What is MouseJack?
It is a new family of vulnerabilities which was discovered late last year by researchers at Bastille, who have just made it public. Affecting many wireless devices which do not use Bluetooth or WiFi communications, it makes it very easy for an attacker to take over the device.
Does it affect Macs or iOS devices?
MouseJack does not affect computers or similar devices as such: it affects wireless peripherals which may be connected to them. If you have a vulnerable device, then it affects all systems to which you might connect that device.
It does not appear to affect any Apple product as such: all Apple’s wireless devices, including mice, keyboards, trackpads, remotes, and other controllers, have used reputable protocols such as Bluetooth and infra-red.
How can I tell whether my wireless peripheral is vulnerable?
One tell-tale is that it requires a small ‘dongle’ to connect it to your Mac, almost certainly connected to a USB port. Reputable wireless support systems such as Bluetooth have been built into Macs for the last decade, and therefore any Bluetooth device should connect directly to that.

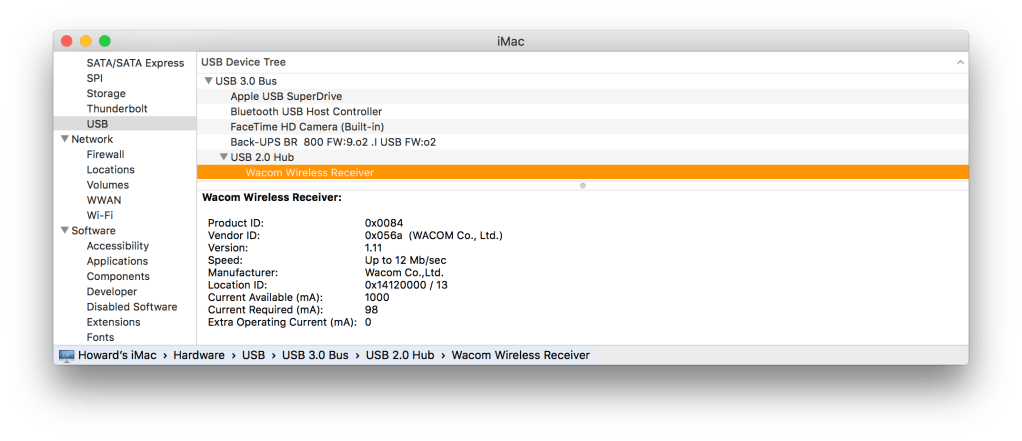
You may then get clues from inspecting the USB ‘dongle’ in System Information: select USB in the Hardware section and you should get further information about devices which are connected to USB ports. The vendor of the vulnerable chips is Nordic Semiconductor, who have sold billions of them for this purpose, and the specific product series identified as being vulnerable is the nRF24L.
Bastille has provided a list of products which they believe to be affected, but because the chips have been so widely used, they are likely to be in many more. For example, wireless graphics tablets are quite popular, and some are likely to use the same chips with the MouseJack vulnerability.
What can I do if my peripheral is vulnerable?
This is a real problem, as the systems which are vulnerable to MouseJack are very simple, and therefore most of them cannot be fixed by applying a firmware update (some Logitech and Lenovo devices are an exception, and can be updated). So you either carry on using them, knowing that they are vulnerable, or replace them with products which are not affected.
This is something which you should perhaps discuss with the product vendor’s support desk.
Is this really exploitable, or just another groundless panic?
As with all security issues, it is a matter of risk. If you use a vulnerable device half way up Everest, or in the middle of the Antarctic, you need not worry about MouseJack. Most use of vulnerable devices in homes and small offices should be fairly safe. But you can imagine that a large open-plan office which processes sensitive personal data using vulnerable devices is likely to have to take MouseJack very seriously.
Another scenario which you might like to consider is using a vulnerable wireless input device when sat in a public place, like a café. It would then be quite feasible for someone nearby to intercept your connection, and possibly take control of the peripheral. If you are going to continue to use a vulnerable device, you should only do so where you can be reasonably confident that it cannot be attacked.
Does it affect ‘smart’ home (IoT) devices or systems?
Probably. The vulnerable chips are popular with manufacturers because they use less power than full Bluetooth, and are considerably cheaper. This makes it highly likely that they will be used in IoT systems and appliances. Given the huge range of such products, it is going to be very hard to discover exactly which are vulnerable, and which are not. The same basic rule applies: if the device(s) use standard Bluetooth or WiFi wireless communications, they should not be vulnerable.
Where can I find out more?
On Bastille’s page, and maybe on product support pages of those vendors good enough to admit to the vulnerability.
What are the lessons?
Major protocols such as Bluetooth and WiFi are not immune to security issues, but should communicate in a way that is reasonably robust to passing attack. In particular, modern wireless devices should use secure methods of connecting, and data transferred should be encrypted where appropriate.
Using any device which uses its own, or other weak, wireless communications is asking for trouble. It is extremely easy for someone with a computer and a very cheap software-defined radio (SDR) dongle to break into these weakly protected (or unprotected) wireless connections. When properly implemented and used, Bluetooth and WiFi should be far more secure.
Many IoT devices, particularly security items such as doorlocks, are very low power, and may well use unencrypted and insecure wireless communications to save cost and power. Indeed some wireless connection protocols widely used for IoT purposes do not require any form of secure connection process, or encrypted communications. MouseJack should be a good reminder that using such protocols is inviting problems.
More generally, this begs the question of the fitness for purpose of billions of wireless devices. As there are no laws which require wireless devices to communicate securely, until someone challenges such products in court – probably in the US – manufacturers seem quite happy to take our money in return for products which they know can be hacked into easily. No one seems interested in doing anything to change that, or to make vendors responsible for ensuring a reasonable level of security in their products. The law appears designed to protect the manufacturer, and to hell with the consumer.