Many apps use helper tools. Indeed, some of Apple’s bundled apps like Disk Utility appear to be nothing more than GUI wrapped around an elaborate network of different helpers. They have an inherent advantage when they have to deal with Mojave’s new privacy protection, though, as Apple has private entitlements which can work around most of the issues arising. For third-party developers, the situation isn’t so easy.
I stumbled into this yesterday when attempting what should have been a simple task: making a clone of my MacBook Pro’s internal SSD using Mike Bombich’s excellent Carbon Copy Cloner (C3). Although I eventually got there, it is one illustration of how what used to be simple is now inevitably more complex.
Following my own checklist, I wanted to clone the High Sierra startup SSD in my MacBook Pro to an external SSD, so that I can upgrade that internal SSD to the release version of Mojave (its betas have been running from another external SSD). Knowing that it is better to clone between non-boot disks, I started up in Mojave beta and ran C3 from there. As this is Mojave, I ensured that I was running the latest C3 beta, version 5.1.5-b4 (5516).
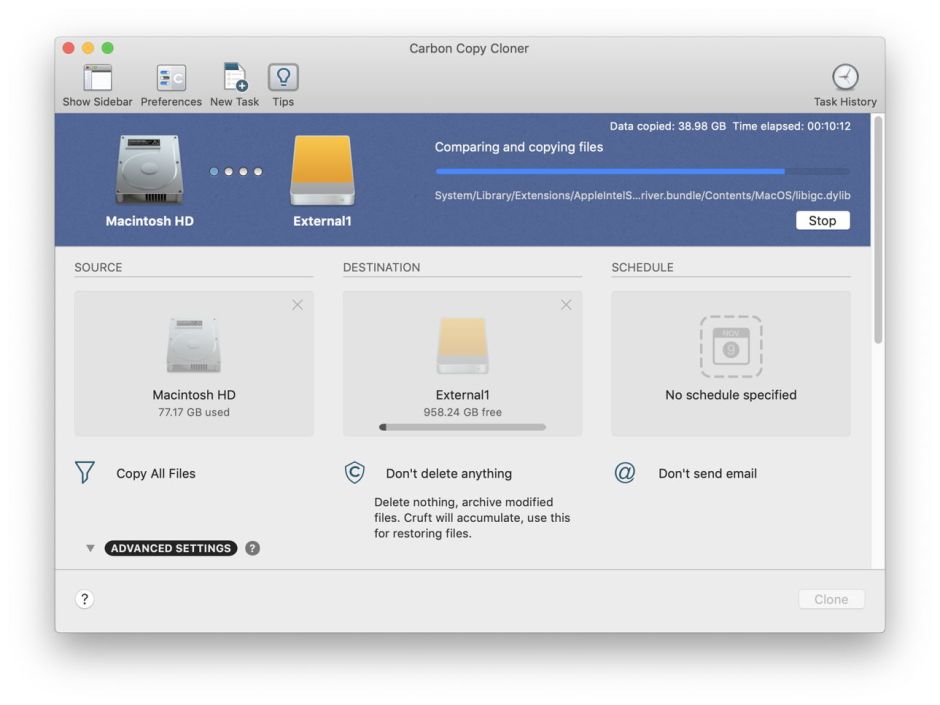
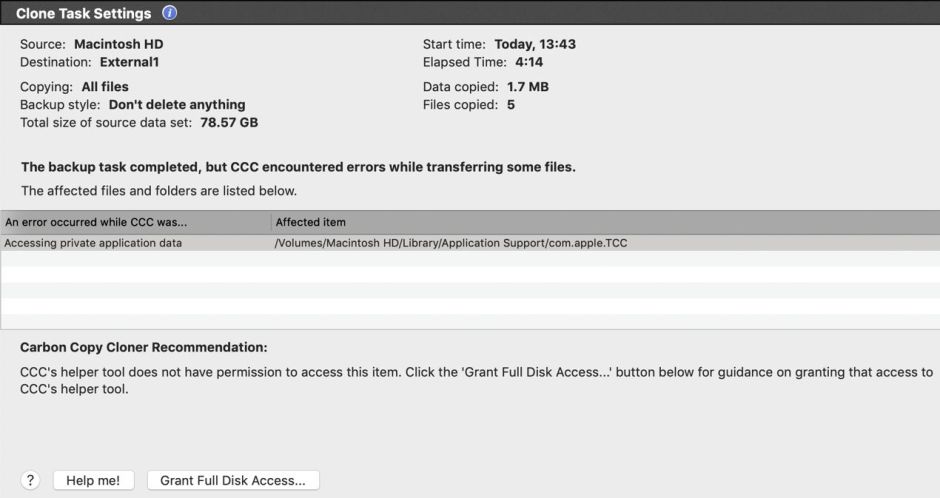
Right at the end of the cloning, C3 reported an error: Mojave’s privacy protection was stopping it from copying High Sierra’s privacy protection support in /Library/Applications Support/com.apple.TCC. This is a surprise, as it shows that Mojave’s TCC system extends its reach beyond your startup volume, something that I hadn’t understood from the WWDC presentations.
C3 is actually quite a complex app. It includes a helper tool (com.bombich.ccchelper), a login item (CCC User Agent.app), and three command tools (archive_manager, ccc, and a special version of rsync). What was happening was that TCC was blocking access to High Sierra’s /Library/Applications Support/com.apple.TCC not to the main C3 app, but to its helper tool, a Launch Agent named com.bombich.ccchelper. (These are now even more complex in the current version of C3.)
Mike Bombich is already well aware of this issue, and has added a neat set of instructions to steer users around it. Read them carefully, and do exactly as they say, as they will help you add the helper tool to your Privacy settings to give it Full Disk Access. If you try to do this yourself using the main C3 app instead, it won’t help in the slightest.
There’s another awkward issue here: when you add any running app to Full Disk Access, macOS helpfully points out that for this change to be effective, you have to quit the app. If you have mistakenly added the C3 app to Full Disk Access instead of the fish icon provided, the Privacy controls offer to quit C3 for you, which only sets you back.

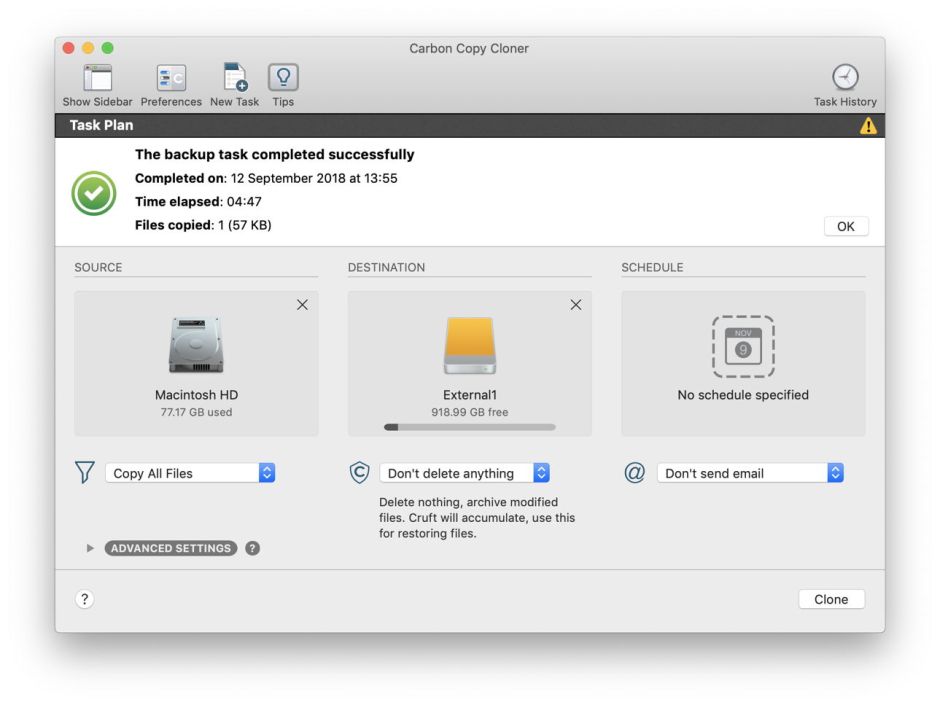
With com.bombich.ccchelper added to the Full Disk Access list, C3 can run the cloning in full, and I eventually ended up with a cloned SSD with a bootable copy of my internal SSD on it.
Important lessons for Mojave early adopters are:
- Mojave’s privacy protection extends to some folders beyond your Mojave startup disk; these aren’t currently documented, but include /Library/Applications Support/com.apple.TCC.
- When you think an app needs to be given Full Disk Access, it may actually be a helper tool which must be added to the Privacy settings, not the app itself. This appears to be a special case to the rule that command tools are traced through their Attribution Chain to the ‘parent’ app which called them in the first place: in this case, adding the C3 app to Full Disk Access doesn’t give its command tool helper com.bombich.ccchelper full disk access. This may be because it is run as a Launch Service, but none of this is documented.
- Third party apps which use helper tools, as C3 does, need to be provided with a mechanism similar to that in C3 to guide the user through the process of adding their helper tools to the Full Disk Access list, when required. As far as we know at present, that cannot be performed by the app, but requires the user to make that addition. Users can add command tools to the Full Disk Access list, but need to be helped to do so.
- This may provide an answer to the outstanding question of how you can give Full Disk Access to a command tool like a Launch Service which is run not by an app at the top of its Attribution Chain, but from within macOS: it has itself to be added to the Full Disk Access list, something the user may find seriously challenging.
Although I’m not sure why TCC should be concerned about me accessing the TCC system on a High Sierra boot drive, the other issues here are inevitable consequences of it providing effective privacy protection. If an app could circumvent protection by just using a helper tool, there would be no protection at all. But helper tools are normally buried inside the app’s bundle, making them awkward for ordinary users to access and to manually add to the Privacy list.
If someone in Apple had been describing these issues in detailed developer documentation, then we would all surely be better prepared.

