect many security researchers and engineers are unaware of its applications and implications.
Reason’s model has inevitably become elaborate and developed its own terminology. As an alternative and adjunct to the concept of the accident chain, or chain of causation, its basic form adds value for those designing and trying to exploit layered computer security systems.
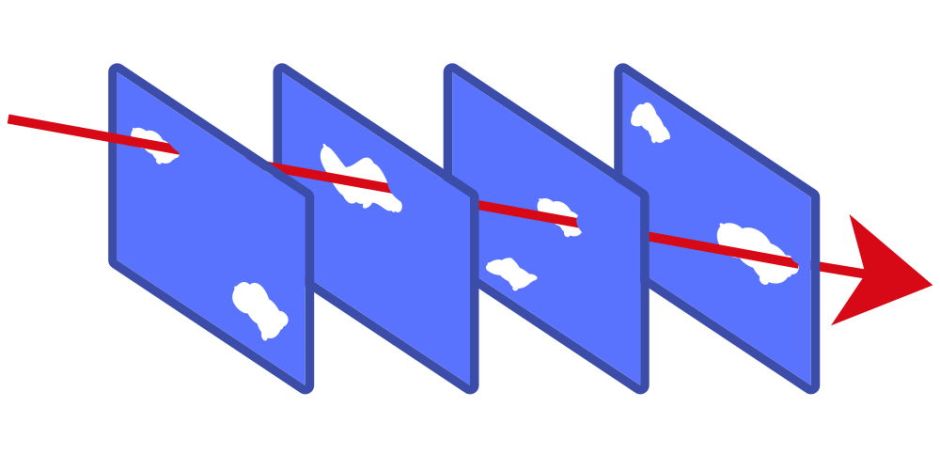
Interpreted in terms of computer security, the model consists of a series of layers through which an attacker must penetrate in order to exploit the system. None of the layers is perfect: as in real life, there can be no single absolutely effective security measure. Each therefore has vulnerabilities which could be exploited individually. However, successful exploitation of the complete system requires that those holes are all lined up to allow the attacker a linear trajectory through them simultaneously.
Successful defence in depth therefore requires design of security systems in which such linear trajectories can’t occur. That’s achieved by using individual measures (slices of cheese) which minimise the attack surface (fewest and smallest holes), and which can’t be chained together (alignment of holes in slices).
An example of this in macOS is the Gatekeeper system. In the first slice, files which are downloaded to a Mac from the Internet have a quarantine flag attached to them, provided that the process which fetches them adopts that behaviour. The second slice is that apps which decompress and unpack archives such as Zip files preserve the quarantine flag on the resulting files, including any apps. When one of those apps is launched, the third slice invokes Gatekeeper because the quarantine flag is set. The fourth slice is Gatekeeper calling on XProtect to check the quarantined app for a signature from those of malware known to it.
Each of those four slices has holes in it, of which the most obvious is the first: if the software used to download the archive in the first instance doesn’t attach a quarantine flag to the download, then the resulting trajectory passes cleanly through holes in the other three slices, and a malicious app can be run.
One measure which Apple has adopted in macOS Catalina is to greatly reduce the size of the hole in the last slice: when any app (or tool) is launched, XProtect invariably checks it against its signatures of known malware, regardless of the state of any quarantine flag. The hole hasn’t closed altogether, though, as that slice depends on the ability of XProtect to detect it as malicious. That makes it harder for any attacker to find a linear trajectory through the layered security system.
We must always be careful not to overapply any model, which can lead us to draw conclusions which aren’t founded on the behaviour of the real system we’re modelling. However, Reason’s Swiss cheese model explains how layered security can usefully incorporate measures which aren’t in themselves particularly effective. If it’s designed to block a linear trajectory, then a layer which is of itself only eighty or ninety percent effective can completely block many exploits. Analysing successful exploits in terms of Reason’s Swiss cheese model is also rewarding in that it should lead to preventative measures which reduce the size and alignment of the holes which are used, or the identification of an additional slice to block a successful trajectory.
Next time that you see a layer in macOS security which doesn’t in itself appear particularly effective, consider carefully how that slice fits into the overall design, and whether it might be there because it works well in combination. Think Swiss cheese.
