As I understand it – and correct me if I’m wrong, because this isn’t simple – there are four use cases with Mojave’s imminent privacy protection.
If the app has been built using the latest (10.14) SDK, and the user doesn’t add it to the Full Disk Access list in the Privacy pane, macOS (or TCC, to be precise) will check the app in the event that the user tries to access protected data with it. If that app includes appropriate usage information for that specific class of protected data, then the user will be invited to consent to the app accessing it. If they agree, then the app will be added to the class-specific list, and it will be able to open the file.
If built with the latest SDK, not given Full Disk Access by the user, and the app doesn’t contain appropriate usage information, then TCC will crash the app without offering the user any other option.
If built with the latest SDK and the user adds that app to the Full Disk Access list, then the app will be given access, normally after obtaining user consent.
Apps built with earlier versions of the SDK, such as 10.13, are given the benefit of the doubt, as they are not expected to follow these new rules over usage strings. In those cases, TCC shouldn’t crash the app, but should invite the user to give their consent. If that is given, then that app will be added to the class-specific list, and the app will be allowed to open the file.
From this, there are several important pieces of information which the user may need to decide what to do to pre-empt privacy problems:
- which version of the SDK was the app built against?
- does the app include a usage string for that class of protected data in its Info.plist?
- what entitlements has the app been granted in its signature?
These are accessible, by opening the app’s Info.plist and using the codesign command to determine its entitlements – actions which are beyond the reach of the average user, and tedious even for the expert.
So here is a simple app which does them for you: Taccy, its name derived from TCC, the Transparency Consent and Control system in macOS.
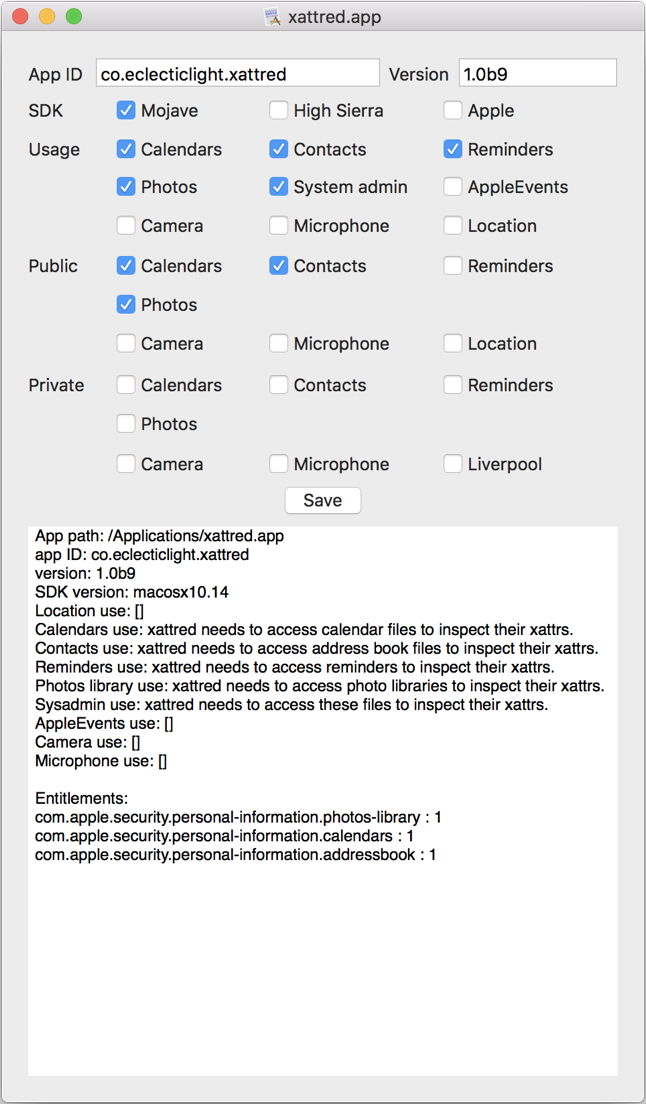
Drop an app like xattred onto it, and it tells you not only which version of the SDK it was built against (here 10.14), but whether that was Apple’s internal version, or that made available to third party developers.
It then flags which of the usage strings are included in its Info.plist file, with the strings themselves displayed in full in the scrolling window at the bottom.
Below those are the public entitlements which are included in its signature, here covering Calendars, Contacts, and Photos libraries; there currently isn’t a separate entitlement for Reminders as far as I can tell.
Then come the private entitlements, which are used extensively in Apple’s apps, and presumably give broader abilities than the public versions. Being signed with a regular developer signature, this app has none of those.
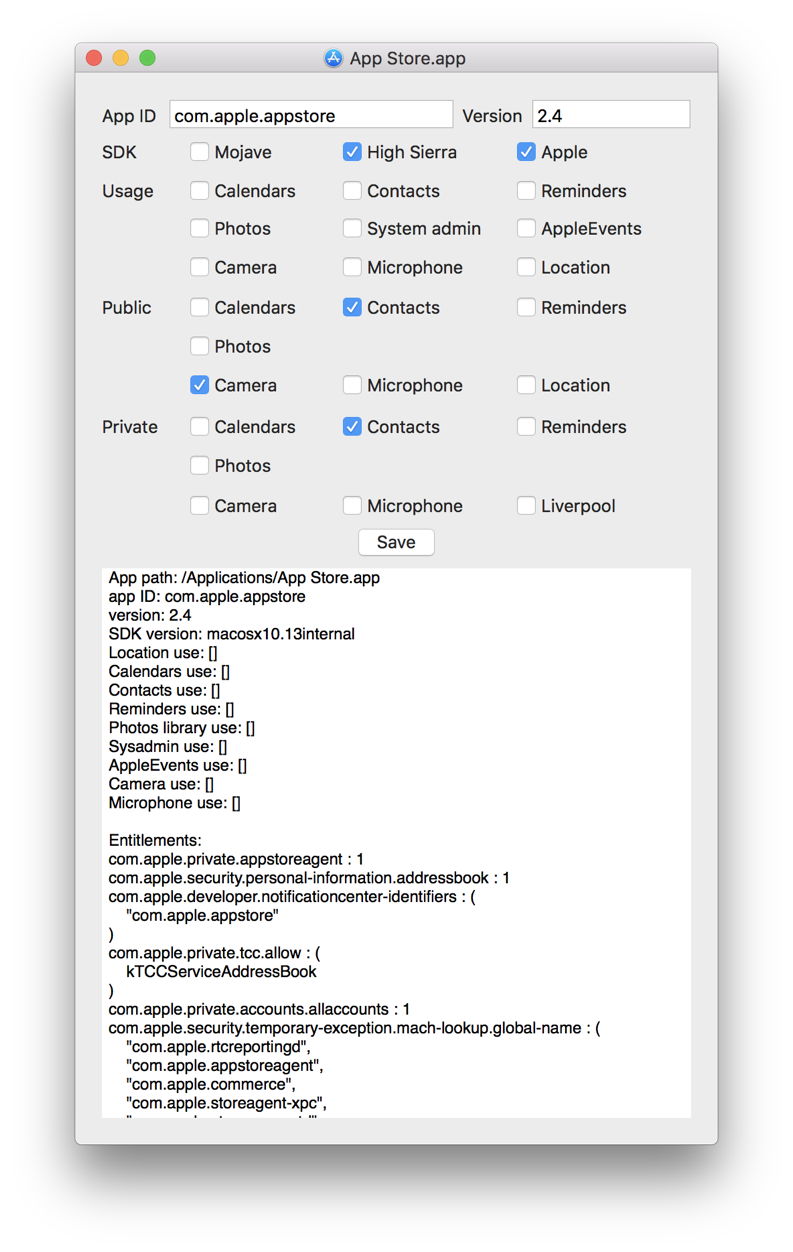
Here’s Apple’s App Store app in High Sierra. As is usual with apps built with Apple’s internal version of Xcode, it has no usage strings at all, and only entitlements. Included in the public entitlements is access to the Camera, which seems puzzling in this particular app. There is a lot of additional detail listed in the text below.
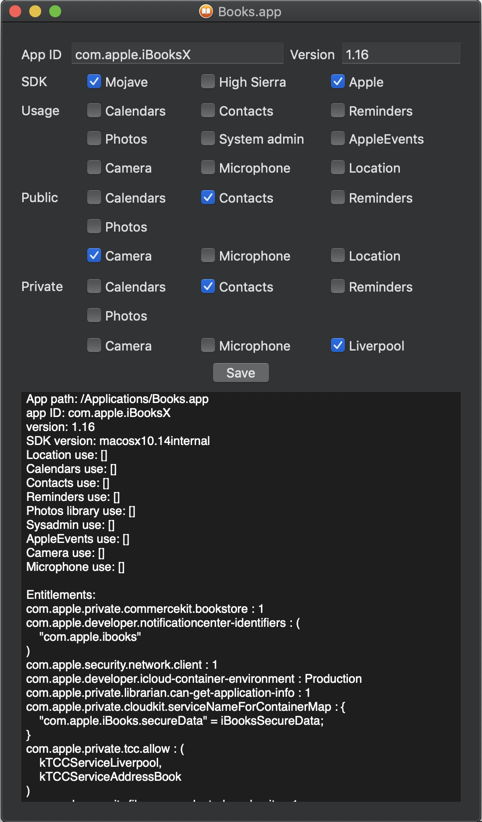
Apps built for Mojave tend to have more extensive privacy settings than those for Sierra, for instance. This is another app which strangely claims access to the Camera in its public entitlements, and its private entitlements include one known simply as “Liverpool”. If that makes any sense to you, I’d be very grateful if you could explain what it means!
This early beta of Taccy should be of value to anyone intending to upgrade to Mojave, as it will inform you of what your current apps will do when they are migrated. Apart from my own apps, I only seem to have one which has been built against the 10.14 SDK, and that won’t be accessing any protected data in Mojave.
If you’re developing apps with the 10.14 SDK, then Taccy gives you a chance to check their settings and entitlements, before users start complaining about problems.
Even in Sierra and High Sierra, Taccy reveals a few surprises. In Mojave, it is simply fascinating, and the other entitlements listed in the scrolling text view are an excellent lead in to understanding how Apple’s apps can do things that others can’t equal.
Taccy 1.0b3 for Sierra, High Sierra and Mojave is available from here: taccy10b3
and from Downloads above.
