Over a month ago, I suggested how Apple’s strong stand over the protection of its users’ privacy might be broken apart by the Investigatory Powers Bill currently being rushed through the UK’s Parliament.
In a nutshell, this enables the UK Secretary of State to serve notice on Apple (or almost anyone else) to make whatever technical changes they deem helpful to law enforcement and security agencies, such as crippling encryption or putting a backdoor into it – a ‘technical capability notice’.
This can be performed entirely in secret, with penalties should anyone reveal the existence of the notice or what is performed in compliance with it, and without any judicial or technical moderation or supervision. As I wrote previously:
It is not about fighting crime or terrorism; it is a pernicious tool for mass and individual surveillance which would, in time, destroy the very fabric of trust on which the Internet depends.
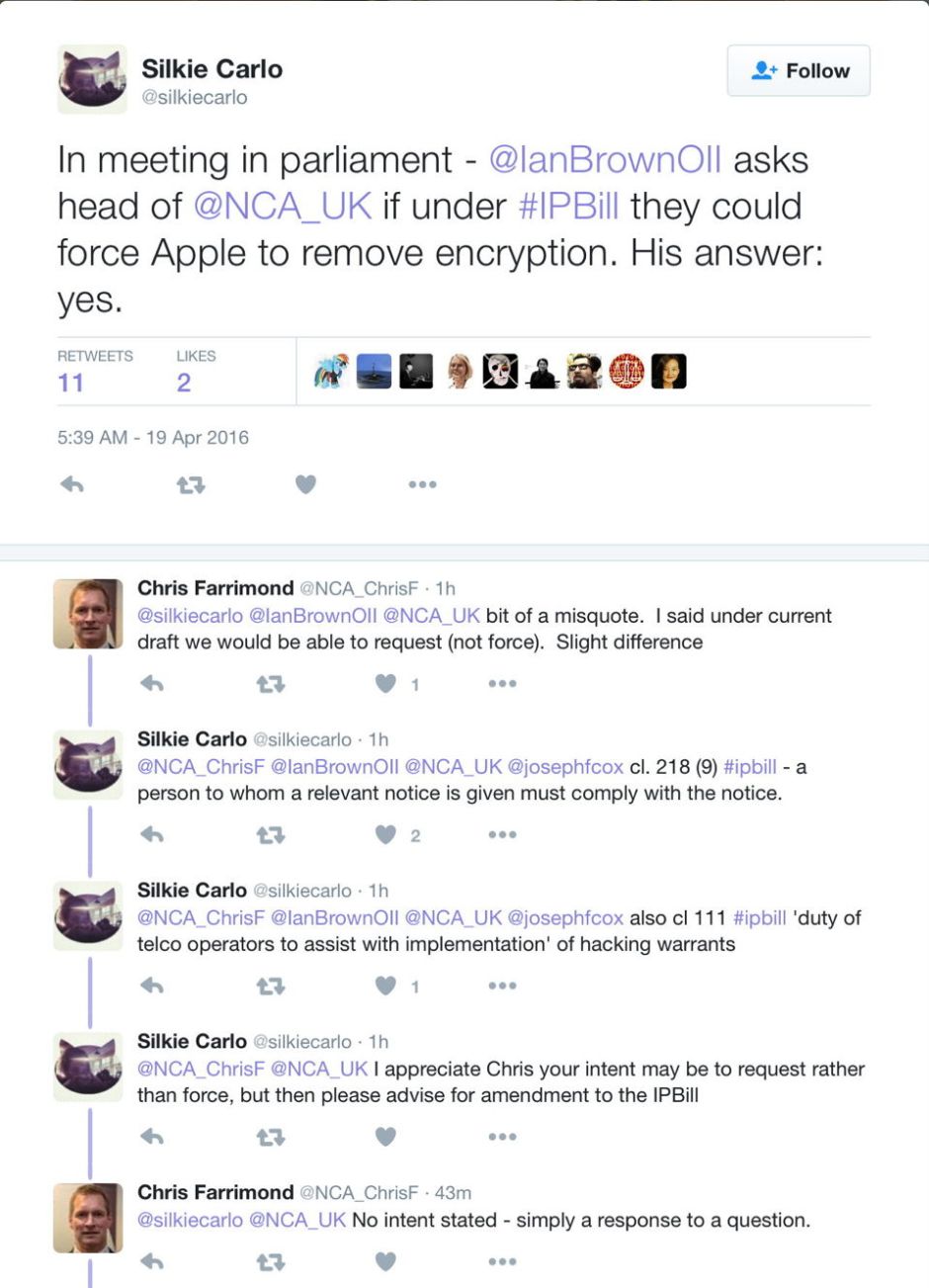
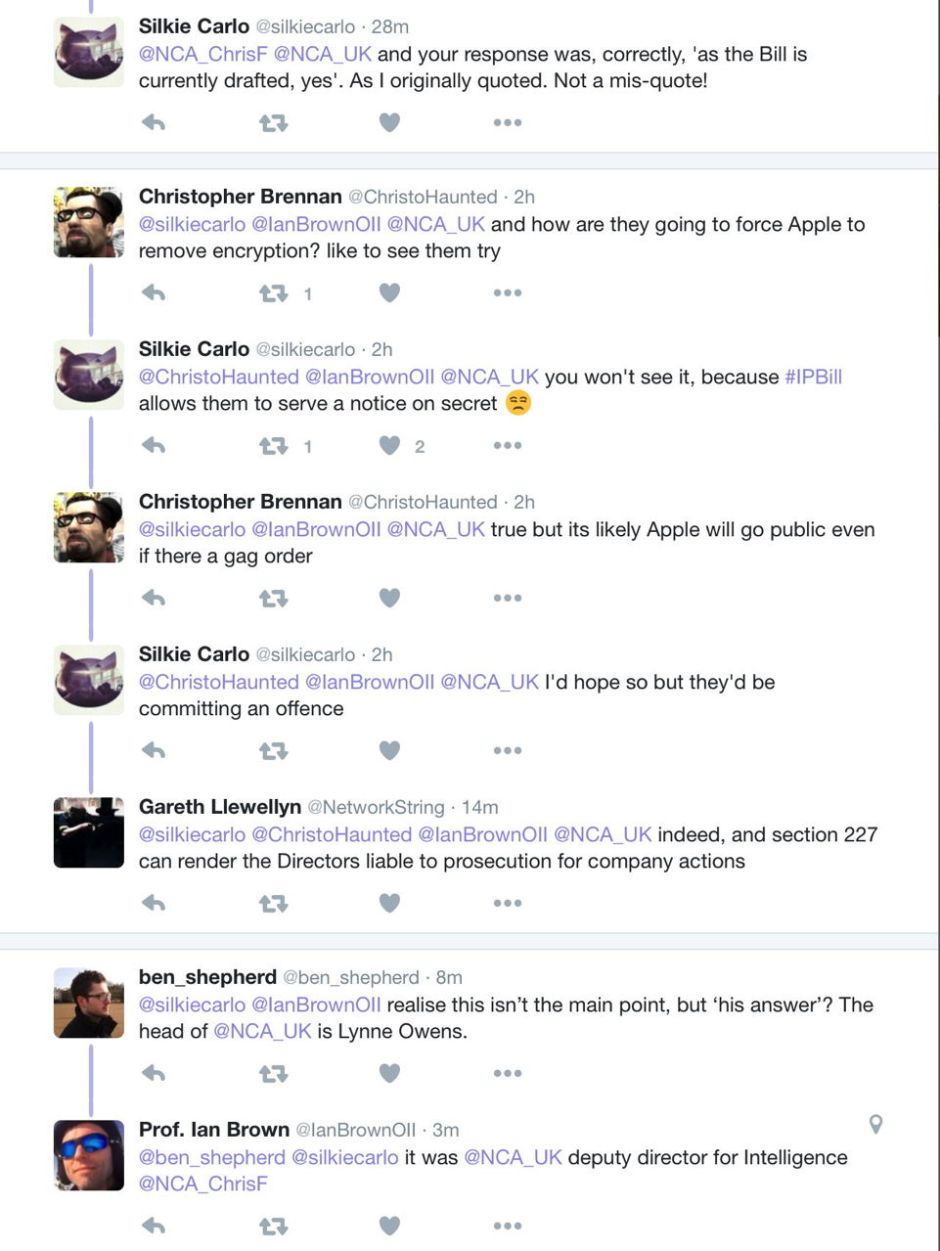
Already, before said bill has cleared parliament and become law, the UK’s National Crime Agency (NCA) has revealed that it intends to use the new law to strip effective encryption. The following series of tweets makes that clear, although at this stage the NCA has not revealed its intended technique of the technical capability notice. I cannot believe that it has not noticed the almost limitless, completely unsupervised, and totally secret powers of those notices, nor that it will not use them.
Contrast the NCA’s partial candour with the FBI’s persistent machinations. It seems to have finally revealed that it now has an independent means of breaking into older iPhones which do not have the Secure Enclave introduced in the iPhone 5s and iPad Air, as explained here last November. So it still wants Apple to open up all the more recent models involved in serious crime investigations. To that end, Apple is no doubt going to face further series of legal challenges, until either party gives in, or both get bored and find something else to occupy the courts.
What the US and UK governments have apparently completely forgotten in all this is their own utter dependence on the services – including encryption – provided by the six major vendors who have already articulated their stand against the UK’s Investigatory Powers Bill. Between them, Apple, Facebook, Google, Microsoft, Twitter, and Yahoo could pretty well shut down government services: a unique bargaining position.
Those agencies have also failed to notice that they can only lose. If the stand of the six major vendors wins, the agencies lose. If that stand is broken in either the US or the UK, then everyone loses because it will start the inexorable process by which strong encryption is lost for everyone, as all the best cryptologists and security experts have predicted.
Unfortunately, with the US Presidential Election and the UK’s forthcoming ballot on its future in the EU, too many minds are on other things. My money is still on Apple and its allies winning the day, but the next few months will prove very interesting times.
