For most, our firewall is the most robust protection between us and the Internet. But it is not just a case of set and forget.
Network connection
A network router performs a simple task: it receives incoming packets from one network connection, and routes them to another connection according to the destination address and its configuration.
When coupled with an ADSL, cable, 3G/4G or satellite modem, the combination receives packets from the Internet that are addressed to systems on the local network, routing them onto that network, and reverses that process for outgoing packets to the Internet.
In the absence of a firewall, a potential intruder could identify your modem-router as opening into a local network, and try to send packets to connect to or otherwise disrupt any system on your network. Even when every device on your local network has its own firewall, the malevolent could bombard your network in an attempt to overwhelm it, in a denial of service (DoS) attack.
Firewall function
A firewall filters network packets, within the modem-router, in a standalone firewall appliance, or in your Mac, according to a set of rules.
For example, a standard default rule blocks all incoming packets originating from the Internet unless they are responses to previously sent outgoing packets.
Thus the firewall will let a remote website send you the contents of a web page when you have already opened a connection with the remote web server. But it will not allow a passing intruder to try to connect to your Mac’s file sharing, as your Mac did not open that connection with the intruder’s system.
Port-based filters
Packets being transmitted to, from and within the Internet are addressed to destination IP addresses, where they are intended for a specific network port.
Ports are a means of separating traffic into different streams according to its purpose: for example the standard port for connecting to a webserver is 80, whilst that used by most SMTP mail servers is 25. You can find a list of well known ports used by OS X here.
Rules used by firewalls to filter packets specify the port as a way of determining which services are permitted: for example, if you were running a server connected to the Internet, you would need to open its incoming port 25 if you wanted to allow users to connect to it to send mail using its SMTP mail server.
As there are over 64,000 different ports, potential intruders can scan some or all of them to see if any are open, so that they could try to connect through that port. Port scanning, which is also used to test a firewall for vulnerabilities, is always assumed to be a hostile act; by all means try scanning your own firewall, but never try this on someone else’s system.
On most local networks, devices have local IP addresses such as 192.168.1.1, but the whole network will have only one or a few public IP addresses, by which it is seen on the Internet. Routers normally convert between internal and public IP addresses automatically, and if your network has two or more public IP addresses, they may use them in an unpredictable way. When one local device needs to be known by a dedicated public IP address, you can enable this mapping by turning on network address translation (NAT) in the router.
Increasing sophistication
The earliest and simplest firewalls are crude filters, capable of simply blocking all incoming or outgoing traffic on specific ports. More sophistication is offered by later designs that incorporate ‘stateful packet inspection’. This keeps track of the state of connections on each port with each local device, and can detect more subtle attacks, thus providing significantly greater protection. Stateful or ‘deep’ inspection is now the standard in most firewalls.
Stateful packet inspection does not attempt to track which applications are responsible for traffic arriving at the firewall: that is the distinguishing feature of the most recent generation, the application firewall.
Instead of filtering packets by port, traffic is now controlled according to the application that handles it. You could for instance allow a gaming app to make connections over a specific port, but block your browser from using the same port. This provides a much greater level of control which can readily match the expectations of users.
It can be used to prevent children from using apps that could expose them to risk, and employers can deploy it to lock down a network to reduce the risk of inappropriate use or inadvertent acquisition of malware. You might also use it to prevent file sharing, if you are concerned that such activities could bring problems.
Most firewalls are either run on the computer which they are protecting, or at the single common pathway connecting a local network with the Internet, classically in the modem-router, to protect all local systems. However servers that provide services to both the local network and remote users via the Internet have more complex and demanding requirements for protection, and are known as operating in a ‘demilitarized zone’ (DMZ), relying largely on their own firewall.
Opening the firewall
It is not uncommon to want to allow remote access to local networked facilities, such as file sharing access to a home system, or a server inside the firewall. If you open a normal incoming port to let anyone both see the opening and try to exploit it, you will eventually get hacked. If you really do need to do this, the best way is to create a virtual private network (VPN).
Under that, the remote system authenticates with the network router or firewall to open a tunnel between the remote system and the local network. This authentication is particularly stringent to prevent an intruder from spoofing their way through, and all communications are strongly encrypted for protection.
Once connected through the tunnel, the remote system acts as if it is another device on the local network, with its own local IP address. When properly implemented, VPN is both powerful and safe, but you cannot afford to bodge it or it may prove vulnerable to attack.
Proxy servers
The ultimate development of the firewall is a proxy server, most commonly used to protect against malevolent or forbidden websites. In this, all attempts made by browsers on local systems are diverted to a local server, which checks whether connection to that remote site is permissible. If it is, the server then fetches the pages being browsed, checks that they do not contain banned content, and delivers sanitised content to the client browser. Configuring and running a proxy server is not trivial.
Keeping record
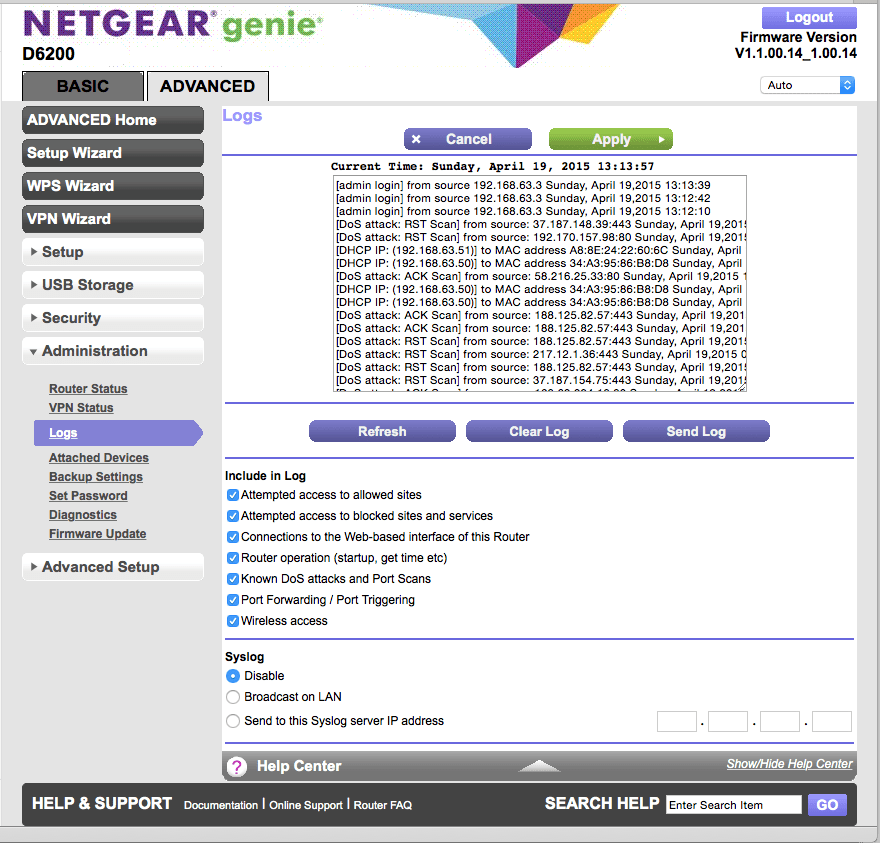
Each of the systems and services detailed, from the basic firewall bundled in most modem-routers right up to VPN facilities and proxy servers, keeps its own usage, error, and security logs, and requires configuration and administration. Default settings are often not fully protective, and you should ensure that your firewalls and other security systems are correctly configured, and their logs are checked regularly.
The great majority of small networks are left with their firewalls stuck in the manufacturer’s defaults, and logging is either not enabled (often the default setting) or never reviewed. Thus the first sign of any intrusion is the damage wreaked by the intruder, by which time they could have made off with sensitive personal or business information, and crippled your Mac.
Network intrusion detection systems (NIDS) are available, but seldom suitable for smaller networks.
Tool: The Modem-Router Firewall
Even basic modem-routers come with their own bundled firewall; for most users this is the only firewall that they need, and the most effective, as it acts as a gatekeeper to their local network. If you are prepared to pay a bit more for a mid-range modem-router, the chances are that it will come with quite a sophisticated firewall, including not only stateful packet inspection, but application firewall features too.
Refer to your modem-router’s documentation to discover how to configure its firewall. In almost all cases, you need to point your browser at the modem-router’s local IP address, such as 192.168.1.1, and enter the default user name and password. It is wise to change its access controls to a more robust name and password, and ensure that it cannot be administered remotely. Then open its basic firewall configuration and check that the firewall and logging are both enabled. Even quite expensive devices may ship with logging turned off.

Basic firewalls should normally be set to block all incoming packets, from the WAN or Internet to the LAN or local network, and this is almost always the default. Firewalls that incorporate VPN will need both ends of the connection to use a compatible protocol such as IPSec or SSL, and should be implemented in the outermost firewall at each end.
Application firewalls give much finer control over filtering, but need to be set up with correspondingly greater care and attention to detail. Generally they are best used in combination with ‘block all incoming’ in the basic firewall, where you want to control outgoing connections as well. However they can also be used to select which services will be exposed to the Internet by a server operating in the DMZ. If you can, test firewall effectiveness from outside your network.
Tool: Mac Firewalls
Prior to OS X 10.7, the standard bundled software firewall provided by Apple was FreeBSD’s IPfirewall, or IPFW. This is a widely-used and respected service which has excellent stateful packet inspection. In its raw form, it is controlled by the Firewall tab in the Sharing pane, and using Unix-style configuration tables if you want additional control.
As editing those tables is tedious and opaque, those who wish better control should use a third-party utility such as WaterRoof, donationware from Hany El Imam here. This gives almost complete access to the power of IPFW without the pain of editing its filter tables.
Lion, Mountain Lion, and Yosemite have switched to another stateful packet filter first seen in OpenBSD, Packet Filter, or PF. Control has moved to the Firewall tab of the Security & Privacy pane, although the Parental Controls pane offers certain features that equate to those offered in application firewalls, for controlled accounts.
PF has blacklist support, in which known malevolent sites can be blocked by IP address, which is required by new internal OS X security mechanisms, but as with its other features would normally be configured by a complex Unix text file.
WaterRoof’s author now offers IceFloor, donationware from here, which opens its features up to a far more friendly interface. For example, this allows you to maintain your own list of blocked hosts, and to use the free Emerging Threats database as a blacklist.
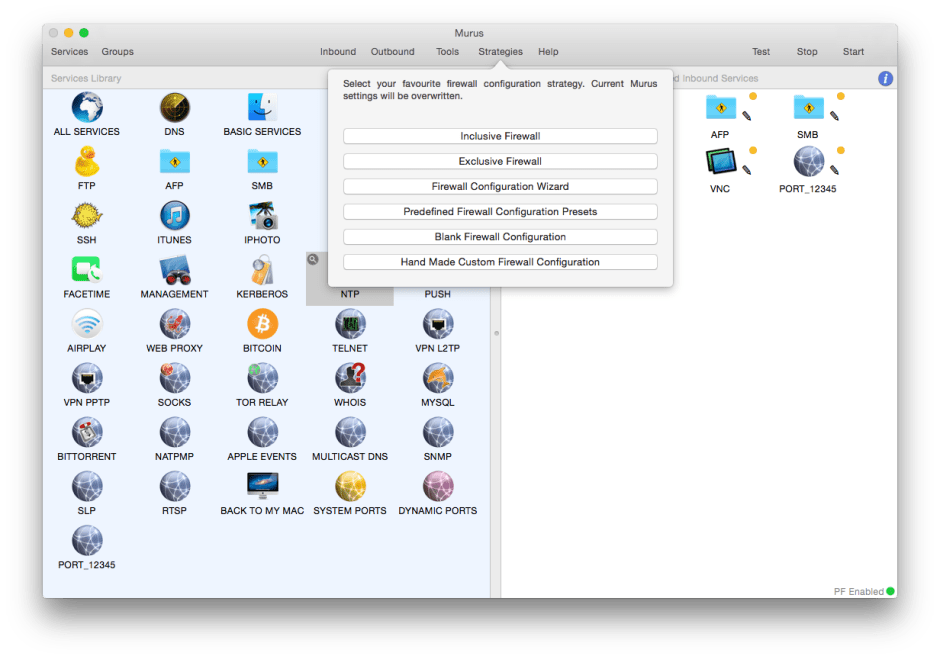
The latest tool for controlling your software firewall is Murus, available in free Lite or £29.46 Pro versions from here. The Pro version is the very best interface to PF that I have seen, making its huge capabilities available to every user, and I cannot recommend it strongly enough. The Murus home page is also the source of its excellent downloadable manual documenting the PF firewall in OS X, an invaluable reference if you prefer to go it alone instead.
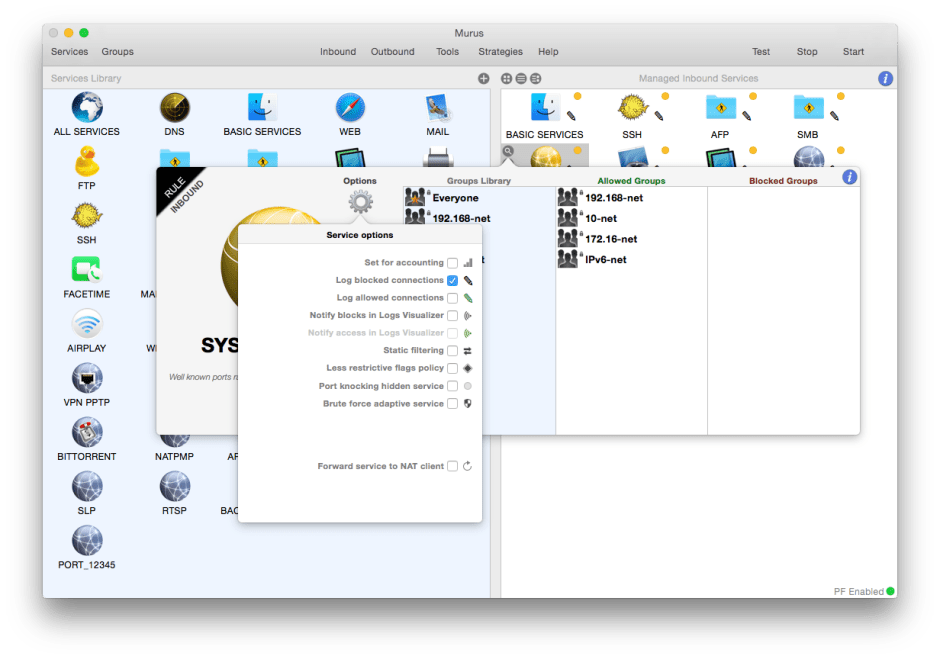
Normally you are better off using a good firewall built into your modem-router and leaving your Mac’s firewall turned off, but if you wish to tighten security then managing your Mac’s PF using Murus Pro is a sound choice.
Those who connect to the Internet from various sites which may not enjoy good firewall protection should enable that on their Mac, preferably using Murus Pro, which can also be used to watch for intrusions that make it past the outer firewall, in lieu of a NIDS.
Updated from the original, which was first published in MacUser volume 29 issue 02, 2013.
