Earlier this year, it was discovered that a common mechanism used to update apps was vulnerable to attack. This depended on their built-in update feature, using Sparkle Update, employing insecure plain HTTP connections to download their updates.
There’s a limited number of ways that updates can be delivered. Those provided by the App Store are, of course, downloaded securely within the App Store app; although this does not guarantee that they are free from malware (as users of some Chinese apps discovered with XcodeGhost), it places the responsibility on Apple to keep the store and its products clear.
When updates are delivered outside of the App Store or equivalent systems for Adobe CC, for example, some vendors simply provide you with a link to their secure website, which then uses HTTPS to deliver the update securely. Here, you rely on connecting to the right website, and HTTPS to ensure that no one has tampered with the update. No commercial vendor of software should now be providing such updates over plain HTTP.
Many apps provided outside of store systems like to make updating even simpler, with a built-in feature to check for updates, download and install them from within the app – and that is most commonly provided using Sparkle Update, an open source project which developers are welcome to use. The snag with it was that it did not require the download to be provided using HTTPS, and sure enough, it was discovered that a lot of apps which used Sparkle’s features did not require download by secure means.
That was over six months ago. In the period since, all developers who use Sparkle Update should have updated their apps to require secure connections.
When I first wrote about this, it was not easy to determine whether an app which used Sparkle was doing so securely: basically you had to sniff its network packets to see. Thankfully this has now changed, and it is much easier for us to check whether an app has been properly updated to be secure.
One method is to check whether the app includes a Sparkle framework which is version 1.13.1 or later. To do that, select the app in the Finder, and use its contextual menu to Show Package Contents. Then navigate down to Contents/Frameworks, and select the Sparkle.framework item. Get Info for that, and it should report that it is version 1.13.1 or later, preferably 1.14.0 or the latest 1.15.0.
There is a slight catch here, in that the Sparkle project has provided some patches to older versions of Sparkle so that they can still be used, when developers cannot use a more recent version of the framework. These should be exceptions, and extremely rare now.
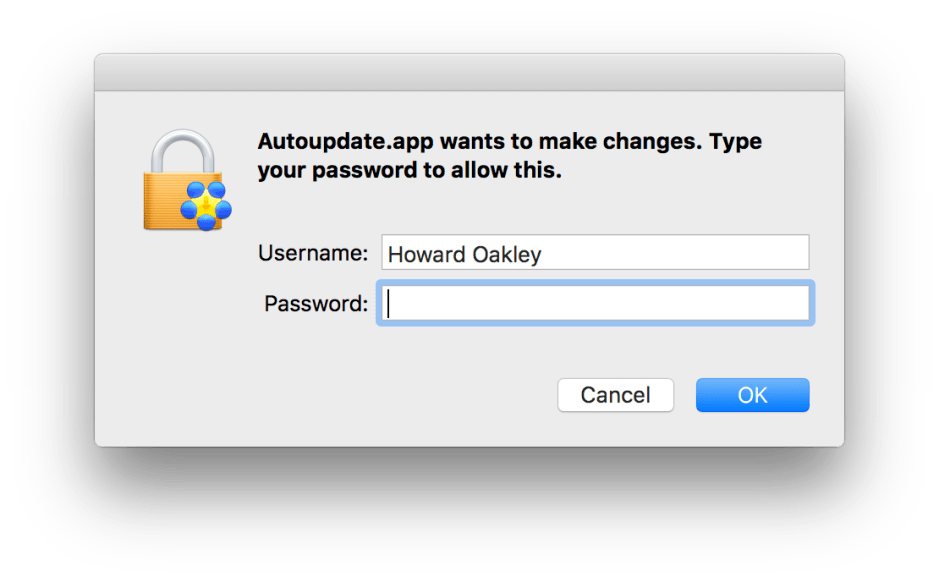
When you do run an update using the built-in Sparkle updater, you should now see a new ‘secure’ version of the dialog which prompts you to authenticate to install the new version of the app which it has just downloaded for you.
When you are checking through your apps in preparation for upgrading to macOS Sierra, you should pay particular attention to all those which have not been updated this year. If they use Sparkle, they may do so without the security of HTTPS, leaving you vulnerable.
