There is no cause for panic, but in case you missed my recent articles (here and here) about Patrick Wardle’s work on ‘dylib hijacking’, OS X security has just changed. Very significantly.
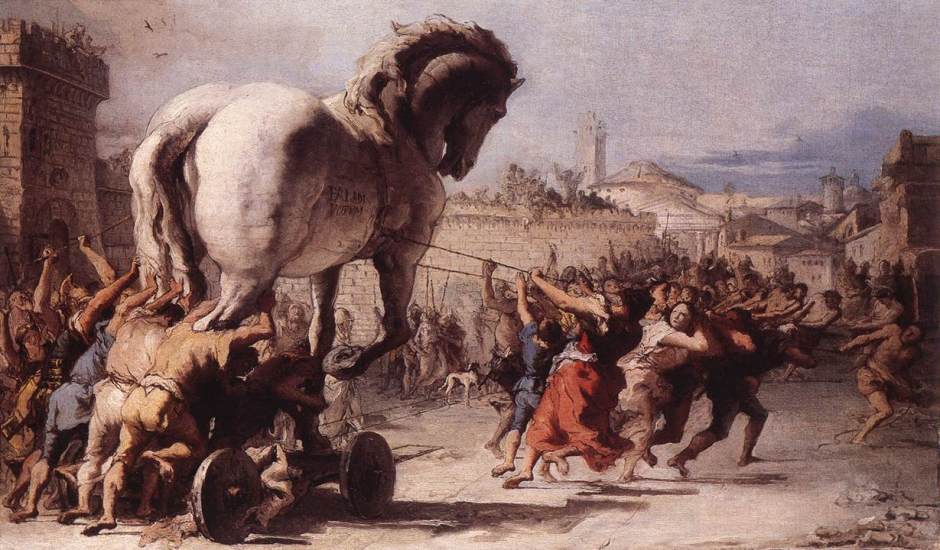
Since it first came out, OS X’s greatest threat in security terms has been a trojan horse attack, in which you are tricked into putting an app or similar onto your Mac, thinking that it is something beneficial or proper, only to find that it is malware.
Apple has provided a number of tools and features which try to prevent this. For over three years, since its introduction with Lion, the centre of this has been Gatekeeper, which decides whether a newly-installed app (and some other types of software) can be run. Controlled in the General tab of the Security & Privacy pane, most users set it to allow apps downloaded from the Mac App Store (most secure), or that and identified developers (on the second notch).
This forces a check on a special signature tucked away in the app. If the signature is missing or incorrect, OS X will refuse to run it, and potentially protect you from a Trojan or other malware. You can still manually override the check, of course, but that is quite a deliberate move and not something done routinely. When the app has been opened once, it is no longer checked by Gatekeeper, and will continue to open thereafter as normal.
Patrick Wardle has now shown how Gatekeeper’s protection can be bypassed without your knowing, so that it is now possible for an attacker to get malicious software onto a Mac running the current release of Yosemite, complete with its latest security updates.
The most likely scenario remains the classic trojan, in which human weakness is exploited, and you are lured to download something that you should not. However, as there is now a way in which an attacker can sneak this past Gatekeeper, you should not rely on Gatekeeper to protect you from your own folly.
Lesson 1: You cannot leave Gatekeeper to do the thinking and watching for you. Be very certain that you never download any malware. This is up to you, not OS X.
However Wardle has also drawn attention to a far more clever form of attack, in which even the most wary and cautious user could be caught.
Many app delivery and update services, like the Mac App Store, use secure connections to ensure that what you download from them cannot be tampered with in any way. Of course someone could always hijack the App Store, but that is a major undertaking which would be a fairly extensive catastrophe. Hopefully Apple has plenty of folk working night and day to ensure that their Stores remain secure and trustworthy. However it is worth noting that any new vulnerability in the secure connections that these rely on would have an even greater consequence.
However we also – all of us – download apps, updates, and other executable code over non-secure connections, like the web’s regular protocol, HTTP. These are all susceptible to tampering. Cunning and skilled attackers have used this ‘man in the middle’ method in the past. Breaking into a secure connection is very difficult; breaking into non-secure connections such as HTTP is a breeze. Wardle’s entirely correct conclusion is that, until this loophole in Gatekeeper is fixed by Apple, downloading any form of executable code – app, update, plug-in, etc. – puts you at risk, even when you can trust its source completely unless your connection is fully secured.
Lesson 2: Download any type of executable code via a non-secure connection, and you are now at significant risk of attack.
In an ideal world, the simple answer is not to download anything iffy using non-secure connections such as HTTP. However that remains the most popular means by which apps etc. are delivered and updated, outside secure services such as the App Store.
Is there anything else that we can do to protect ourselves? Wardle found that current releases of anti-virus products were unable to detect his bypassing Gatekeeper. Expect a flurry of activity among their vendors to introduce improved protection. However I would not recommend that you rely on such protection when it becomes available. If Apple can fix Gatekeeper to close this loophole, then that should help us all sleep easier.
If you are a software vendor, you clearly need to provide a secure delivery service now. If you are a user, then please be very very careful.
