Your Mac knows a lot about you: roughly where you are, your engagements and appointments, details of all your contacts, your Twitter and Facebook accounts, and more. Its privacy controls let you decide which of that information is shared, and with which apps and services.
Privacy overlaps in many areas with security. Apps which seek to access private information could pose a security risk to you if they leak any of that back to an online system, and malware can try to exploit loopholes in privacy to do that thoroughly maliciously. But protecting your privacy is largely a matter of personal choice: there are often benefits to you if you let an app have access to your address book, but you may decide that you’d prefer not to.
Early versions of OS X did not have particularly fine-grained controls over privacy. In those days we tended to be easily impressed – if an app did something clever with our address book, that seemed like a good thing, not something to get too worried about. By the time of OS X 10.8 Mountain Lion, it was clear that users needed to control access properly, and it was then that Apple introduced the mechanisms which are used still in macOS Sierra.
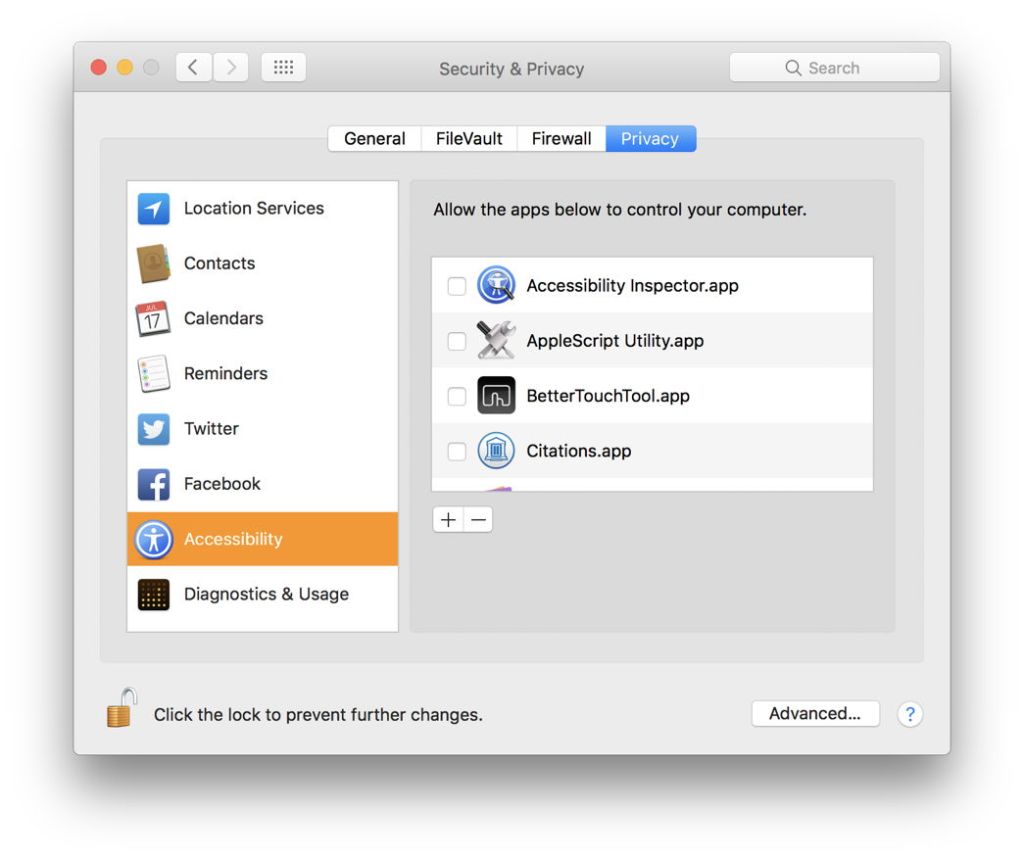
Your interface to these controls is in the Privacy tab of the Security & Privacy pane, in System Preferences. This divides privacy up into the eight main areas, covering Location Services, databases of Contacts, Calendars, and Reminders, the social media, Accessibility (which is not really what you might think), and diagnostic and usage data.
Normally, if an app wants access to data controlled by the privacy services in macOS, it will prompt you to agree to it obtaining such access. You can always pre-emptively give it access using the pane, or remove its access at a later date if you change your mind. It is good practice to check through the different categories here every so often, as it is easy to let your private data leak all over the place, and this gives you the chance to review your setup properly.
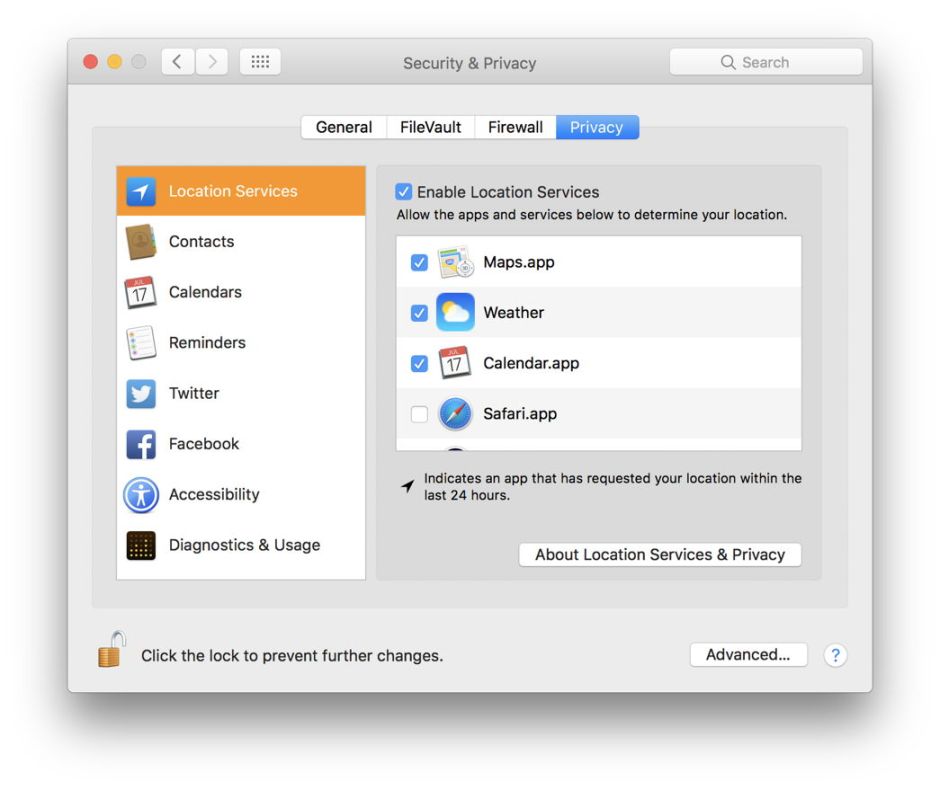
Location Services is probably the simplest. Your Mac works out as best it can where you are, for example using locational information from wireless networks to which you might connect. You can then choose which apps you allow access to that location. If yours is a desktop Mac or a largely static laptop, this may not be particularly useful or private. But you may prefer some apps not to know your location when you are travelling with your Mac.
Locational information is not a database but a service, so your Mac runs a background service or daemon named locationd which handle this. Its only interface to users is through the Privacy tab in the Security & Privacy pane. Location Services settings property lists and other data are stored in /private/var/db/locationd, which requires root privileges to access.

The Contacts, Calendars, and Reminders items determine which apps are allowed access to your address book, calendar, and reminders. These are fairly straightforward too, in most cases allowing you the convenience of being able to retrieve contact information automatically, if you’re prepared to trust them.
Internally, this is managed in a special TTC database, which is stored in the folder ~/Library/Application Support/com.apple.TCC. There is also a master database stored at /Library/Application Support/com.apple.TCC, but you cannot open that folder, as only the system has that privilege. The only command line tool which provides any access to this privacy database is tccutil, which only supports a single command, to reset the database. So
tccutil reset AddressBook
should reset all decisions made about access to your address book. Each controlled service is reset individually. The available services include:
- contacts, for access to your address book
- accessibility, for the services controlled in that category
- calendar, for access to your calendar
- reminders, for access to your reminders
- location, for access to Location Services
- icloud, for access to iCloud storage and settings.
Twitter and Facebook, the social media, should be self-explanatory. They determine which apps have access to your user accounts there.
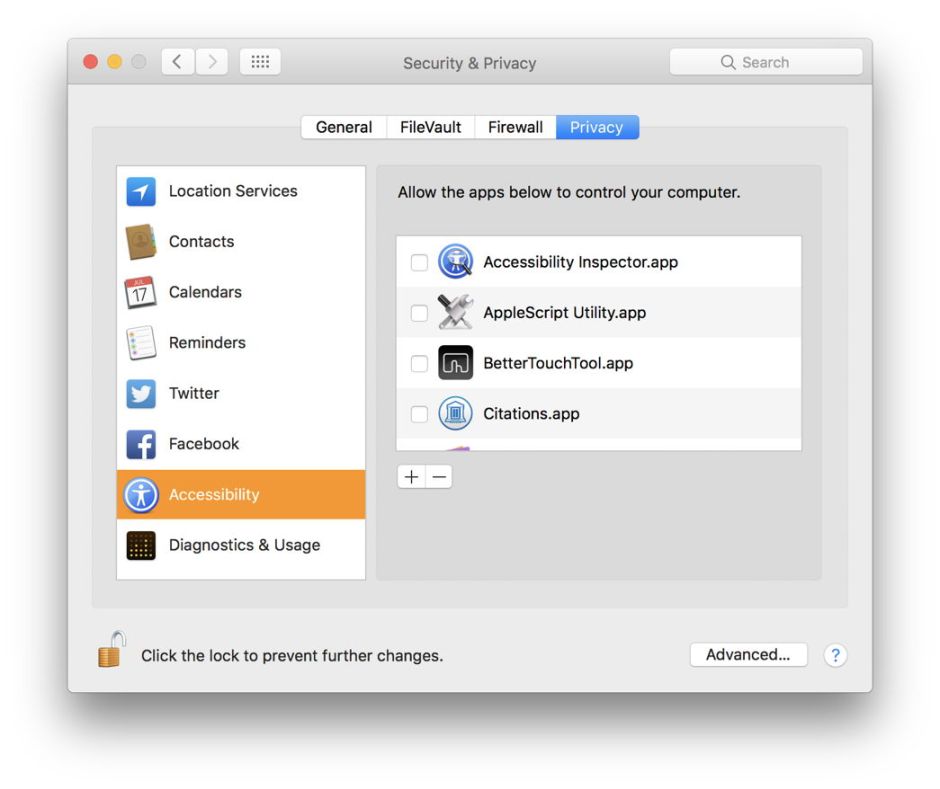
Accessibility has proved much more controversial, largely as the result of the Dropbox app. Earlier versions of that did not go through this pane, but worked directly with the TCC database, in order to obtain the abilities that the app’s features required. This has now been corrected, and recent versions prompt you to agree to the app being given access in the official manner.
Apple uses doom-laded words here, referring to apps being able “to control your computer” because this category covers a very wide range of abilities. Before agreeing to give an app such abilities, you should refer to its documentation, which should explain exactly what the app would do, if you were to agree. If they don’t, check their support Q&A, and if you remain in doubt, don’t let the app have access.

The final category concerns sharing of diagnostic and usage reports with Apple (alone), and of crash data with Apple and all app developers. In general, you should try to agree to both, as they help improve macOS and its apps. However if you are concerned that this might leak sensitive data which you are not happy with, it is your choice.

Another key area in terms of privacy is your control over what is stored locally, and what goes into iCloud, something referred to as Ubiquity, because once it’s in the cloud, you can access it from anywhere. Access to iCloud is controlled now in its own pane, where you can determine exactly what is, and what is not, shared with your iCloud storage.
One problem with all these privacy settings is that many of Apple’s built-in apps are given access over which you have no control. For example, the recent spate of ‘spamvitations’, spam emails which automatically become inserted as events in calendars, exploited the fact that the Mail app has automatic access to your calendar. If you used a third-party email client, such messages would only be given access to your calendar if allowed to do so in the Privacy tab of Security & Privacy. If you had enabled that, and started to receive spamvitations, then you could simply remove that access. Apple’s Mail does provide a separate control buried in its own preferences, but is not listed in the Privacy tab’s categories.