Notarization is now much simpler than it was earlier, but can still play strange tricks on you. Take the example of an old app, Patrick Wardle’s KextViewr, which was last built in April 2016, four years ago. Patrick, its developer, was most surprised the other day to discover that it’s now notarized.
Notarization wasn’t introduced until June 2018, with the first beta-release of Mojave at WWDC. Patrick hasn’t submitted it for notarization, so how come it now shows up as having been checked by Apple for malicious software and opens fine in Catalina? Has Apple been busy notarizing old apps without informing their developers?
None of us knows who has been notarizing such old apps, but someone has definitely done so, and this isn’t the first time I’ve heard the same from a developer. But this wasn’t notarization as we now know it.
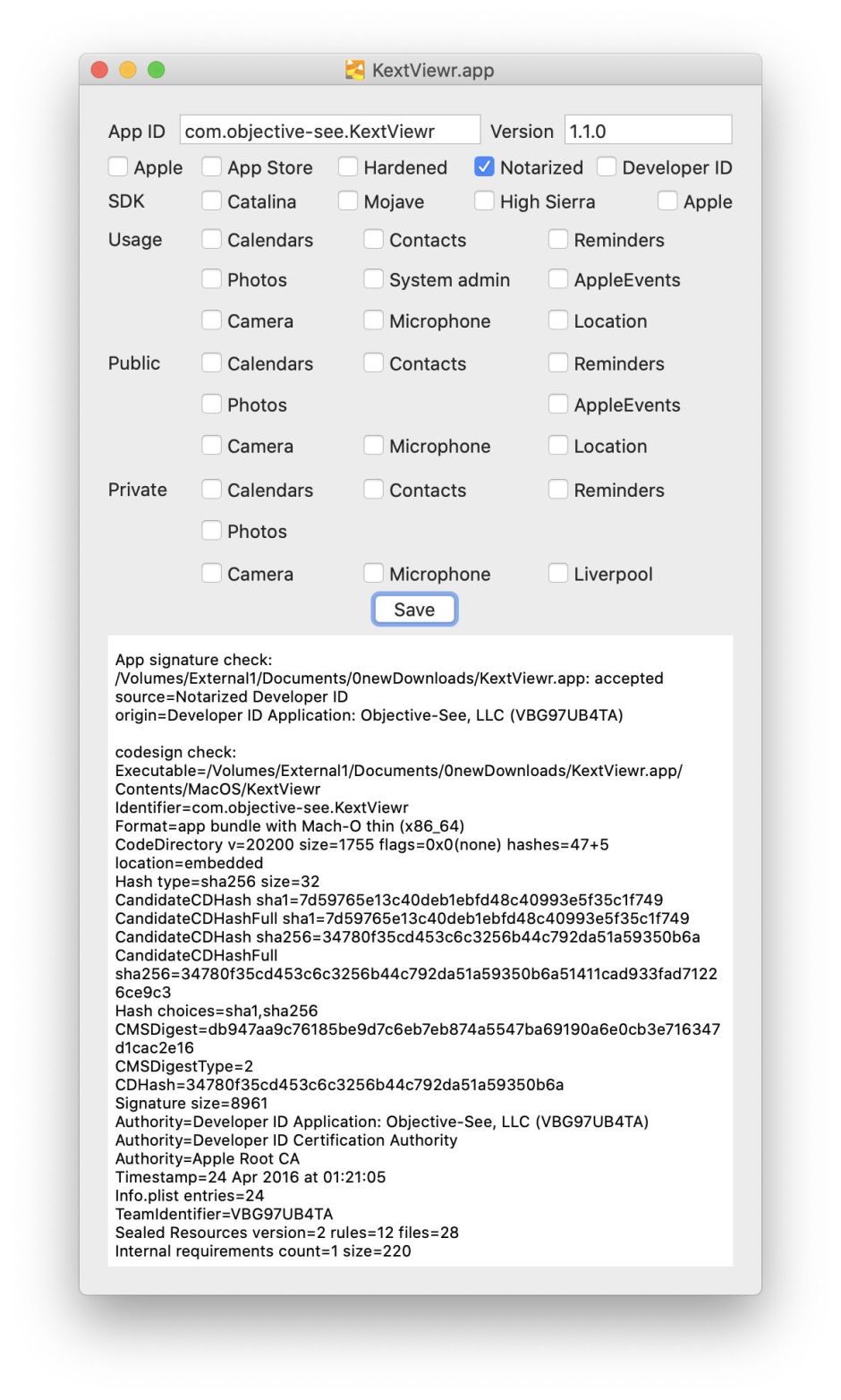
Use any tool, such as my free Taccy, which checks signing and notarization, and you’ll see that this app is properly notarized, and was signed correctly using Patrick’s developer certificate. However, as the top row of checkboxes shows, it isn’t hardened, or even built using a version of the SDK which is capable of notarization.
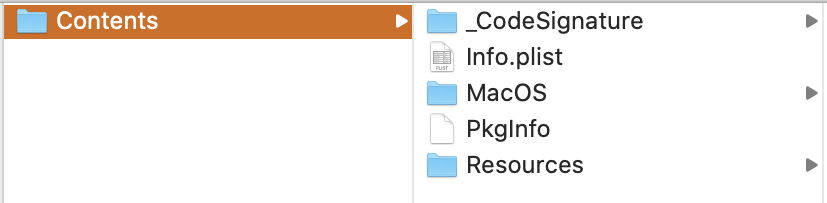
Look inside the app, though, and there’s no sign of the tell-tale CodeResources file which gets inserted when the notarization ticket is stapled to the app.
What has happened here is that someone has had this app notarized under legacy rules, or during the amnesty period which applied from the release of Catalina until February of this year. It’s a genuine notarization, but a bit different.
Despite developers being given advance notice of more than a year before Catalina made it a requirement, Apple seemed to have problems with compliance. The first scheme it offered to ease the transition allowed developers to submit existing apps and software for notarization under legacy rules. This was intended to ensure that there was an easy route to notarizing your current and recent products without having to bring them to full compliance with the strict rules, rebuild and submit them for checking.
When Catalina shipped in October 2019, a lot of major developers had still failed to ship properly notarized versions of their apps. Without warning, Apple suddenly relaxed the requirements for notarization, allowing newly notarized software to not comply with its strict rules. For example, it was no longer necessary for an app to be hardened at all: so long as it was submitted to Apple’s Notary Service and passed its tests for malware, it was awarded notarization. Those of us who had dutifully been notarizing everything under the previous strict rules were unimpressed that other developers suddenly had a free pass.
In February 2020, the rules reverted to require full conformance with the original rules which had been announced in June 2018, at last, and as far as I’m aware that’s the way they have remained ever since.
Patrick’s KextViewr app was notarized on 31 August 2019, and doesn’t comply with the strict rules, as it isn’t even hardened, so must have been submitted under the original legacy rules. So while it has been checked by Apple for malware, it doesn’t benefit from the protection afforded by hardening. But how come someone other than its developer got it notarized?
Anyone with a Developer ID can apparently get any app which satisfies current rules notarized. There isn’t, and never has been, any requirement that only the developer who signs the app can get it notarized. Indeed, Apple has commended this ‘feature’ to enterprise and other large-scale users. If they depend on an app which hasn’t been notarized, and need to install it on multiple Catalina systems, they’re perfectly entitled to submit it to Apple’s Notary Service. When that happens, the notification and email confirming that notarization has been successful are sent not to the original developer, but to the developer who submits the software for notarization. So the original developer will probably be completely unaware that this has happened.
The tell-tale here is the fact that whoever had Patrick’s app notarized didn’t staple the notarization ticket to the app. That’s why you can’t see it inside. Instead, when Catalina puts it through a full Gatekeeper check, it checks with Apple whether the app has been notarized but has no stapled ticket. In this case, Apple’s security servers responded that the app did have a notarization ticket, and Catalina was therefore perfectly happy to open it.
Although strange, I’ve been unable to think of any good security reason why this system shouldn’t be fine. Can you?
