How should you protect documents containing sensitive information from loss or theft?
Many of us now have to take sensitive data, particularly those covered by the Data Protection Act and its equivalents in other jurisdictions, out of the office. If you fear the wrath of those laws, and the humiliation that would accompany loss or theft of those data, you must take robust and defensible measures to protect them.
Drop the personal identifiers
The best answer is to strip out all personal information. You clearly cannot do this when that personal information is the whole purpose of the data, so client lists and the like are not suitable for this approach. However many data collections that have been lost or stolen contained unnecessary identifiers.
See if you can work with a subset of the original database in which serial numbers replace personal identifiers, or even better use a one-way anonymisation scheme based on hash keys such as SHA1 or its successors. Implemented properly these provide complete protection, still allowing you to add further data.
Change human behaviour
Next you must change human behaviour to prevent data loss from occurring. When travelling with a laptop, are you always meticulous about checking that you take it with you rather than leaving it unattended and unsecured?
Do you store memory sticks in secure compartments with the same care that you take over your wallet/purse and keys? Before leaving your hotel room or train, do you check every item of baggage, or are you distracted by your iPhone?
Beware of encryption
Encryption can be potent protection when you must move sensitive data around, as a fallback from human error or criminal actions. If your hotel room is burgled when you are in the bar, for example, it can limit resulting damage. But do not let encryption put the data at risk, either changing your behaviour through risk compensation, or using an encryption technique that is vulnerable, ineffective, or flawed.
Risk compensation is adjustment of behaviour to offset the protection offered by safety devices such as anti-lock brakes or cycle helmets, and may account for some problems experienced by organisations with poor records of data protection.
Organisations with problems often consider that the only way to ensure that data are properly protected is to force users to store files on encrypted media, such as encrypted hard disks or memory sticks. In practice, low-level encryption can also greatly increase the risk of loss of access to the data.
When implemented in firmware, in a special encrypted hard disk, for example, it is usually very reliable indeed. However as whole-disk encryption is most commonly implemented in software, outside the storage device controller, it is vulnerable to bugs and the devastating consequences of disk errors. Some widely used commercial products have poor compatibility, and do not appear to be sufficiently reliable for use.
Encrypting only the sensitive data
If you cannot use expensive firmware encryption, you are normally much better off storing sensitive information in encrypted files such as disk images, the same basic technique that Apple uses to implement File Vault. Disk images have the advantage that OS X knows how to decrypt and mount them automatically, integrating them seamlessly into your workflow. Good compression tools and third-party encryption apps can approach the same level of convenience.
However there is a significant risk that those tools might decrypt the file onto your hard disk, either leaving it there unencrypted for anyone to find, or once when it has been deleted a determined thief still may be able to recover some or all of the data.
Beware of closed, proprietary products which make extravagant claims. Federal Information Processing Standards (FIPS) compliance may mean little more than the use of an encryption algorithm that is widely accepted, and is no general guarantee of security.
Using Encrypted Disk Images
Disk Utility can readily create and modify encrypted disk images which should be impervious to all but national security agencies – provided that you use robust passwords which are stored securely. From the File menu, choose the New Blank Disk Image… command, and set the dialog up to your liking.
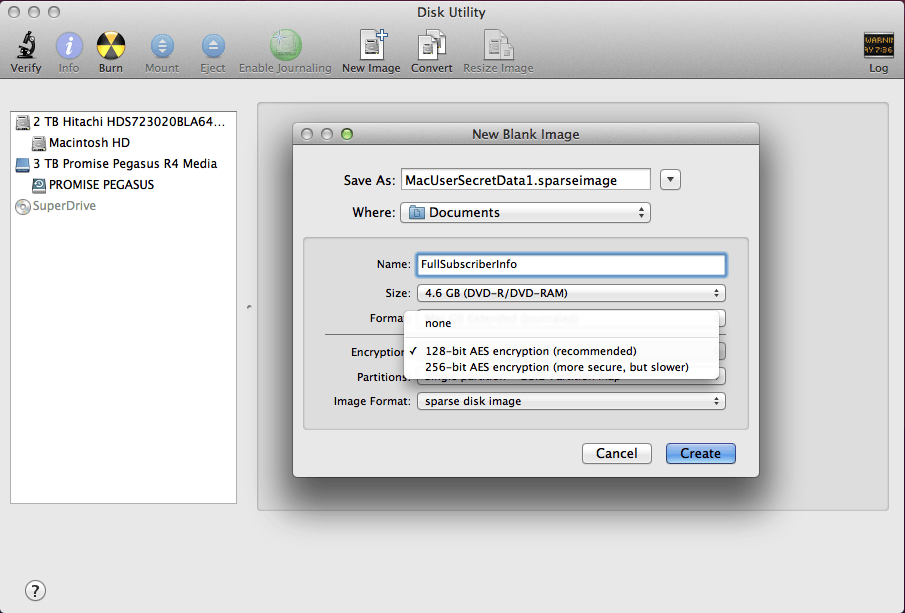
Using 128-bit AES as the encryption method should be ample for normal purposes, but if the contents are particularly sensitive and could readily fall into determined hands, 256-bit is more bombproof.
Before Disk Utility can create and save the disk image, you have to enter a new password. Its strength is shown, helping you to construct something suitably protective. However if you accept the default for this to be stored in your keychain, your protection will only be as strong as its weakest link, which will probably be your user password, protecting the keychain.
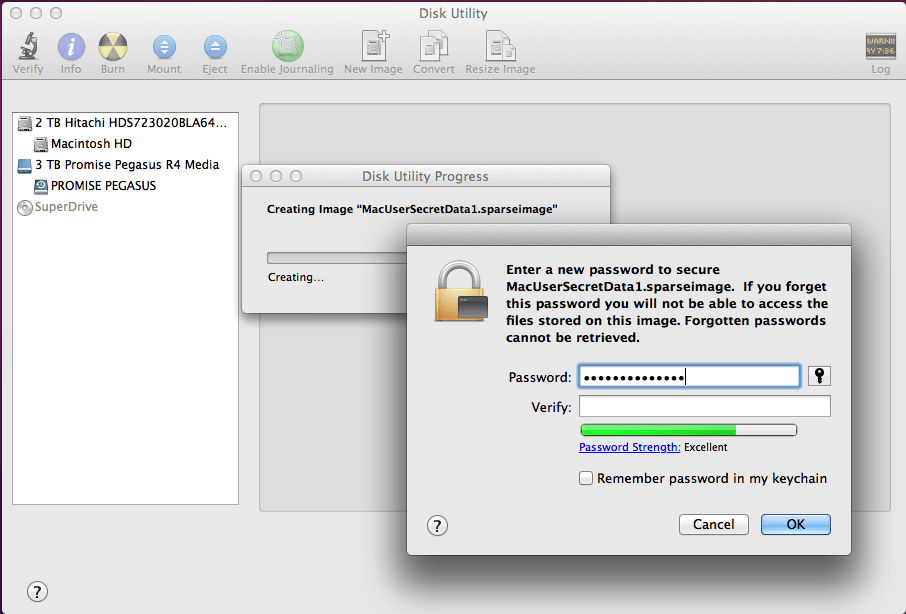
This can be further weakened if you are careless enough to write either password down and keep that on a note on your screen, or in the same bag as a laptop, for instance. Although it is essential to have a backup record, keep that completely separate from your Mac and storage devices, preferably sealed away.
Updated from the original, which was first published in MacUser volume 29 issue 11, 2013.
